2019年5月15日,微软官方发布5月安全补丁更新共修复了82个漏洞,其中包含一个针对远程桌面服务(RDP)的远程代码执行漏洞(编号为CVE-2019-0708 ),攻击者可以利用此漏洞远程发送构造特殊的恶意数据在目标系统上执行恶意代码,无需用户验证即可以实现目标机器的完全控制权。
此漏洞影响Windows XP、Window 2003、Windows 7、Window Server 2008系列操作系统。由于该漏洞影响及危害巨大,根据微软安全响应中心( MSRC )发布的博客文章提醒该漏洞有被蠕虫病毒利用再次导致WannaCry类似全球事件可能。
随后知道创宇404实验室及产品相关团队第一时间发布了漏洞预警及解决方案并密切关注该漏洞利用演变及进展,目前可确定部分安全研究机构及个人宣称已经复现并实现了远程真实利用程序。在此,我们再次预警提醒广大用户注意防御,及时更新修复该漏洞规避安全风险。
漏洞影响:
受影响系统及版本
● Windows 7 for 32-bit Systems Service Pack 1
● Windows 7 for x64-based Systems Service Pack 1
● Windows Server 2008 for 32-bit Systems Service Pack 2
● Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
● Windows Server 2008 for Itanium-Based Systems Service Pack 2
● Windows Server 2008 for x64-based Systems Service Pack 2
● Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
● Windows Server 2008 R2 for Itanium-Based Systems Service Pack 1
● Windows Server 2008 R2 for x64-based Systems Service Pack 1
● Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
需要注意的是: Windows 8 和 Windows 10 及之后版本的用户不受此漏洞影响。
网络空间影响:
知道创宇旗下网络空间搜索引擎ZoomEye 通过 app:”Microsoft Terminal Service” 查询到,截至目前全球有7,824,306条微软远程桌面服务对外开放的记录,主要分布在美国(2093963)及中国(1777045):

解决方案
漏洞检测方案:
1、目前知道创宇SeeBug漏洞平台推出了基于PocSuite框架的漏洞远程无害扫描检测程序(免费):https://www.seebug.org/vuldb/ssvid-97954。

