source: http://www.securityfocus.com/bid/1525/info
In February of 2000 CERT Coordination Center released an advisory titled "Malicious HTML Tags Embedded in Client Web Requests" (advisory attached in 'Credit' section"). This advisory was a joint release by the CERT Coordination Center, DoD-CERT, the DoD Joint Task Force for Computer Network Defense (JTF-CND), the Federal Computer Incident Response Capability (FedCIRC), and the National Infrastructure Protection Center (NIPC). The point of the advisory in essence was a warning about client side vulnerabilities brought about by malicious scripting from Rogue websites which could be exploited to run code on client side browsers (acting as unwary interpreters for the scripting in question).
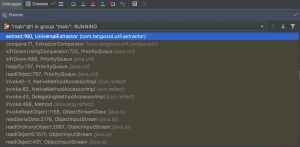
A number of webserver have suffered from this problem including 'Weblogic' from BEA Systems. In this particular case if a user can upload text in the form of JSP or JHTML code to the webserver (possibly via a web form etc.) a malicious end user might execute this code.
" Assume that there is an application on the WebLogic server that writes user entered data to a file called "temp.txt".
Given below is JHTML/JSP code that will print "Hello World":
<java>out.println("Hello World");</java> (JHTML) -or-
<% out.println("Hello World"); %> (JSP)
If this code is somehow inserted in the file "temp.txt" via an application, then the following can be used to invoke forced compilation and execution of "temp.txt":
http://weblogic.site/*.jhtml/path/to/temp.txt (JHTML)
-or-
http://weblogic.site/*.jsp/path/to/temp.txt "
![图片[1]-BEA WebLogic Java JHTML代码编译执行漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号
CVE编号
![图片[2]-BEA WebLogic Java JHTML代码编译执行漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID
CNNVD-ID










![[云筏测评系列] NAT-EU 9元服务器 by archlinux-安全小百科](https://aqxbk.com/wp-content/uploads/2021/08/frc-2d6dd61f98a70c4529220ebc07f363d6-277x300.png)








恐龙抗狼扛8月前0
kankan啊啊啊啊3年前0
66666666666666