2、使用知道创宇网络空间安全资产管理系统ZoomEye BE 进行内部资产普查及时发现并修复漏洞。

漏洞修复及拦截方案:
1、参考微软官方安全通告下载并安装最新补丁:
https://support.microsoft.com/zh-cn/help/4500705/customer-guidance-for-cve-2019-0708
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0708
补丁下载链接:
● Windows 7 x86
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-x86_6f1319c32d5bc4caf2058ae8ff40789ab10bf41b.msu
● Windows 7 x64
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-x64_3704acfff45ddf163d8049683d5a3b75e49b58cb.msu
● Windows Embedded Standard 7 for x64
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-x64_3704acfff45ddf163d8049683d5a3b75e49b58cb.msu
● Windows Embedded Standard 7 for x86
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-x86_6f1319c32d5bc4caf2058ae8ff40789ab10bf41b.msu
● Windows Server 2008 x64
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.0-kb4499149-x64_9236b098f7cea864f7638e7d4b77aa8f81f70fd6.msu
● Windows Server 2008 Itanium
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.0-kb4499180-ia64_805e448d48ab8b1401377ab9845f39e1cae836d4.msu
● Windows Server 2008 x86
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.0-kb4499149-x86_832cf179b302b861c83f2a92acc5e2a152405377.msu
● Windows Server 2008 R2 Itanium
http://download.windowsupdate.com/c/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-ia64_fabc8e54caa0d31a5abe8a0b347ab4a77aa98c36.msu
● Windows Server 2008 R2 x64
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/05/windows6.1-kb4499175-x64_3704acfff45ddf163d8049683d5a3b75e49b58cb.msu
● Windows Server 2003 x86
http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsserver2003-kb4500331-x86-custom-chs_4892823f525d9d532ed3ae36fc440338d2b46a72.exe
● Windows Server 2003 x64
http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsserver2003-kb4500331-x64-custom-chs_f2f949a9a764ff93ea13095a0aca1fc507320d3c.exe
● Windows XP SP3
http://download.windowsupdate.com/c/csa/csa/secu/2019/04/windowsxp-kb4500331-x86-custom-chs_718543e86e06b08b568826ac13c05f967392238c.exe
● Windows XP SP2 for x64
http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsserver2003-kb4500331-x64-custom-enu_e2fd240c402134839cfa22227b11a5ec80ddafcf.exe
● Windows XP SP3 for XPe
http://download.windowsupdate.com/d/csa/csa/secu/2019/04/windowsxp-kb4500331-x86-embedded-custom-chs_96da48aaa9d9bcfe6cd820f239db2fe96500bfae.exe
● WES09 and POSReady 2009
http://download.windowsupdate.com/d/msdownload/update/software/secu/2019/04/windowsxp-kb4500331-x86-embedded-chs_e3fceca22313ca5cdda811f49a606a6632b51c1c.exe
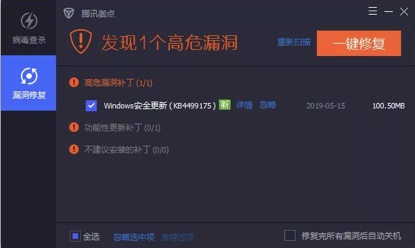
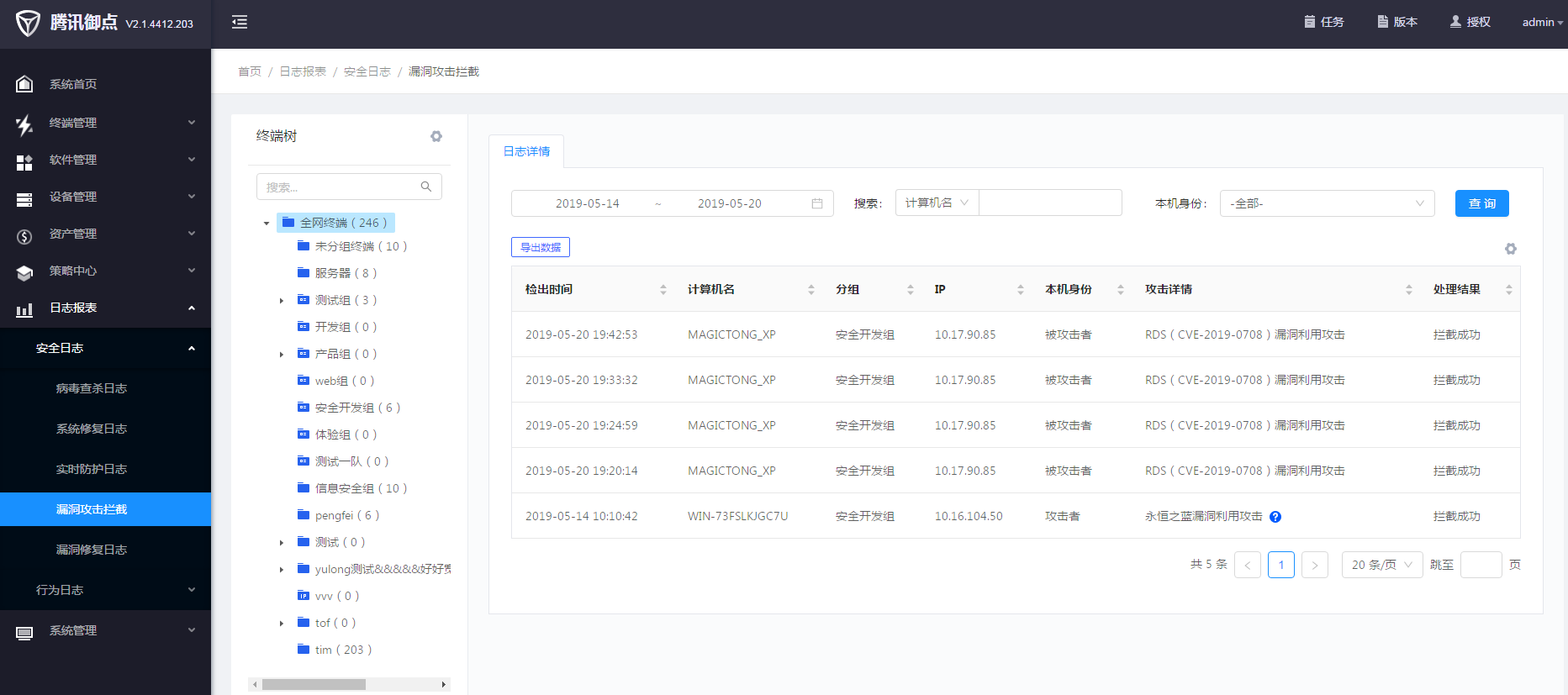
2、启用知道创宇联合腾讯研发的终端安全产品:御点终端安全管理系统,提供一键修复、针对没办法打补丁重启的设备并提供无补丁漏洞防御。
如有更多疑问,可向知道创宇寻求技术支持,联系电话:400-060-9587





















请登录后发表评论
注册